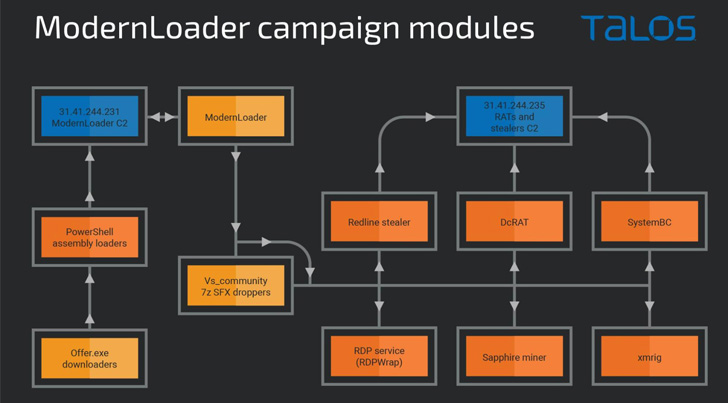
As quite a few as 3 disparate but connected strategies among March and Jun 2022 have been identified to deliver a variety of malware, including ModernLoader, RedLine Stealer, and cryptocurrency miners on to compromised methods.
“The actors use PowerShell, .NET assemblies, and HTA and VBS data files to spread across a targeted network, inevitably dropping other items of malware, such as the SystemBC trojan and DCRat, to permit various levels of their functions,” Cisco Talos researcher Vanja Svajcer explained in a report shared with The Hacker News.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The malicious implant in dilemma, ModernLoader, is developed to give attackers with distant command above the victim’s device, which permits the adversaries to deploy more malware, steal sensitive data, or even ensnare the pc in a botnet.
Cisco Talos attributed the bacterial infections to a beforehand undocumented but Russian-speaking risk actor, citing the use of off-the-shelf tools. Prospective targets integrated Eastern European users in Bulgaria, Poland, Hungary, and Russia.
An infection chains learned by the cybersecurity organization contain attempts to compromise vulnerable web purposes like WordPress and CPanel to distribute the malware by usually means of files that masquerade as bogus Amazon reward playing cards.
The very first stage payload is a HTML Application (HTA) file that runs a PowerShell script hosted on the command-and-manage (C2) server to initiate the deployment of intertim payloads that ultimately inject the malware using a system known as system hollowing.
Described as a uncomplicated .NET distant accessibility trojan, ModernLoader (aka Avatar bot) is geared up with characteristics to assemble system data, execute arbitrary instructions, or download and run a file from the C2 server, allowing the adversary to change the modules in genuine-time.

Cisco’s investigation also unearthed two previously campaigns in March 2022 with similar modus operandi that leverage ModerLoader as the main malware C2 communications and provide further malware, such as XMRig, RedLine Stealer, SystemBC, DCRat, and a Discord token stealer, among others.
“These campaigns portray an actor experimenting with diverse technology,” Svajcer stated. “The usage of all set-designed resources exhibits that the actor understands the TTPs required for a prosperous malware campaign but their specialized abilities are not developed plenty of to totally produce their possess resources.”
Found this posting attention-grabbing? Adhere to THN on Facebook, Twitter and LinkedIn to browse much more distinctive articles we publish.
Some areas of this post are sourced from:
thehackernews.com


 Hands-on Review: Stellar Cyber Security Operations Platform for MSSPs
Hands-on Review: Stellar Cyber Security Operations Platform for MSSPs