Microsoft has disclosed details of an evasive yr-long social engineering campaign whereby the operators stored changing their obfuscation and encryption mechanisms every 37 days on regular, including relying on Morse code, in an attempt to protect their tracks and surreptitiously harvest consumer credentials.
The phishing attacks get the type of bill-themed lures mimicking monetary-linked company transactions, with the emails that contains an HTML file (“XLS.HTML”). The supreme objective is to harvest usernames and passwords, which are subsequently used as an original entry point for later on infiltration attempts.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Microsoft likened the attachment to a “jigsaw puzzle,” noting that individual pieces of the HTML file are made to surface innocuous and slip previous endpoint security software program, only to expose its true colours when these segments are decoded and assembled jointly. The company did not establish the hackers guiding the operation.
“This phishing campaign exemplifies the present day email danger: innovative, evasive, and relentlessly evolving,” Microsoft 365 Defender Risk Intelligence Workforce explained in an investigation. “The HTML attachment is divided into various segments, which include the JavaScript files utilised to steal passwords, which are then encoded utilizing numerous mechanisms. These attackers moved from employing plaintext HTML code to using multiple encoding approaches, like aged and unusual encryption strategies like Morse code, to hide these attack segments
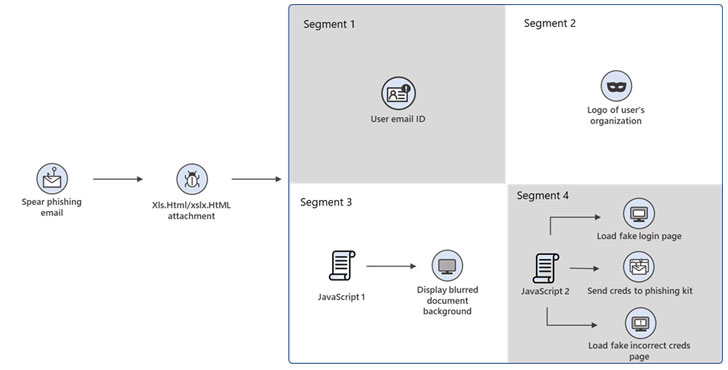
Opening the attachment launches a browser window that displays a bogus Microsoft Place of work 365 credentials dialog box on best of a blurred Excel doc. The dialog box reveals a concept urging the recipients to signal in once more thanks to factors that their accessibility to the Excel doc has purportedly timed out. In the party the person enters the password, the particular person is alerted that the typed password is incorrect, although the malware stealthily harvests the data in the qualifications.

The campaign is said to have been through 10 iterations since its discovery in July 2020, with the adversary periodically switching up its encoding solutions to mask the destructive character of the HTML attachment and the distinct attack segments contained within the file.
Microsoft said it detected the use of Morse code in the attacks’ February and May 2021 waves, though afterwards variants of the phishing kit were located to immediate the victims to a legit Business office 365 site in its place of showing a phony mistake message once the passwords have been entered.
“Email-primarily based attacks carry on to make novel attempts to bypass email security options,” the researchers mentioned. “In the scenario of this phishing campaign, these attempts contain using multilayer obfuscation and encryption mechanisms for recognised existing file forms, these types of as JavaScript. Multilayer obfuscation in HTML can likewise evade browser security answers.
Discovered this post fascinating? Stick to THN on Fb, Twitter and LinkedIn to read more unique information we post.
Some components of this write-up are sourced from:
thehackernews.com


 “Great resignation” sparks concern over insider data leaks
“Great resignation” sparks concern over insider data leaks