Lots of enterprises count on additional than a single security device to protect their technology belongings, gadgets, and networks. This is particularly genuine for companies that use hybrid programs or a mixture of cloud and nearby purposes. Likewise, businesses whose networks include a multitude of smartphones and IoT units are likely to deploy multiple security options ideal for various situations.
Utilizing many security options tends to be unavoidable for a lot of, primarily people that have outgrown their preceding network setups. Providers that grow to new branches and even abroad operations have to make use of extra security steps and applications. This use of many tools or software frequently prospects to critical issues, though.
The management of the many cybersecurity methods can turn into much too difficult and difficult to tackle, specifically for companies with minimal working experience in addressing cyber threats, let alone actual attacks. This can consequence in confusion and the incapability to detect vulnerabilities and reply to rising troubles properly.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The alternatives
Just one alternative to the predicament of making use of various security defenses is to glimpse for a single business that gives anything to switch existing security defenses. There are security suppliers that provide a thorough array of protection, from client-based mostly malware detection and avoidance resources to SaaS security.
Having said that, this is unlikely to be a effortless preference for most businesses. Switching to a new cybersecurity solution provider involves a important modify and is maybe likely to be much more high-priced with every thing taken into account. It also does not generally promise much better security.
The next option does not have to have a swap to a distinctive platform or security service provider. It is all about centralizing and unifying even fragmented sets of security alternatives. Corporations can use a solution that serves as a cybersecurity central command platform to keep an eye on and deal with all security instruments by a unified dashboard.
Centralized cybersecurity
To exemplify the concept of centralized cybersecurity Cyrebro has developed a security solution that unifies all of the security instruments of an corporation to make it a lot easier to observe security events, proactively offer with cyber menace intelligence, and make sure a immediate incident reaction.
Cyrebro touts 3 highlight characteristics: centralized eyesight, a single cyber mind, and clear accountability.
Centralized eyesight refers to Cyrebro’s capability to get information on all security activities and have a apparent sense of what they necessarily mean to the group. It is not only about accumulating specifics from numerous resources. It is also about producing feeling out of all the knowledge by way of correlation and other ways that just take gain of having unified accessibility to information from many sources. It also allows sensible prioritization when it comes to addressing threats.
Meanwhile, Cyrebro’s “one cyber brain” utilizes proprietary detection algorithms to monitor, review, and interpret the attainable results of security events as detected by the distinct security solutions employed by an group. It works on the idea of turning chaos into clarity manufactured feasible by way of automatic integration, fast contextual evaluation, and simple-to-comprehend real-time tips.
Moreover, Cyrebro will help ensure clear accountability, which means that the centralization does not only result in the streamlining of security controls. Yet another crucial purpose of Cyrebro is to notify corporations which alternatives do the job and which demand tweaking, reconfiguration, or in some situations, finish substitution. It offers a clearer perspective of how protected or not an business is with its present set of measures.
A single essential characteristic worth mentioning about Cyrebro is that it is technology-agnostic. It does not matter what variety of security methods are applied in an group or which certain platforms or operating techniques they are constructed to function with. To make certain helpful cybersecurity unification and centralization, Cyrebro can’t discriminate which antivirus, firewall, or other security program software it can get the job done with. It has to be appropriate with pretty much all answers to accomplish detailed visibility and productive security administration.
Simplified method
So how accurately does cybersecurity unification and centralization perform? It really is less difficult than what lots of would possibly be expecting. Heading again to Cyrebro as the instance, the procedure normally takes only a number of actions.
Cyrebro is a SaaS alternative, so it does not involve any program set up or servicing. The to start with move is merely to acquire a username and password to be in a position to log in to the method and access its means.
Right after logging in, the integration of security methods follows. Mainly, this usually means connecting all of an organization’s security tools to Cyrebro, so they can be monitored and managed. Cyrebro works with numerous antiviruses, endpoint detection and response software program, security info and celebration management applications, network firewalls, web application firewalls, safe web gateways, VPNs, email security resources, cloud entry security brokers (CASB), IDS/IPS security tools, cloud platforms, data loss prevention units (DLS), network obtain controls (NACs), privileged entry management (PAMs), and user and entity habits analytics (UEBA) options.
 Screenshot of the Cyrebro dashboard
Screenshot of the Cyrebro dashboard
Right after integration is completed, companies can start off checking all security actions as details from different details converge in a single Cyrebro dashboard. Every little thing the security officers need to have to know is shown in a unified and centralized interface with contextual facts to facilitate a far better knowledge of the security occasions detected.
Gains of centralization
By acquiring in depth visibility of the complete company cybersecurity technique, CTOs, CISOs, as very well as CIOs have a superior comprehending of their security stance. They are not still left in the dark for the reason that of needless red tape or the incompetence of those people tasked to deal with precise security solutions in distinct branches or places of work.
This infers proactive security protection whereby businesses know what matters for their network defense and what to do when they come upon threats and attacks. Centralization permits strategic checking as a unified cybersecurity system like Cyrebro is made to present contextual visibility across techniques, making it faster and less difficult to detect the early indications of suspicious network action.
