If you happen to be at all acquainted with web development, you have in all probability listened to of SQL injection attacks. An SQL injection is quantity just one on the OWASP Major 10, a checklist of the most critical web application security hazards, and can have a devastating impact.
They are simple to discover and execute, and so they’re one of the most generally utilized types of cyber attack. They’re also relatively simple to protect versus, yet they’re a commonplace attack strategy on social media sites, online merchants, universities, and SMBs who really don’t have the know-how or assets to reduce these attacks.
The explanation SQL injection attacks can verify so fearsome is that a big proportion of the web is built on SQL databases, which include the types supplied by the likes of Microsoft, Oracle and SAP. This will make SQL injection just one of the most versatile attack procedures in a hacker’s arsenal, and it really is ordinarily between the 1st applications utilised as aspect of a breach try.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
What is SQL injection?
To analyse how SQL injection works we very first have to set up what SQL is. In brief, SQL (or structured question language) is a programming language built to handle huge databases, such as the type utilised by web programs. SQL is made use of to modify, retrieve and reorganise the information in a database with textual content-primarily based instructions.
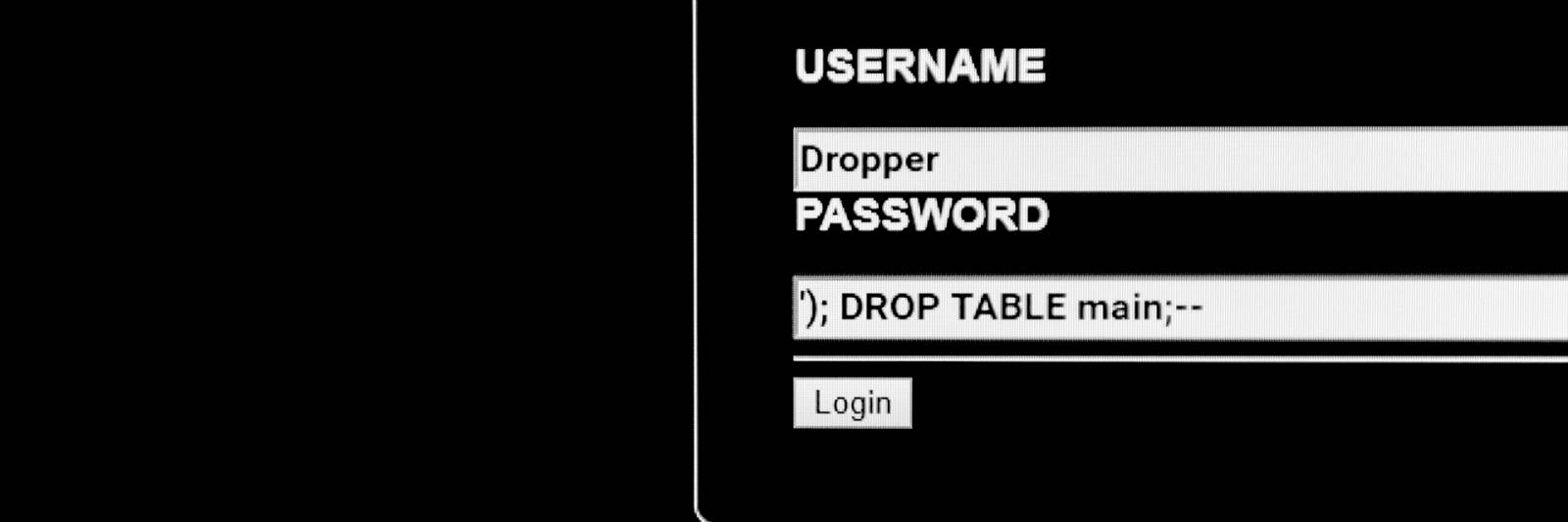
A SQL injection attack is when a third party is able to use SQL instructions to interfere with back-end databases in means that they shouldn’t be permitted to. This is usually the final result of websites straight incorporating user-inputted textual content into a SQL query and then running that question against a database. How this operates in a non-destructive context is that the person-inputted textual content is utilized to look for the database – for instance, logging in to a unique account by matching it primarily based on the username and password entered by the consumer.
In a SQL injection, even so, this system is hijacked to complete unauthorised functions. To use a simple case in point, the attacker could make use of the question process outlined higher than by working with a further SQL command to override the query’s logic. The common SQL query is created to log into an account once it finds a single in the database that matches a particular established of inputs consequently, if the attacker is able to amend the query so that it adds the ailment ‘OR 1=1’, it usually means that each and every entry in the desk will return a beneficial outcome. Below people ailments, the question will log into the to start with account it finds, which in most databases is a user with admin privileges.
This capabilities in a incredibly very similar way to cross-web-site scripting, a further design of injection attack that requires hackers inputting malicious scripts into web forms to target user browsers.
1 of the most common results of a SQL injection attack is the theft of consumer details. Login credentials, email addresses or own info can all be marketed on the black market place or exploited for further cyber attacks. The attack can also be utilised to knock apps offline by deleting tables from the database, or to add new facts to the database.
How to defend against SQL injection
Like all programming languages, SQL is created around the use of sure people and formatting structures to designate functions. SQL injection exploits this by making use of text enter fields to introduce these elements into normally-benign queries, but it can be counteracted by ‘sanitising’ the consumer enter sections in the course of a site or software.
Adding a layer of abstraction enables you to strip out figures which are employed in SQL queries but not whichever the enter field concerns. The semicolon, for instance, is applied in SQL queries, but does not characteristic in names and is not permitted in email addresses, so anyone entering it into a textual content area built to acquire names or email addresses is pretty much undoubtedly making an attempt a SQL injection attack.
A significantly far more efficient way, however, is to use parameterised queries. Somewhat than instantly jogging a query based on consumer inputs, this approach of databases construction requires specifying the framework of the query beforehand and plugging the person input into predefined slots. This ensures that, even if the person does enter malicious SQL code into the textual content field, it will be properly wrapped in just a more substantial question that will not recognise it as these kinds of.
It is also ideal observe to make certain that these safeguards are applied to all textual content input types, relatively than just all those that join to sensitive databases, as lateral motion and privilege escalation are widespread hallmarks of SQL injection attacks. You need to also make confident that databases mistake messages are not displayed on general public-experiencing internet websites, as these can give attackers additional data about the composition of your databases to advise even further attempts.
How have SQL injections been employed and what effect do they have?
SQL injections have been made use of in several cyber attacks above the previous 20 years, often as an original probe in advance of other, much more advanced tools and procedures are deployed.
They are practically nothing to scoff at, although.
SQL injection can consequence in a stolen, deleted, or altered sensitive information. Attackers can build bogus identities, adjust transactions, make by themselves database administrators, or even go so considerably to entirely just take about the web server.
SQL injection attacks have been employed in the 2020 Freepick information breach to accessibility 8.3 million users’ documents, and in 2015’s mammoth TalkTalk breach, resulting in the theft of more than 150,000 customers’ personal info and a £400,000 pound fine. Back again in 2012, a team also applied SQL injection attacks to steal 450,000 Yahoo users’ login information, in a single of a variety of breaches that would hit the embattled web enterprise in the adhering to several years.
In accordance to a report from web security business Akamai, SQL injection attacks have accounted for much more than 65% of web-centered attacks amongst November 2017 and March 2019, with the US and the UK topping the charts as the most often-qualified international locations.
Some elements of this post are sourced from:
www.itpro.co.uk

 HackBoss malware is using Telegram to steal cryptocurrency from other hackers
HackBoss malware is using Telegram to steal cryptocurrency from other hackers