A novel technique adopted by attackers finds means to use Microsoft’s Background Clever Transfer Assistance (BITS) so as to deploy malicious payloads on Windows machines stealthily.
In 2020, hospitals, retirement communities, and health care facilities bore the brunt of an at any time-shifting phishing campaign that distributed customized backdoors this sort of as KEGTAP, which eventually paved the way for RYUK ransomware attacks.
But new investigate by FireEye’s Mandiant cyber forensics arm has now exposed a previously unidentified persistence mechanism that exhibits the adversaries made use of BITS to launch the backdoor.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Launched in Windows XP, BITS is a component of Microsoft Windows, which will make use of idle network bandwidth to facilitate the asynchronous transfer of data files concerning equipment. This is obtained by producing a job — a container that consists of the documents to download or upload.
BITS is generally employed to provide working procedure updates to purchasers as perfectly as by Windows Defender antivirus scanner to fetch malware signature updates. In addition to Microsoft’s very own solutions, the services is also place to use by other purposes such as Mozilla Firefox to allow downloads to keep on in the track record even when the browser is shut.
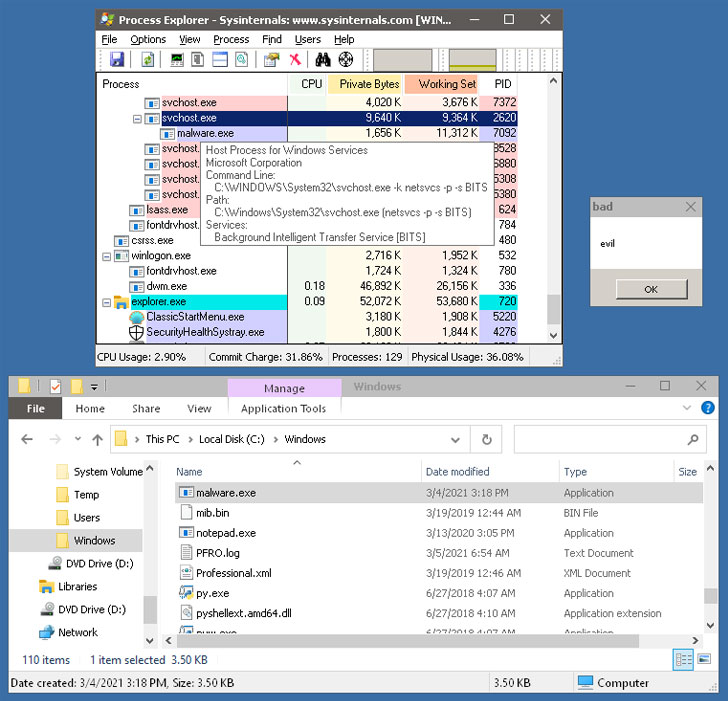
“When destructive programs make BITS jobs, files are downloaded or uploaded in the context of the support host approach,” FireEye scientists claimed. “This can be handy for evading firewalls that could block destructive or unidentified procedures, and it will help to obscure which application requested the transfer.”
Particularly, the article-compromise incidents involving Ryuk bacterial infections were observed to leverage the BITS service to generate a new occupation as a “Procedure update” that was configured to start an executable named “mail.exe,” which in convert triggered the KEGTAP backdoor, following making an attempt to down load an invalid URL.
“The destructive BITS position was set to attempt an HTTP transfer of a nonexistent file from the localhost, the researchers noted. “As this file would under no circumstances exist, BITS would cause the error point out and start the notify command, which in this circumstance was KEGTAP.”
The new system is yet one more reminder of how a practical device like BITS can be repurposed by attackers to their possess advantage. To help incident reaction and forensic investigations, the researchers have also produced obtainable a Python utility called BitsParser that aims to parse BITS database documents and extract occupation and file information and facts for further examination.
Located this article attention-grabbing? Stick to THN on Facebook, Twitter and LinkedIn to read through much more unique articles we put up.
Some elements of this posting are sourced from:
thehackernews.com

 Hackers Set Up a Fake Cybersecurity Firm to Target Security Experts
Hackers Set Up a Fake Cybersecurity Firm to Target Security Experts