Due to the fact at the very least late 2019, a network of hackers-for-seek the services of have been hijacking the channels of YouTube creators, luring them with bogus collaboration possibilities to broadcast cryptocurrency scams or offer the accounts to the optimum bidder.
That’s in accordance to a new report published by Google’s Threat Examination Team (TAG), which mentioned it disrupted financially motivated phishing strategies targeting the video platform with cookie theft malware. The actors at the rear of the infiltration have been attributed to a team of hackers recruited in a Russian-talking discussion board.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“Cookie Theft, also identified as ‘pass-the-cookie attack,’ is a session hijacking technique that permits accessibility to user accounts with session cookies saved in the browser,” TAG’s Ashley Shen reported. “When the strategy has been close to for many years, its resurgence as a leading security risk could be because of to a broader adoption of multi-factor authentication (MFA) creating it hard to perform abuse, and shifting attacker focus to social engineering methods.”
Given that May possibly, the internet giant mentioned it has blocked 1.6 million messages and restored almost 4,000 YouTube influencer accounts influenced by the social engineering marketing campaign, with some of the hijacked channels marketing for anyplace involving $3 to $4,000 on account-trading marketplaces relying on the subscriber rely.
Other channels, in distinction, ended up rebranded for cryptocurrency ripoffs in which the adversary live-streamed films promising cryptocurrency giveaways in return for an initial contribution, but not prior to altering the channel’s name, profile photograph, and articles to spoof huge tech or cryptocurrency trade firms.
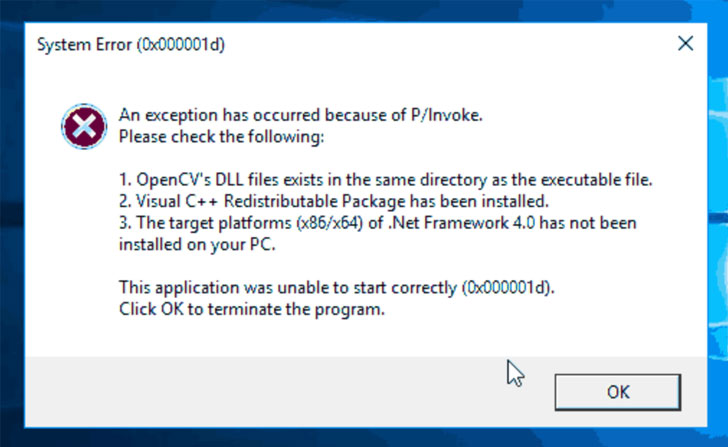
The attacks included sending channel owners a destructive hyperlink underneath the ruse of video ad collaborations for anti-virus application, VPN clientele, songs gamers, picture enhancing apps, or on the internet video games that, when clicked, redirected the recipient to a malware landing site, some of which impersonated legit computer software websites, these kinds of as Luminar and Cisco VPN, or masqueraded as media stores centered on COVID-19.
Google explained it located no less than 15,000 accounts powering the phishing messages and 1,011 domains that have been purpose-constructed to provide the fraudulent software package accountable for executing cookie stealing malware designed to extract passwords and authentication cookies from the victim’s device and upload them to the actor’s command-and-control servers.
The hackers would then use the session cookies to acquire control of a YouTube creator’s account, effectively circumventing two-factor authentication (2FA), as nicely as get measures to change passwords and the account’s recovery email and phone quantities.
Subsequent Google’s intervention, the perpetrators have been noticed driving targets to messaging apps like WhatsApp, Telegram, and Discord in an endeavor to get about Gmail’s phishing protections, not to point out transitioning to other email vendors like aol.com, email.cz, seznam.cz, and article.cz. End users are very encouraged to protected their accounts with two-factor authentication to prevent such takeover attacks.
Uncovered this short article attention-grabbing? Follow THN on Fb, Twitter and LinkedIn to read additional distinctive written content we publish.
Some components of this write-up are sourced from:
thehackernews.com


 Two Eastern Europeans Sentenced for Providing Bulletproof Hosting to Cyber Criminals
Two Eastern Europeans Sentenced for Providing Bulletproof Hosting to Cyber Criminals