The common charge of a info breach, in accordance to the most up-to-date analysis by IBM, now stands at USD 4.24 million, the highest reported. The primary bring about? Compromised credentials, generally induced by human error. While these conclusions proceed to clearly show an upward trend in the completely wrong course, the problem by itself is not new. What is new is the unparalleled and accelerated complexity of securing the workplace. CISOs/CIOs are working with legacy units, cloud hosting, on-prem, remote personnel, workplace primarily based, conventional software program, and SaaS.
How companies tailored was laudable, but now that personnel distribute throughout locations, offices and properties – with far more than half threatening not to return to places of work except hybrid performing is executed – the challenge morphs into securing a nonuniform perimeter.
We know passwords are not enough. Information-based mostly entry is normally fortified with other kinds of multi-factor authentication (MFA), these kinds of as auth apps or FIDO tokens, and in extremely delicate instances, biometrics.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Why powerful IAM is important for hybrid doing the job
The period of ‘BYOD’ (Provide Your Personal Unit) has evolved into what Gartner phone calls Provide-Your-Possess-Identification: staff members are accessing details from a selection of distant gadgets from a range of distinctive places.
Cybercriminals can intercept details in a variety of strategies, from compromised credentials to phishing scams to gentleman-in-the-center attacks, which are made less difficult on community networks with no security controls, these types of as Wi-Fi hotspots at espresso shops or airports. If your staff access is only primarily based on expertise variables such as usernames and passwords, attackers could quickly achieve complete accessibility to delicate info.
Hardware-based security tokens or dongles have gained reputation, particularly at the organization degree. They generate a code for the person to enter when prompted, so that only the consumer possessing the token can attain entry. But these individual, tiny components gadgets are not with no their problems.
Challenges with hardware authentication
Price tag — Security tokens cost involving $50-$100 on typical for a solitary unit. As a result, these devices are likely to be reserved only for a number of superior-risk men and women – although lessen-profile staff members are left vulnerable.
Lost products — Hardware tokens can be shed, stolen, or neglected, and workforce generally only see correct when they want access. Buying new tokens is inconvenient and high priced.
UX — Finding the product and moving into the code usually takes user hard work, and are not able to be effortlessly used for immediate provisioning, staff transform, or do the job with outside contractors.
Attack risk — Hardware tokens are also not absolutely efficient towards MITM attacks – though they can not be straight remotely accessed, a bad actor can trick the consumer into getting into the code on a fraudulent edition of the web-site/login page.
There is an revolutionary, new technology that presents a powerful possession factor for IAM devoid of further hardware units – and it really is in everyone’s palms by now.
Cellular phone possession as an alternate to hardware tokens
The more simple, a lot easier choice to getting high-priced tokens is to make use of some thing your workforce by now have: their cellular phone.
Using the innovative cryptographic security of the SIM card, mobile networks presently authenticate shoppers securely and invisibly to allow for calls and information. SIM-centered authentication is tamper-resistant, real-time verification that operates the exact same as chips in financial institution cards.
With no user motion or codes to type, SIM-centered authentication will make login basic for your personnel, but retains malicious actors out. By authenticating with the SIM card itself, alternatively than just the mobile quantity, it truly is also doable to test for latest SIM swap action, stopping account takeover attacks.
It really is considerably extra cost-efficient, deployable at scale, and common, meaning every single employee, not just a few, has the best amount of security. And in contrast to very small and very easily-dropped components dongles, the mobile phone is an critical unit that staff will previously get with them almost everywhere.
Now, APIs by tru.ID open up SIM-based mostly network authentication for enterprises and enterprises to carry out frictionless, safe verification.
Any further considerations more than person privacy are alleviated by the fact that tru.ID does not method individually identifiable data between the cell network and its APIs. It really is purely a URL-dependent lookup.
See tru.ID SIM security solution in motion
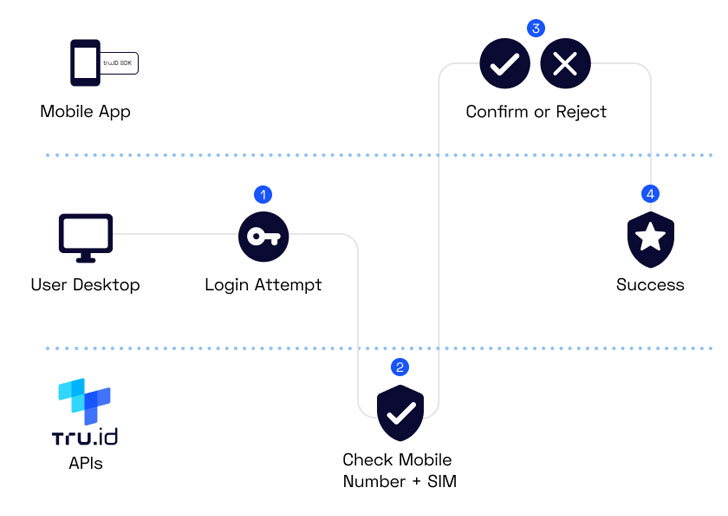
A single of the approaches to use tru.ID APIs is to employ a passwordless one-faucet registration and login alternative to obtain an organization system applying a companion app. Here is an case in point workflow:
tru.ID addresses around 2 billion cell phones in 20 marketplaces and can be deployed in two strategies. It can either be built-in immediately into a organization application (if current) with basic Relaxation APIs and SDKs, or it can be rolled out with a tru.ID companion app that verifies worker entry employing their cellular credentials. tru.ID is keen to listen to from the neighborhood to explore scenario experiments – just go to the web-site to see it in action in a demo or get started coding.
Located this short article attention-grabbing? Stick to THN on Facebook, Twitter and LinkedIn to study far more special information we article.
Some areas of this report are sourced from:
thehackernews.com


 Australian Federal Police plots “aggressive” cyber division following law change
Australian Federal Police plots “aggressive” cyber division following law change