A North Korean authorities-backed marketing campaign focusing on cybersecurity researchers with malware has re-emerged with new strategies in their arsenal as part of a refreshing social engineering attack.
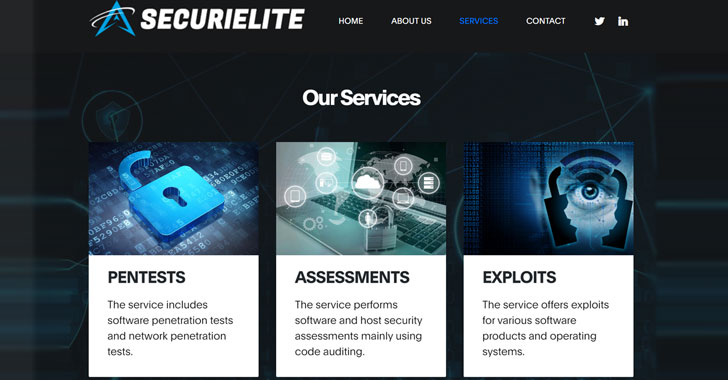
In an update shared on Wednesday, Google’s Threat Assessment Team said the attackers powering the operation established up a bogus security business called SecuriElite and a slew of social media accounts throughout Twitter and LinkedIn in an endeavor to trick unsuspecting scientists into going to the firm’s booby-trapped site “where a browser exploit was waiting around to be brought on.”
“The new web-site claims the corporation is an offensive security corporation found in Turkey that delivers pentests, application security assessments and exploits,” TAG’s Adam Weidemann claimed. The web-site is claimed to have long gone stay on March 17.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
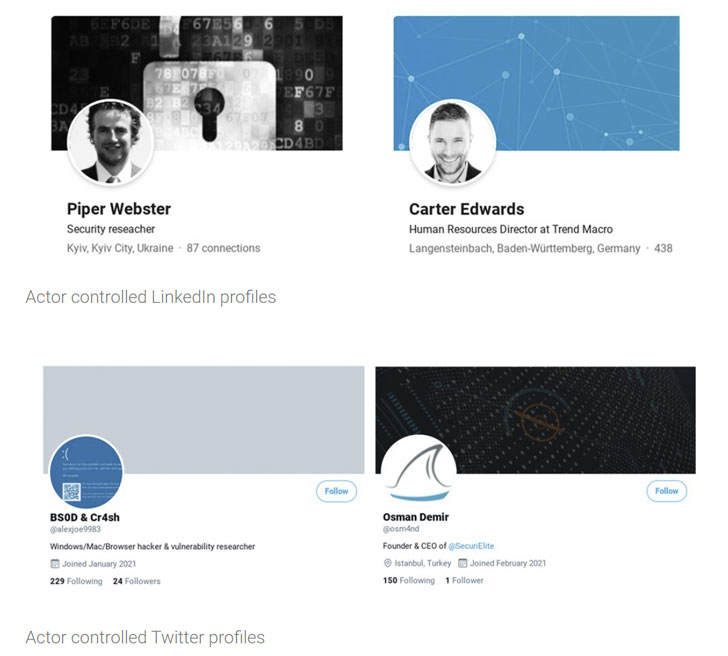
A total of 8 Twitter profiles and seven LinkedIn profiles, who claimed to be vulnerability scientists and human sources staff at different security firms (such as Trend Macro, influenced by Craze Micro), ended up developed for this goal, with a several many others posing as the main government officer and personnel at the fictitious business. All the accounts have because been suspended.
The campaign was to begin with flagged by TAG in January 2021, when it came to light that the adversary had developed a investigate website and many profiles on numerous social media platforms these kinds of as Twitter, LinkedIn, Telegram, Discord, and Keybase in a bid to communicate with the researchers and construct belief, only to deploy a Windows backdoor that came in the variety of a trojanized Visual Studio Venture.
Subsequent the disclosure, researchers from South Korean cybersecurity agency ENKI discovered a zero-working day in Internet Explorer that it stated authorized the hackers to obtain the gadgets managed by its security staff with destructive MHTML information. Microsoft later addressed the issue in its Patch Tuesday update for March 2021.
As a precaution, Google has added the website’s URL to its Safebrowsing blocklist service to avert accidental visits, even however the web page has not been located to serve any malicious content material.
If something, the most current improvement is nonetheless an additional illustration of attackers immediately shifting gears when their methods are discovered and uncovered publicly.
The genuine motive driving the attacks continues to be unclear as but, even though it’s becoming suspected that the risk actor may well be attempting to stealthily gain a foothold on techniques in buy to get hold of zero-day study, and in the course of action, use individuals unpatched vulnerabilities to stage even more attacks on vulnerable targets of their alternative.
Identified this post exciting? Follow THN on Fb, Twitter and LinkedIn to study far more special written content we publish.
Some parts of this write-up are sourced from:
thehackernews.com

 National infrastructure plan could strain CISA despite modernizing systems
National infrastructure plan could strain CISA despite modernizing systems