Graphic of the Washington, D.C. business office of law firm BakerHostetler.
In a discipline exactly where each and every contractor releases an yearly infosec report, BakerHostetler’s is one of a kind. BakerHostetler, a regulation firm with a large facts and privacy presence, compiles facts from their client’s experiences to supply a rare lawyer’s perspective on cyber data. No amount of seller telemetry can supply some of the info they have, together with consequence stats from ransomware negotiations or the frequency of litigation.
Even though the firm’s stats are relatively self-picking — they refer to results for providers savvy sufficient to go after suitable lawful assistance — they are the closest search we have to outcomes ordinarily hidden at the rear of boardroom doors.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
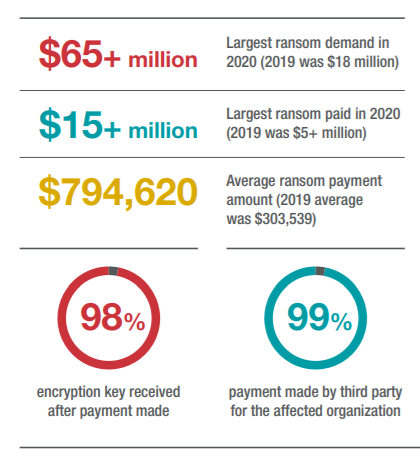
For instance, contrary to popular rhetoric, which frequently portrays spending ransom as a dangerous proposition inviting criminals to choose the revenue and operate, business clients who paid ransoms acquired an encryption important 98 per cent of the time.
SC spoke to Craig Hoffman, companion at BakerHostetler and the main editor of the report, about the genuine outcomes from breaches.
A great place to start would be why a legislation company would launch cybersecurity stats. What do people get listed here that they simply cannot get from security sellers?
Hoffman: If you seem at forensic firms, they have great once-a-year stories. The Mandiant M-Traits report is 1 I have followed for a extended time. It has fantastic details, this sort of as Mitre attack chains and dwell time until eventually investigation. But it won’t have the other elements of a breach: How very long did it acquire the company they investigated to ship a see to people today? Or, did they get sued right after they provided that detect? Given that we are advising a corporation and bringing in distinctive types of gurus to help us give information, we see information from the whole picture and check out to use that listed here.
Mandiant has documented on the forensics, CoveWare has excellent facts releases quarterly on ransom payments. People are primarily based on a solitary resource. Ours is dependent on viewing incidents across numerous forensic corporations, a number of payment facilitation, and negotiators. If you appear at the breakdown of providers, it’s throughout all industries and earnings dimensions.
How diverse is the knowledge, which you have a window on, than other scientists get to see?
One of the most significant disparities lies in the total impression. If you glance at many others who find a statistic for the average price tag of a data breach per report, that quantity, no matter if it is $200 or $300 for each file, has no good, useful use. You would say, “Okay, we have a databases of 100,000 clients. So that suggests if we have an incident we’re going to have billions of bucks in legal responsibility.” Which is just not what really happens.
If you consider the components of our report, you get a far more reasonable projection of what your to start with-party and 3rd-party expenses and liabilities are. You can say, “Alright, I have an incident. What is the likelihood that I essentially get sued? Should really I factor in litigation expenses into my expectation of what my probably fees are?” Previous 12 months, our purchasers provided notice 543 periods. Out of those people, our customers were only sued 20 periods. So if you are stating, I need to have to figure out how a great deal and how probable it is I will have litigation, unless of course it is a situation that fulfills a pair of criteria, it’s not likely you will be sued. You don’t want to factor the exact liabilities into your cost.
Just one of the data that jumps out suitable absent is that nearly all of your consumers — 98 % — who compensated a ransom received their info again. That goes towards a common narrative in the market and the authorities that men and women who shell out ransom operate a sizeable risk of being cheated by a legal.
 Courtesy BakerHostetler
Courtesy BakerHostetler
I noticed the current activity pressure and their extensive listing of tips. All of that is excellent. I hope they are enormously profitable in shutting down these ransomware menace teams. Right up until that comes about, we however have companies who are affected by this and need to have enable.
With the Treasury alert that arrived out in Oct of 2020, I suspect the authorities would want that businesses not spend the ransom. But you just really don’t have a ton of applications to make that occur when corporations are in a posture of both incurring a large amount of lost earnings and impacting their interactions with clients and stakeholders or building a payment to enormously lessen that effect.
