A danger actor with affiliations to the cyber warfare division of Hamas has been joined to an “elaborate marketing campaign” concentrating on significant-profile Israeli people used in delicate defense, legislation enforcement, and emergency products and services corporations.
“The marketing campaign operators use subtle social engineering strategies, finally aimed to deliver formerly undocumented backdoors for Windows and Android equipment,” cybersecurity company Cybereason explained in a Wednesday report.
“The intention at the rear of the attack was to extract delicate information from the victims’ products for espionage purposes.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The monthslong intrusions, codenamed “Procedure Bearded Barbie,” have been attributed to an Arabic-talking and politically-motivated group referred to as Arid Viper, which operates out of the Center East and is also acknowledged by the monikers APT-C-23 and Desert Falcon.
Most a short while ago, the threat actor was held responsible for attacks aimed at Palestinian activists and entities setting up around Oct 2021 applying politically-themed phishing email messages and decoy files.
The most up-to-date infiltrations are notable for their particular emphasis on plundering information and facts from desktops and mobile units belonging to Israeli people today by luring them into downloading trojanized messaging applications, granting the actors unfettered obtain.
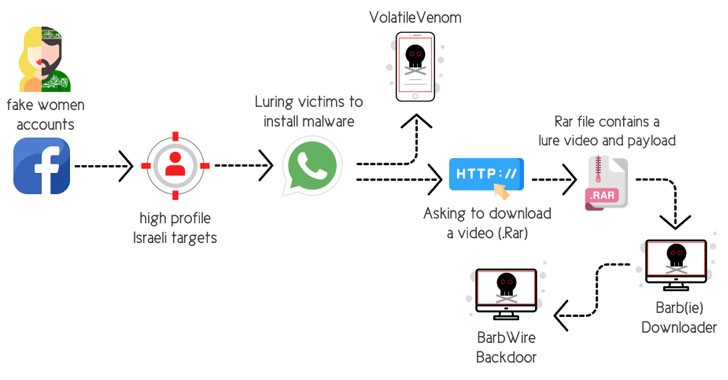
The social engineering attacks concerned the use of phony personas on Fb, relying on the tactic of catfishing to set up fictitious profiles of desirable younger girls to achieve the belief of the qualified persons and befriend them on the platform.
“Right after gaining the victim’s trust, the operator of the faux account implies migrating the dialogue from Facebook about to WhatsApp,” the scientists elaborated. “By doing so, the operator swiftly obtains the target’s cellular amount.”
The moment the chat shifts from Fb to WhatsApp, the attackers counsel the victims that they set up a protected messaging application for Android (dubbed “VolatileVenom”) as very well as open up a RAR archive file made up of explicit sexual content that sales opportunities to the deployment of a malware downloader named Barb(ie).
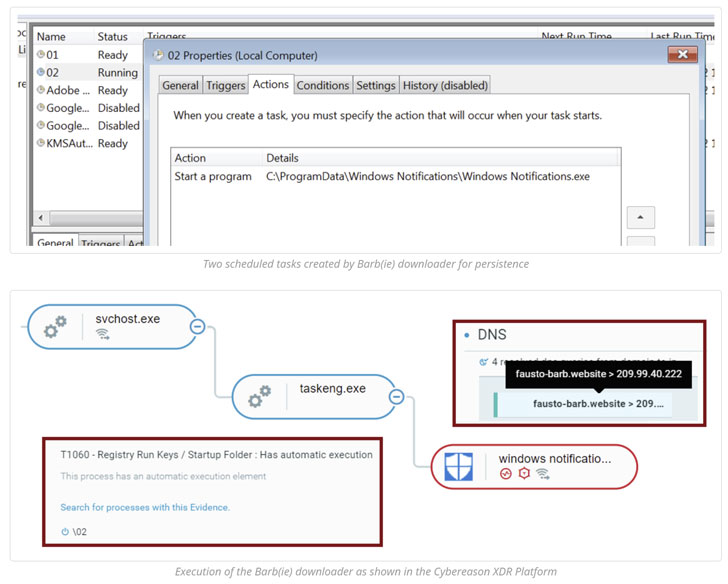
Other hallmarks of the marketing campaign have bundled the team leveraging an upgraded arsenal of malware applications, together with the BarbWire Backdoor, which is installed by the downloader module.
The malware serves as a device to entirely compromise the sufferer device, allowing it to establish persistence, harvest stored facts, document audio, capture screenshots, and download extra payloads, all of which is transmitted back to a remote server.
VolatileVenom, on the other hand, is Android adware that’s identified to spoof respectable messaging applications and masquerade as method updates and which has been put to use in various campaigns by Arid Viper considering that at the very least 2017.
A person this sort of illustration of a rogue Android app is termed “Wink Chat,” wherever victims trying to signal up to use the application are introduced an error concept that “it will be uninstalled,” only for it to stealthily run in the history and extract a vast wide variety of info from the cell gadgets.
“The attackers use a entirely new infrastructure that is unique from the known infrastructure utilized to concentrate on Palestinians and other Arabic-speakers,” the scientists mentioned.
“This marketing campaign demonstrates a appreciable phase-up in APT-C-23 capabilities, with upgraded stealth, more advanced malware, and perfection of their social engineering techniques which entail offensive HUMINT capabilities working with a pretty active and effectively-groomed network of bogus Facebook accounts that have been established really productive for the team.”
Observed this posting intriguing? Comply with THN on Facebook, Twitter and LinkedIn to study extra distinctive content material we publish.
Some components of this article are sourced from:
thehackernews.com



 SSRF Flaw in Fintech Platform Allowed for Compromise of Bank Accounts
SSRF Flaw in Fintech Platform Allowed for Compromise of Bank Accounts