Strategic checking, in flip, final results in increased risk intelligence and snappier incident reaction. Cyrebro has a steady Indication of Compromise (IOC) feature dependent on granular contextual facts and equipment understanding to make sure that all the appropriate alerts are raised in a timely way. It is straightforward to make security alerts, but also many of them can stifle reaction as it would be challenging to go through hundreds of security incidents. Proper risk intelligence requires performance, which signifies the have to have to limit fake positives devoid of lessening the thoroughness of risk detection and contextual analysis.
In accordance to a CNBC report, 93 per cent of attacks deal with to compromise property inside of a few minutes. Likewise alarming, the world-wide ordinary for cyber attack dwell time is 146 days in accordance to a report cited by Infocyte. This indicates that it usually takes corporations approximately five months to detect attacks from the time the compromise occurred.
Corporations need to have to be brief in responding to attacks, some thing that can only be finished by promptly realizing all of the vital security incident aspects. Rapid reaction and mitigation lessen the impression of security incidents on enterprise continuity. Cyrebro improves this rapid reaction benefit more by like serious-time security analyst help to assist businesses with small cybersecurity ordeals evaluate their facts better.
On top of that, cybersecurity centralization permits process optimization centered on all the risk intelligence and updates accumulated. It also encourages proactive threat hunting, to make certain that very little penetrates the security defenses and sleeper attacks are detected ahead of they get activated.
 Screenshot of the Cyrebro menace data research interface
Screenshot of the Cyrebro menace data research interface
Moreover, the unification of organization security remedies presents a sizeable improve to forensic investigations. With all security info compiled in 1 spot for uncomplicated access, businesses can accelerate ongoing investigations in excess of suspected incursions. Also, in situations when remarkably advanced attacks deal with to penetrate, specifically insider-pushed kinds, centralization would make it straightforward to scrutinize every thing to decide what went incorrect and plug the vulnerabilities or transform ineffective measures.
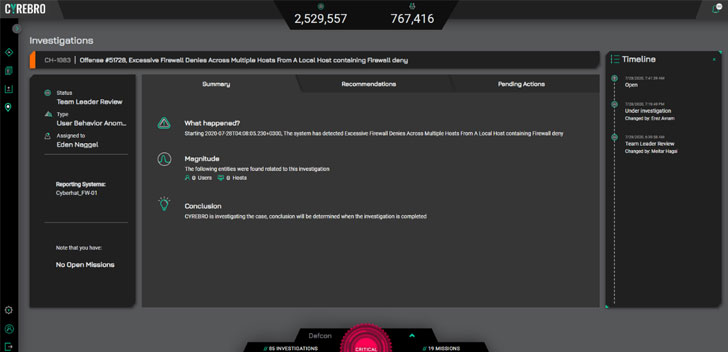 Screenshot of the Cyrebro Investigations interface
Screenshot of the Cyrebro Investigations interface
Who wants cybersecurity centralization?
Cyrebro is created for a wide assortment of users, from micro and SMBs to enterprises and managed security provider suppliers. Logically, if an group takes advantage of several security solutions, it would be better to unify them for a lot easier monitoring and response. Regardless of the dimension, a enterprise can be inclined to repeated attacks and vulnerabilities for the reason that of the use of many units and numerous networks and web expert services.
Cyrebro recently acquired a report from a consumer about a phishing plan. The internet site of a humanitarian assist agency was used by a destructive actor who sent e-mail that resembled a reputable support notification from Microsoft.
The phishing URL reportedly redirects various situations, in the end landing on a simulated Microsoft login page. Clueless victims who enter their login details conclude up submitting their credentials by way of Write-up to the exact same phishing domain. The humanitarian support company evidently suffers from a mirrored XSS or cross-web-site scripting vulnerability, and they had no prior know-how of this until eventually Cyrebro informed them.
This situation is a demonstration of how everybody requires to fork out added focus to their security posture. Small corporations or large enterprises will need to have a proactive and high-visibility cybersecurity coverage to make guaranteed that all hints of a doable social engineering plan are detected and resolved immediately. At the identical time, much larger corporations or establishments ought to also assure extensive security visibility not only to discourage attacks versus them but also to steer clear of becoming an unwitting accomplice in phishing or other subtle cyber attacks.
Without cybersecurity centralization, Cyrebro’s consumer would not have instantly detected the phishing attack. In the meantime, if the humanitarian assist agency had a centralized cybersecurity posture, they would have detected the vulnerability in their internet site and carried out the important therapies.
The takeaway
Centralization may perhaps be frowned upon in the capitalist world, but it tends to be the much more preferable approach when it arrives to security. You will find a purpose why in decentralized federal sorts of federal government, the defense job is assigned to the federal government, and states are not still left to handle defense and security problems individually.
At the top of the hacktivism attacks versus the United States government, a Boston University paper referred to as for cybersecurity centralization to increase response to the ongoing threats. Centralization allows security gurus to coordinate much better and assess vulnerabilities, threats, and true attacks with higher accuracy and performance.
Productive defense posture necessitates coordination, collaboration, and in depth visibility. Competitors amongst departments, branches, or units hardly ever final results in anything at all productive. It only makes siloing, which prevents the sharing of beneficial details and technologies that could bolster defenses and help prompt response to threats and attacks.
Observed this article appealing? Comply with THN on Facebook, Twitter and LinkedIn to study additional unique articles we write-up.
Some parts of this write-up are sourced from:
thehackernews.com


 Google limits which apps can access the list of installed apps on your device
Google limits which apps can access the list of installed apps on your device