And it’s not unlawful to make that payment. They make a enterprise conclusion. There are only a several teams on [the sanctioned list], or affiliated with corporations that are on there, or work out of international locations on the sanctions list. For most of the ransomware actors that are lively suitable now, there is no indicator that they are in a country or affiliated with a group that are. There ought to be an means to have self confidence that you can make a payment with no violating legal guidelines.
As you take note in your figures, virtually all of your consumers use a third-party negotiator in payments. Does that have an affect on the achievement level?
They go hand-in-hand. Yes, you are working with a criminal. If you really don’t know who they are, how can you have any self-assurance that if you deliver cash to them they will stay up to their conclude of the deal? In reality, for the reason that you are pretty much always making use of a third party to do the negotiations, they can recognize who that team is and detect their observe report.
You can see how several situations they’ve negotiated with the group in advance of, and what their track history is. When you achieved an arrangement to fork out, did they give you an encryption tool or try to re-extort you? For groups that do re-extortion, or who never deliver an encryption instrument that works, ransomware only functions a handful of occasions for them. It gets recognized who they are, and persons don’t negotiate with them.
 Courtesy BakerHostetler
Courtesy BakerHostetler
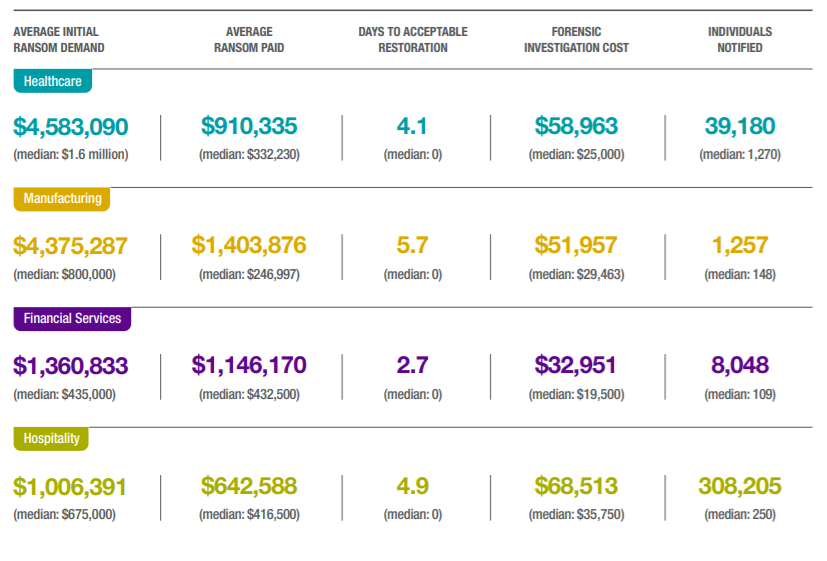
When customers come to you, do they presently have a sense of the position negotiation plays? Your stats on negotiated ransoms are substantially lower than the requires. In healthcare, the median remaining price tag was around 20% of the asking value. How are individuals prepared and how should really they be ready?
Persons have a great deal of questions at the outset. What does this signify we’re dealing with a prison? You necessarily mean, we can really negotiate with them? What are the tactics for negotiating with them? The greatest factor in having a reduction from the first demand is time. How speedy do you need to obtain the decryption instrument to restore functions? The extended you can maintain out, the additional you can drive down the price.
You pointed out that only a tiny number of corporations that fulfill specified conditions are inclined to get sued after a breach. What are people standards?
If you’re an corporation preparing to do observe, you want to know if it is likely that you’re going to be sued. Are you carrying out detect to 10,000 or extra people today, and does it contain their social security range? If it does, there’s a first rate probability, primarily with much larger corporations. If it is an incident that comes pretty noted on, there is a really great prospect to get sued. If the incident was a breach of an employee’s email account where an individual could see info, and you are likely to notify 1000 men and women, soon after the recognize is despatched, there is a really great likelihood of not currently being sued.
Eventually, the report specials with a wide array of organizations that are possibly large or well prepared adequate to appear question for assist. How will issues be diverse for smaller sized corporations or types that are fewer well prepared?
At providers that are smaller and up to medium, and even at types who are massive, there is often no specified man or woman whose job it is to handle the over-all impression of a security incident. Usually, it is not someone’s career to go uncover names and addresses to build a notification. When corporations are already lean, it is difficult to have an employee detect and examine, identify detect obligations, and send them out.
Businesses have to pull jointly and it’s definitely taxing. It can take a major toll on the main men and women who pull jointly to do it.
Some parts of this short article are sourced from:
www.scmagazine.com


 The business of cyber: How security defines (or derails) success
The business of cyber: How security defines (or derails) success