Risk actors are capitalizing on a well-liked TikTok challenge to trick people into downloading information and facts-stealing malware, in accordance to new study from Checkmarx.
The trend, named Invisible Problem, entails applying a filter named Invisible System that just leaves driving a silhouette of the person’s system.
But the actuality that people filming this kind of videos could be undressed has led to a nefarious plan whereby the attackers article TikTok video clips with back links to rogue software program dubbed “unfilter” that purport to take away the applied filters.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“Guidance to get the ‘unfilter’ software package deploy WASP stealer malware hiding inside destructive Python packages,” Checkmarx researcher Guy Nachshon mentioned in a Monday assessment.
The WASP stealer (aka W4SP Stealer) is a malware that’s built to steal users’ passwords, Discord accounts, cryptocurrency wallets, and other delicate information.
The TikTok movies posted by the attackers, @learncyber and @kodibtc, on November 11, 2022, are approximated to have arrived at over a million views. The accounts have been suspended.
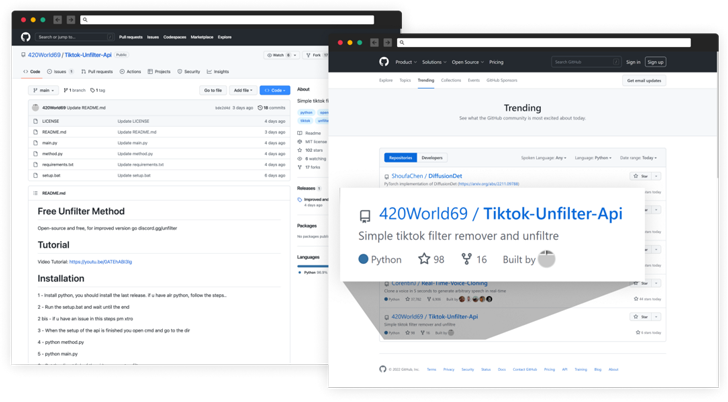
Also bundled in the video is an invite website link to a Discord server managed by the adversary, which had just about 32,000 associates just before it was noted and deleted. Victims becoming a member of the Discord server subsequently receive a url to a GitHub repository that hosts the malware.
The attacker has considering the fact that renamed the undertaking to “Nitro-generator” but not right before it landed on GitHub’s Trending repositories list for November 27, 2022, by urging the new customers on Discord to star the undertaking.
Apart from shifting the repository title, the threat actor deleted outdated information in the project and uploaded fresh kinds, one of which even describes the Python code as “Its (sic) open resource, its not a **VIRUS**.”
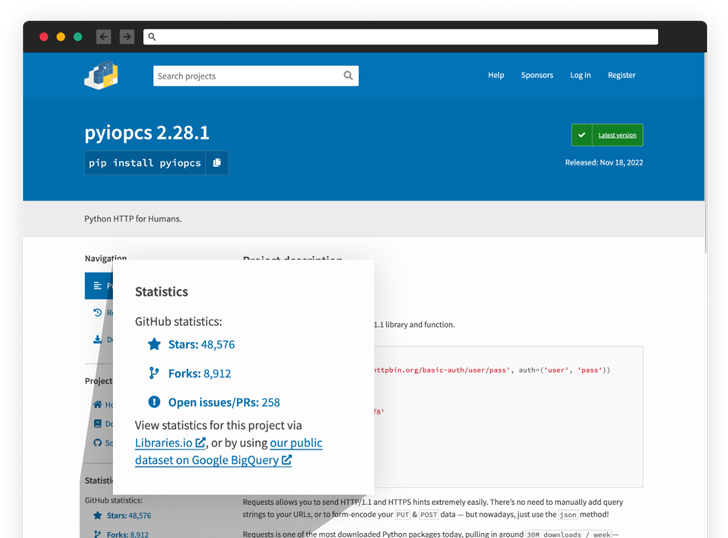
The stealer code is stated to have been embedded in numerous Python packages this kind of as “tiktok-filter-api,” “pyshftuler,” “pyiopcs,” and “pydesings,” with the operators swiftly publishing new replacements to the Python Package deal Index (PyPI) under diverse names upon having removed.
“The level of manipulation employed by software provide chain attackers is escalating as attackers become progressively clever,” Nachshon famous. “These attacks show all over again that cyber attackers have started to aim their interest on the open supply offer ecosystem.”
Identified this short article appealing? Adhere to THN on Fb, Twitter and LinkedIn to go through extra special articles we post.
Some parts of this article are sourced from:
thehackernews.com


 Getting board-level buy-in for security strategy
Getting board-level buy-in for security strategy