Microsoft has warned companies of a “special” attack marketing campaign that abuses speak to varieties printed on web sites to supply malicious backlinks to corporations via email messages made up of bogus legal threats, in what is nonetheless one more occasion of adversaries abusing reputable infrastructure to mount evasive campaigns that bypass security protections.
“The email messages instruct recipients to simply click a link to overview supposed evidence behind their allegations, but are in its place led to the obtain of IcedID, an info-thieving malware,” the firm’s danger intelligence team mentioned in a generate-up posted previous Friday.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
IceID is a Windows-primarily based banking trojan that’s employed for reconnaissance and exfiltration of banking credentials, together with features that let it to link to a remote command-and-manage (C2) server to deploy supplemental payloads such as ransomware and malware able of doing hands-on-keyboard attacks, stealing credentials, and moving laterally across afflicted networks.
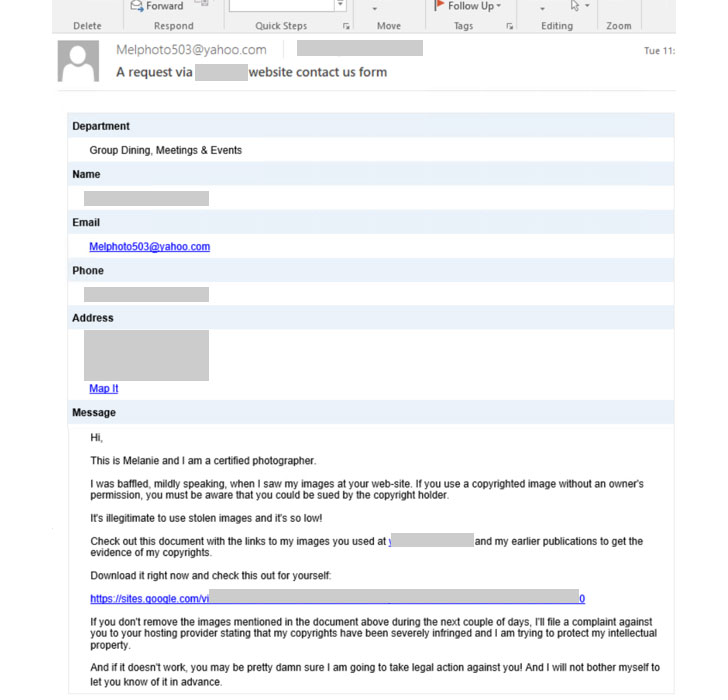
Microsoft scientists said the attackers could possibly have employed an automated tool to produce the email messages by abusing the enterprises’ contact sorts whilst circumventing CAPTCHA protections. The email messages themselves make use of authorized threats to intimidate victims, saying that the recipients “allegedly made use of their visuals or illustrations without the need of their consent, and that legal motion will be taken versus them.”
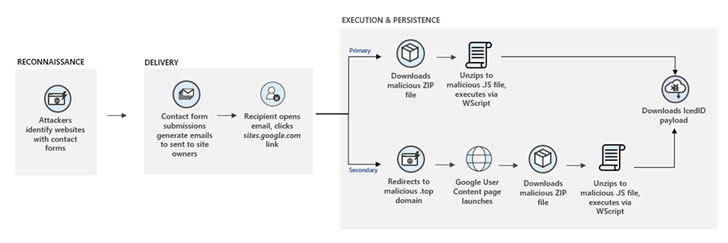
By invoking a perception of urgency, the concept is to guide the target into revealing delicate info, simply click a sketchy backlink, or open up a destructive file. In this infection chain, it is really a link to a web sites.google.com web site, which necessitates customers to indication in with their Google qualifications, pursuing which a ZIP archive file is quickly downloaded.
The ZIP file is made up of a closely obfuscated JavaScript file that downloads the IcedID malware. What’s much more, the destructive code has the potential to download secondary implants like Cobalt Strike, most likely placing impacted victims at further risk.
The novel intrusion route notwithstanding, the attacks are still another sign of how danger actors continuously tweak their social engineering ways to focus on providers with an intent to distribute malware while evading detection.
“The eventualities […] provide a serious glimpse into how refined attackers’ tactics have grown, though keeping the aim of offering harmful malware payloads these as IcedID,” the researchers stated. “Their use of submission sorts is notable simply because the e-mails never have the regular marks of malicious messages and are seemingly legitimate.”
Discovered this report interesting? Abide by THN on Facebook, Twitter and LinkedIn to browse a lot more unique articles we post.
Some components of this posting are sourced from:
thehackernews.com

 Detecting the “Next” SolarWinds-Style Cyber Attack
Detecting the “Next” SolarWinds-Style Cyber Attack