A monetarily enthusiastic danger actor has been noticed deploying a earlier mysterious rootkit targeting Oracle Solaris units with the objective of compromising Automatic Teller Equipment (ATM) switching networks and carrying out unauthorized funds withdrawals at diverse financial institutions applying fraudulent cards.
Threat intelligence and incident reaction company Mandiant is monitoring the cluster below the moniker UNC2891, with some of the group’s tactics, techniques, and processes sharing overlaps with that of one more cluster dubbed UNC1945.
The intrusions staged by the actor involve “a substantial diploma of OPSEC and leverage both of those public and non-public malware, utilities, and scripts to eliminate proof and hinder reaction endeavours,” Mandiant researchers reported in a new report published this 7 days.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
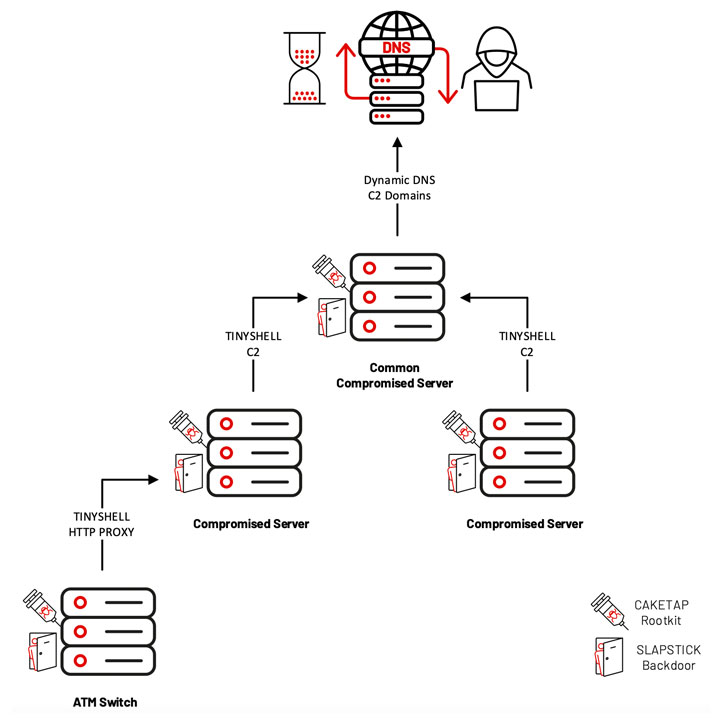
Even extra concerningly, the attacks spanned numerous years in some circumstances, during the entirety of which the actor remained undetected by leveraging a rootkit termed CAKETAP, which is built to conceal network connections, procedures, and documents.
Mandiant, which was equipped to get better memory forensic facts from a single of the victimized ATM change servers, noted that one particular variant of the kernel rootkit came with specialized attributes that enabled it to intercept card and PIN verification messages and use the stolen knowledge to execute fraudulent dollars withdrawals from ATM terminals.
Also set to use are two backdoors identified as SLAPSTICK and TINYSHELL, both equally attributed to UNC1945 and are employed to acquire persistent remote accessibility to mission-critical techniques as properly as shell execution and file transfers via rlogin, telnet, or SSH.
“In line with the group’s familiarity with Unix and Linux primarily based systems, UNC2891 generally named and configured their TINYSHELL backdoors with values that masqueraded as legitimate expert services that may be missed by investigators, these kinds of as systemd (SYSTEMD), title services cache daemon (NCSD), and the Linux at daemon (ATD),” the researchers pointed out.
On top of that, the attack chains have employed a selection of malware and publicly-readily available utilities, like –
- STEELHOUND – A variant of the STEELCORGI in-memory dropper which is utilised to decrypt an embedded payload and encrypt new binaries
- WINGHOOK – A keylogger for Linux and Unix dependent operating units that captures the knowledge in an encoded format
- WINGCRACK – A utility that is utilised to parse the encoded material generated by WINGHOOK
- WIPERIGHT – An ELF utility that erases log entries pertaining to a particular consumer on Linux and Unix primarily based units
- MIGLOGCLEANER – An ELF utility that wipes logs or get rid of sure strings from logs on Linux and Unix based devices
“[UNC2891] makes use of their talent and experience to get complete edge of the lowered visibility and security actions that are generally existing in Unix and Linux environments,” the researchers mentioned. “Whilst some of the overlaps in between UNC2891 and UNC1945 are notable, it is not conclusive ample to attribute the intrusions to a solitary risk team.”
Uncovered this report interesting? Follow THN on Fb, Twitter and LinkedIn to examine a lot more exclusive information we publish.
Some parts of this post are sourced from:
thehackernews.com




 Google Blows Lid Off Conti, Diavol Ransomware Access-Broker Ops
Google Blows Lid Off Conti, Diavol Ransomware Access-Broker Ops