Key monetary and coverage providers positioned in French-speaking nations in Africa have been focused around the previous two decades as aspect of a persistent destructive marketing campaign codenamed DangerousSavanna.
Nations qualified include things like Ivory Coast, Morocco, Cameroon, Senegal, and Togo, with the spear-phishing attacks intensely concentrating on Ivory Coastline in the latest months, Israeli cybersecurity organization Test Position said in a Tuesday report.
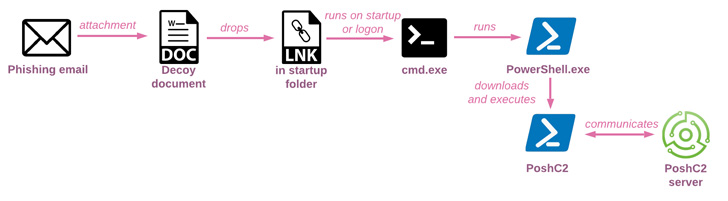
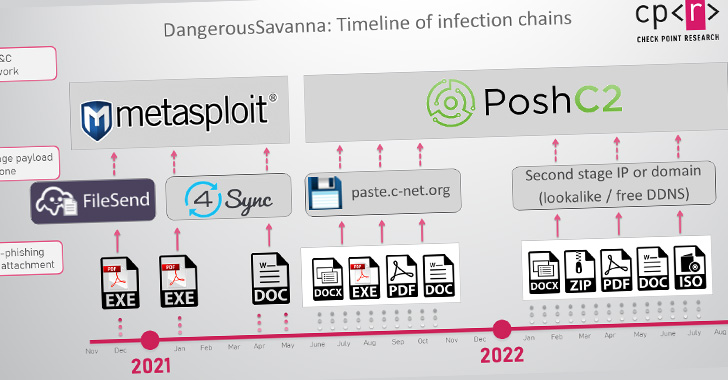
Infection chains entail concentrating on workforce of financial institutions with social engineering messages that contains malicious attachments as a indicates of initial obtain, in the long run foremost to the deployment of off-the-shelf malware these types of as Metasploit, PoshC2, DWservice, and AsyncRAT.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

“The risk actors’ creative imagination is on display in the preliminary an infection stage, as they persistently go after the employees of the specific businesses, continuously switching infection chains that use a huge variety of destructive file types, from self-penned executable loaders and malicious documents, to ISO, LNK, JAR and VBE data files in various combos,” the enterprise reported.
The phishing e-mail are written in French and despatched making use of Gmail and Hotmail services, with the messages also impersonating other financial institutions in Africa to enhance their trustworthiness.
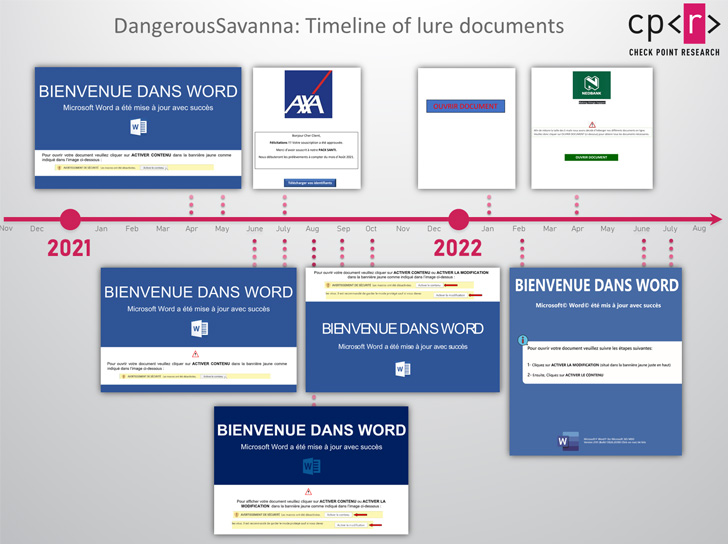
Whilst attacks in 2021 leveraged macro-laced Microsoft Phrase paperwork as lures, the company’s final decision to block macros in information downloaded from the internet by default previously this year has led the DangerousSavanna actors to pivot to PDF and ISO files.
Also, the very first wave of attacks from the stop of 2020 to the commencing of 2021 concerned the use of bespoke .NET-based mostly applications, which came disguised as PDF data files attached to phishing e-mails, to retrieve upcoming-stage droppers and loaders from distant servers.

Regardless of the system made use of, article-exploitation things to do carried out after acquiring an initial foothold include creating persistence, doing reconnaissance, and providing supplemental payloads to remotely handle the host, get rid of anti-malware procedures, and log keystrokes.
The exact provenance of the danger actor remains unclear, but the regular change in its resources and techniques demonstrates their information of open-supply application and their skill to good-tune their practices for maximizing economical gain.
“If 1 infection chain didn’t get the job done out, they adjusted the attachment and the lure and tried targeting the very same business once again and yet again hoping to uncover an entry stage,” Verify Issue mentioned. “With social engineering by way of spear-phishing, all it requires is a single incautious simply click by an unsuspecting user.”
Located this short article exciting? Stick to THN on Fb, Twitter and LinkedIn to read through extra special content we submit.
Some components of this article are sourced from:
thehackernews.com

 Microsoft Warns of Ransomware Attacks by Iranian Phosphorus Hacker Group
Microsoft Warns of Ransomware Attacks by Iranian Phosphorus Hacker Group