Microsoft on Friday mentioned it can be investigating an incident whereby a driver signed by the organization turned out to be a malicious Windows rootkit that was observed speaking with command-and-control (C2) servers found in China.
The driver, referred to as “Netfilter,” is stated to concentrate on gaming environments, precisely in the East Asian place, with the Redmond-dependent organization noting that “the actor’s aim is to use the driver to spoof their geo-place to cheat the system and perform from any place.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“The malware enables them to achieve an benefit in game titles and probably exploit other players by compromising their accounts by means of widespread applications like keyloggers,” Microsoft Security Response Center (MSRC) reported.
The rogue code signing was noticed by Karsten Hahn, a malware analyst at German cybersecurity corporation G Information, who shared further details of the rootkit, together with a dropper, which is used to deploy and set up Netfilter on the procedure.
On thriving set up, the driver establishes connections with a C2 server to retrieve configuration information and facts, which delivers a quantity of functionalities these kinds of as IP redirection, amongst other capabilities to acquire a root certificate and even self-update the malware.
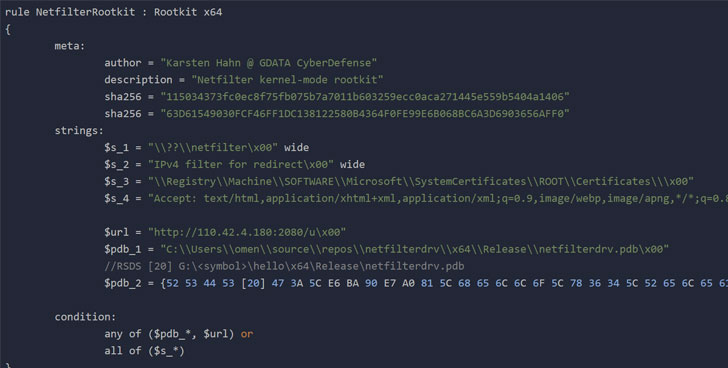
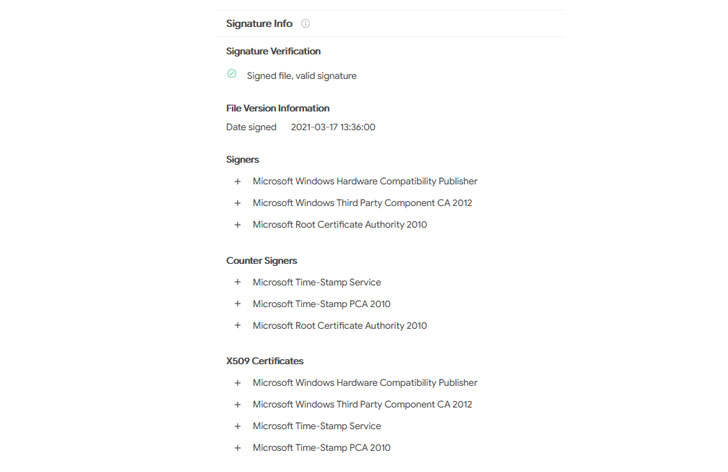
The oldest sample of Netfilter detected on VirusTotal dates back to March 17, 2021, Hahn claimed.

Microsoft famous that the actor submitted the driver for certification by way of the Windows Components Compatibility Program (WHCP), and that the drivers ended up crafted by a third-party. The firm has because suspended the account and reviewed its submissions for supplemental signals of malware.
The Windows maker also stressed that the approaches used in the attack come about put up-exploitation, which necessitates that the adversary ought to have experienced earlier gained administrative privileges so as to be in a position to install the driver during program startup or trick the user into carrying out it on their behalf.
Also, Microsoft explained it intends to refine its partner obtain insurance policies as very well as its validation and signing process to boost protections additional.
“The security landscape carries on to fast evolve as risk actors locate new and modern techniques to acquire obtain to environments across a vast vary of vectors,” MSRC explained, at the time again highlighting how respectable processes can be exploited by danger actors to facilitate large-scale application source chain attacks.
Found this posting exciting? Stick to THN on Fb, Twitter and LinkedIn to browse far more exclusive material we submit.
Some components of this article are sourced from:
thehackernews.com


 DMARC: The First Line of Defense Against Ransomware
DMARC: The First Line of Defense Against Ransomware