A new spear-phishing campaign is concentrating on experts on LinkedIn with weaponized position presents in an attempt to infect targets with a complex backdoor trojan called “additional_eggs.”
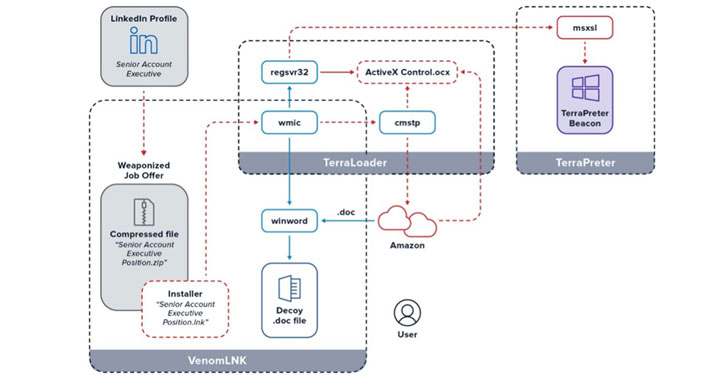
To raise the odds of good results, the phishing lures take gain of malicious ZIP archive information that have the same name as that of the victims’ occupation titles taken from their LinkedIn profiles.
“For instance, if the LinkedIn member’s work is detailed as Senior Account Executive—International Freight the destructive zip file would be titled Senior Account Executive—International Freight place (observe the ‘position’ added to the close),” cybersecurity firm eSentire’s Danger Response Device (TRU) explained in an examination. “Upon opening the bogus position supply, the target unwittingly initiates the stealthy set up of the fileless backdoor, much more_eggs.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Strategies delivering more_eggs using the similar modus operandi have been spotted at the very least given that 2018, with the backdoor attributed to a malware-as-a-company (MaaS) service provider referred to as Golden Chickens. The adversaries driving this new wave of attacks keep on being not known as however, despite the fact that far more_eggs has been put to use by several cybercrime groups such as Cobalt, FIN6, and EvilNum in the previous.
When mounted, additional_eggs maintains a stealthy profile by hijacking legit Windows procedures though presenting the decoy “employment software” document to distract targets from ongoing history jobs induced by the malware. Furthermore, it can act as a conduit to retrieve added payloads from an attacker-controlled server, this kind of as banking trojans, ransomware, credential stealers, and even use the backdoor as a foothold in the victim’s network so as to exfiltrate facts.
If everything, the latest advancement is still one more indicator of how menace actors are continually tweaking their attacks with individualized lures in an endeavor to trick unsuspecting consumers into downloading malware.
“Given that the COVID pandemic, unemployment fees have risen substantially. It is a best time to consider advantage of position seekers who are desperate to find work,” the scientists reported. “As a result, a tailored career entice is even far more attractive during these troubled situations.”
Located this article attention-grabbing? Stick to THN on Facebook, Twitter and LinkedIn to read through much more special written content we write-up.
Some pieces of this post are sourced from:
thehackernews.com

 Probing restrictions may stilt Pentagon’s vulnerability disclosure program for contractors
Probing restrictions may stilt Pentagon’s vulnerability disclosure program for contractors