Two newly uncovered malicious Android applications on Google Engage in Retail outlet have been utilized to focus on buyers of Brazil’s fast payment ecosystem in a possible try to entice victims into fraudulently transferring their whole account balances into yet another bank account underneath cybercriminals’ control.
“The attackers distributed two distinct variants of banking malware, named PixStealer and MalRhino, by two independent destructive applications […] to have out their attacks,” Examine Stage Investigate said in an assessment shared with The Hacker Information. “Both equally destructive apps were created to steal money of victims by means of user interaction and the authentic PIX software.”
The two applications in question, which have been uncovered in April 2021, have considering the fact that been removed from the application retail outlet.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Launched in November 2020 by the Central Bank of Brazil, the country’s financial authority, Pix is a point out-owned payments system that permits customers and providers to make income transfers from their lender accounts without necessitating debit or credit score playing cards.
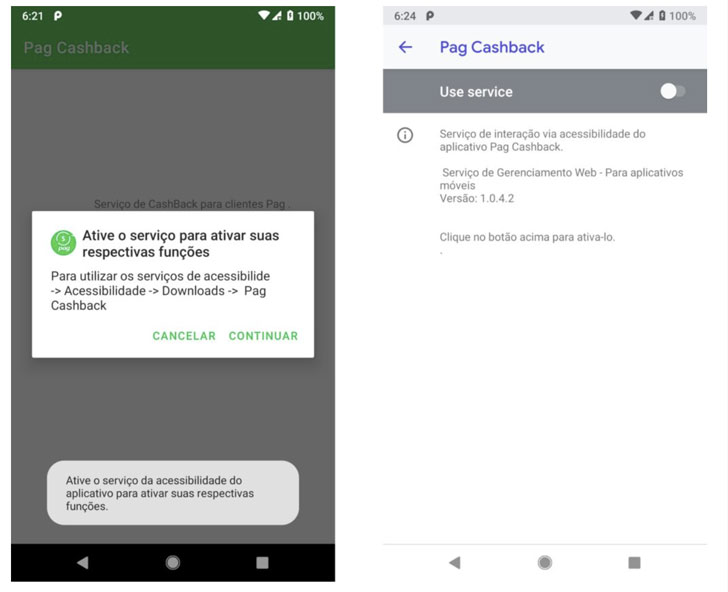
PixStealer, which was observed dispersed on Google Play as a fake PagBank Cashback provider application, is developed to empty a victim’s funds to an actor-managed account, even though MalRhino — masquerading as a cellular token application for Brazil’s Inter bank — will come with advanced features vital to accumulate the listing of installed apps and retrieve PIN for particular financial institutions.
“When a person opens their PIX bank software, Pixstealer displays the target an overlay window, where the user are unable to see the attacker’s moves,” the researchers explained. “Driving the overlay window, the attacker retrieves the offered total of revenue and transfers the revenue, frequently the full account stability, to one more account.”
What unites PixStealer and MalRhino is that equally the applications abuse Android’s accessibility assistance to execute malicious steps on the compromised gadgets, making them the most recent addition to a extensive listing of mobile malware that leverages the permission to perpetrate knowledge theft.

Specially, the fake overlay will come with a message “Synchronizing your access… Do not flip off your mobile monitor” when, in actuality, the malware searches for the “Transfer” button to perform the transfer working with a series of accessibility APIs.
The MalRhino variant also stands out for its use of Mozilla’s Java-dependent Rhino JS framework to operate JavaScript instructions inside of targeted banking programs, but not ahead of convincing the user to switch on accessibility expert services.
“This strategy is not generally utilised on cellular malware and demonstrates how destructive actors are receiving impressive to keep away from detection and get inside of Google Enjoy,” the researchers claimed. “With the expanding abuse of the Accessibility Company by cellular banking malware, consumers should really be wary of enabling the relevant permissions even in the purposes distributed by using regarded app shops these as Google Perform.”
Observed this post attention-grabbing? Comply with THN on Fb, Twitter and LinkedIn to go through far more exceptional content we put up.
Some parts of this write-up are sourced from:
thehackernews.com


 SolarWinds Attackers Develop New FoggyWeb Backdoor
SolarWinds Attackers Develop New FoggyWeb Backdoor