A single of the determining aspects of how much damage a cyber-attack bring about is how speedy corporations can reply to it. Time to reaction is critical for security teams, and it is a big hurdle for leaner groups.
To help improve this metric and greatly enhance organizations’ skill to respond to attacks quickly, lots of endpoint detection and reaction (EDR) and extended detection and response (XDR) suppliers have commenced which includes some kind of automation in their platforms to reduce the have to have for manual intervention.
XDR supplier Cynet promises that they go beyond existing solutions when it will come to security automation. Much more than automating personal components, the Cynet 360 platform (see a stay demo right here) provides automation across every single section of incident response – from detection as a result of remediation. The company works by using a range of resources and procedures to preserve corporations risk-free and swiftly react to any emerging threat.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
How Cynet eliminates the guesswork from Incident Reaction
Cynet fully automates the response workflow from get started to complete. It also removes or enormously minimizes the need to have for handbook attempts and guarantees key reaction details and tasks are done swiftly and correctly.
The system commences by grouping alerts logically into incidents that generate a far better image of a potential attack. This assists reduce notify exhaustion and presents bigger risk context.
The system also supplies an Incident Motor that automates:
- Investigation – automated root result in and impression assessment
- Findings – actionable conclusions on attack components and their impacted entities
- Remediation – removing any destructive existence and action throughout end users, networks, endpoints, and infrastructure.
Deploying preset remediation steps
A single way Cynet can help organizations velocity their time to response is by deploying a huge assortment of remediation applications for contaminated hosts, compromised user accounts, and attacker-managed network visitors. The business provides a broad set of remediation actions immediately out of the box. As a end result, it drastically raises the range of attacks the procedure can react to mechanically.
Employing and making playbooks
Another automation-centered element made available by Cynet is its capability to use both equally pre-developed and personalized playbooks. These are chains of remediation actions that can be quickly executed upon detection of unique threats and attacks. Cynet will come pre-packaged with many all set-created playbooks, but people can swiftly establish their have chains dependent on organizational desires, distinct threats, and protocols.
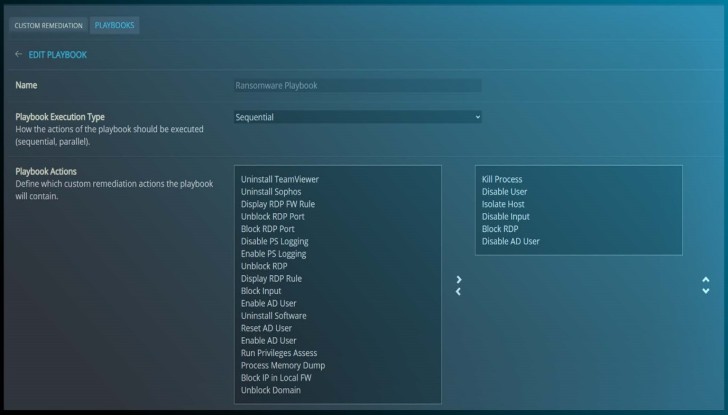 Customized Remediations
Customized Remediations
Teams can generate playbooks that bring about on certain alerts, or suspicious actions. Playbooks are bult applying drag-and-fall, allowing groups swiftly establish the ideal flows of response actions to make sure a quickly and comprehensive resolution.
The Incident Motor
Cynet’s Incident Engine is an additional one of a kind tool the firm gives to give groups considerably better visibility into attacks and their will cause. The motor lays out the incident in a visual timeline to support teams greater ascertain the attack’s root bring about and scope, to its eventual resolution.
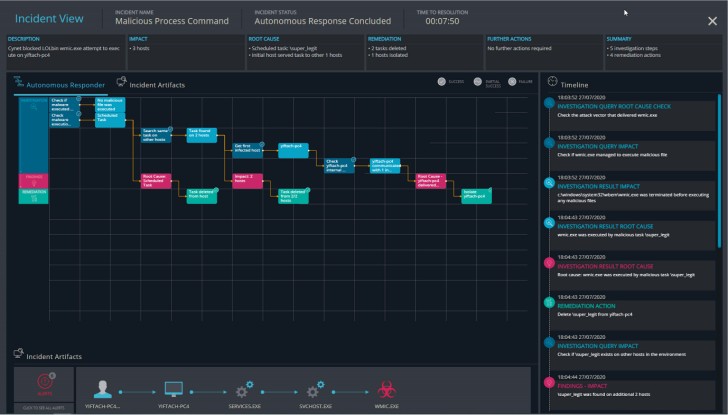 The Incident Engine
The Incident Engine
The Incident Engine commences by asking a sequence of inquiries to establish the lead to and scale of the attack. As soon as it has findings, it can take the automatic actions vital to remediate a threat. On the timeline, consumers can watch each and every distinct remediation and the party or inform that triggered it.
Primarily for lean security groups that will not often have the means or bandwidth readily available to examine an attack just after the point, the Incident Motor presents an exceptional way to fully grasp threats and assure hazardous attack elements are not ignored.
The motor will also search the full surroundings to check for related threat elements. If found, the Incident Motor can act immediately to remove any remaining threats.
You can study much more about Cynet’s automated reaction abilities by requesting a dwell demo here.
Discovered this report appealing? Observe THN on Facebook, Twitter and LinkedIn to study a lot more distinctive information we post.
Some elements of this short article are sourced from:
thehackernews.com

 Enterprises Need 27 New IT Hires to Manage Security Debt
Enterprises Need 27 New IT Hires to Manage Security Debt