Researchers have disclosed a security shortcoming impacting three various WordPress plugins that effect in excess of 84,000 sites and could be abused by a destructive actor to get above vulnerable websites.
“This flaw made it attainable for an attacker to update arbitrary site alternatives on a vulnerable internet site, provided they could trick a site’s administrator into undertaking an motion, these kinds of as clicking on a link,” WordPress security company Wordfence mentioned in a report revealed final week.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Tracked as CVE-2022-0215, the cross-web site ask for forgery (CSRF) flaw is rated 8.8 on the CVSS scale and impacts 3 plugins managed by Xootix —
- Login/Signup Popup (Inline Variety + Woocommerce),
- Facet Cart Woocommerce (Ajax), and
- Waitlist Woocommerce (Back again in inventory notifier)
Cross-site request forgery, also regarded as a single-click attack or session using, happens when an authenticated conclude-user is tricked by an attacker into submitting a specially crafted web ask for. “If the target is an administrative account, CSRF can compromise the whole web application,” OWASP notes in its documentation.
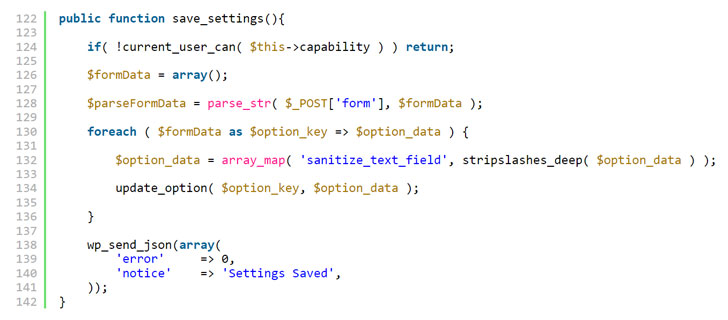
Specially, the vulnerability has its origin in a absence of validation when processing AJAX requests, efficiently enabling an attacker to update the “consumers_can_sign up” (i.e., anyone can sign up) option on a site to real and set the “default_position” setting (i.e., the default function of users who register at the blog site) to administrator, granting entire management.
Login/Signup Popup is mounted on around 20,000 sites, whilst Facet Cart Woocommerce and Waitlist Woocommerce have been put in on more than 4,000 and 60,000 websites, respectively.
Subsequent dependable disclosure by Wordfence researchers in November 2021, the issue has been tackled in Login/Signup Popup variation 2.3, Side Cart Woocommerce variation 2.1, and Waitlist Woocommerce 2.5.2.
The conclusions arrive a little above a thirty day period just after attackers exploited weaknesses in 4 plugins and 15 Epsilon Framework themes to concentrate on 1.6 million WordPress internet sites as part of a substantial-scale attack marketing campaign originating from 16,000 IP addresses.
“However this Cross-Web page Request Forgery (CSRF) vulnerability is fewer possible to be exploited because of to the point that it calls for administrator conversation, it can have a sizeable effects to a efficiently exploited website and, as these, it serves as an unbelievably critical reminder to stay mindful when clicking on inbound links or attachments and to make sure that you are consistently preserving your plugins and themes up to date,” Wordfence’s Chloe Chamberland claimed.
Identified this short article intriguing? Stick to THN on Facebook, Twitter and LinkedIn to go through much more distinctive content we post.
Some sections of this report are sourced from:
thehackernews.com



 Ukrainian Government Officially Accuses Russia of Recent Cyberattacks
Ukrainian Government Officially Accuses Russia of Recent Cyberattacks