As a CISO, one of the most challenging issues to answer is “How effectively are we secured ideal now?” Between the acceleration of hackers’ offensive abilities and the dynamic nature of facts networks, a drift in the security posture is unavoidable and requires to be continually compensated. For that reason, answering that question implies continually validating the security posture and being in a position to verify it such as, towards the most current emerging threats.
Yet, the bulk of cybersecurity is concentrated on defensive tools. The mix of the quick evolution of technology and the multiplication of technology layers, combined with the professionalization of the menace landscape, has led to a profusion of cybersecurity resources tackling distinctive security aspects.
Checking the cybersecurity option stack effectiveness is usually performed by means of pen-tests or, a lot more a short while ago, via crimson teaming – an work out aimed to map possible loopholes that would guide to a facts breach. When performed once or 2 times a year only, these assessments may well satisfy the compliance regulators. Nonetheless, as new threats emerge day by day, they fail to tell about the environment’s present-day security posture efficiently.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
In addition, these infrequent tests are unsuccessful to inform about prospective tool overlaps and are not created to protect against device sprawl, a recurrent prevalence in a area in which more than half of SOC facilities are overrun with redundant security applications and are swamped by way too lots of alerts.
Unrationalized security stacks are not only unnecessarily highly-priced, but they also crank out extra phony-optimistic phone calls, needlessly taxing security personnel stamina and growing the risk of lacking a critical inform.
The skill to measure every single tool’s efficacy, eradicate overlap and sustain ongoing regulate in excess of security baseline variability relies on ongoing accessibility to quantified data. This is at the main of what Extended Security Posture Administration (XPSM) provides to the table.
Understanding Prolonged Security Posture Administration
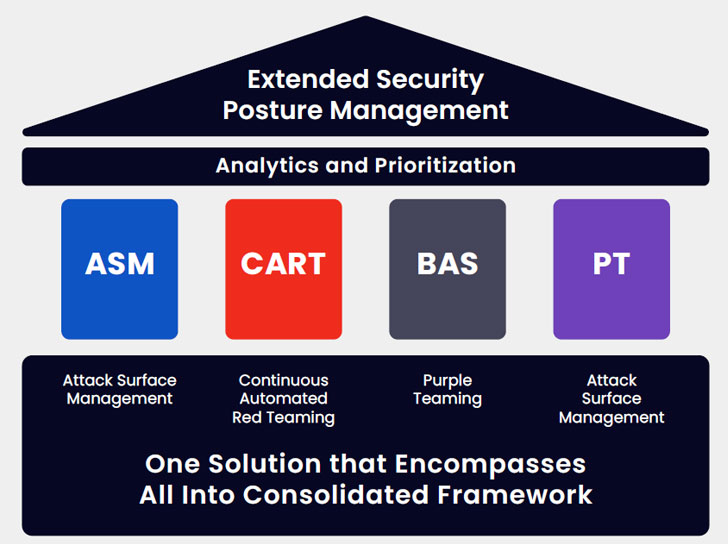
Prolonged Security Posture Administration (XSPM) is a multilayered system combining the abilities of Attack Surface Management (ASM), Breach and Attack Simulation (BAS), Steady Automated Crimson Teaming (CART), and Purple Teaming to continuously examine and score the infrastructure’s all round cyber resiliency.
This up-to-date detailed snapshot of the lively security posture, mixed with in-depth remediation course of action suggestions, is conducive to building rational company conclusions based on tricky information.
Using the granular evaluation of each individual specific instrument and of the security control configuration, an XSPM option delivers granular information and facts about each and every alternative made use of, the eventual overlap involving two or much more methods and the remaining security gaps. It then supplies specific tips about the remediation approach for each gap and optimization options for recognized overlaps.
The Edge of a Consolidated, Extensive Baseline
Security teams are systematically impressed by the big difference in possessing actionable information created, equally in enhancing the security posture and in rationalizing cybersecurity investing.
XSPM aids the security crew to deal with the frequent articles configuration churn and leverages telemetry to aid establish the gaps in security by producing up-to-day emerging threats feeds and providing additional test circumstances emulating TTPs that attackers would use, conserving DevSocOps the time necessary to build all those test conditions. When working XSPM validation modules, recognizing that the checks are timely, latest, and applicable enables reflecting on the efficacy of security controls and being familiar with exactly where to make investments to guarantee that the configuration, cleanliness and posture are maintained via the frequent improvements in the atmosphere.
By delivering visibility and maximizing relevancy, XSPM aids validate that each and every dollar put in added benefits risk reduction and resource efficacy by way of baselining and trending and automatically producing reviews made up of specific tips masking security hardening and software stack optimization it dramatically facilitates conversations with the board.
The change from rare to normal tests, manufactured probable by automation, allows the two the constant baseline variability checking and the quantified calculation of ROI realized by means of resource stack rationalization.
Additionally, it enables producing attack-primarily based vulnerability management by leveraging the results to prioritize patching.
As a bonus, checking an environment’s skill to stand up to the most up-to-date attacks can be done nearly at a click, and, if required, advised mitigation processes can be pushed ahead in the prioritized patching timetable.
George Washington’s adage “The finest protection is a very good offense” definitely applies to cybersecurity, and the ongoing offense is the only way to stay forward of the attackers’ development consistently.
Notice: This write-up was created by Arien Seghetti, Resolution Architect at Cymulate. For additional info, visit www.cymulate.com and sign up for a No cost Demo.
Observed this write-up attention-grabbing? Stick to THN on Facebook, Twitter and LinkedIn to examine a lot more special material we write-up.
Some components of this post are sourced from:
thehackernews.com


 Christmas Payroll Fears After Ransomware Hits Software Provider
Christmas Payroll Fears After Ransomware Hits Software Provider