There is no issue that attackers are going just after your sensitive account knowledge. Passwords have prolonged been a concentrate on of people hunting to compromise your ecosystem.
Why would an attacker just take the very long, difficult way if they have the keys to the front doorway?
No make any difference how extensive your security options are, safeguarding the a variety of techniques in your ecosystem, your group may perhaps probable be an simple concentrate on without having correct password security. An specially susceptible sort of password is a breached password, a.k.a “pwned” password.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
What is a breached password? How do you find breached passwords in your natural environment? How can businesses successfully defend their stop-consumers from employing these types of passwords?
The Hazard of Compromised Accounts
The IBM Expense of a Facts Breach Report 2020 pointed out compromised credentials as 1 of the primary contributors to malicious information breaches in the report’s important conclusions. It noted:
“Stolen or compromised qualifications ended up the most costly result in of destructive info breaches. A single in 5 organizations (19%) that endured a destructive information breach was infiltrated because of to stolen or compromised qualifications, raising the ordinary total value of a breach for these companies by nearly $1 million to $4.77 million. In general, destructive attacks registered as the most repeated root bring about (52% of breaches in the research), vs . human mistake (23%) or procedure glitches (25%), at an ordinary total price tag of $4.27 million.”
This facts can help to underscore the criticality of safeguarding account credentials and ensuring the protecting actions are in location to reduce the use of dangerous and even dangerous passwords in your business. A single stolen set of credentials may be all an attacker wants to compromise your information.
What Are Breached or “pwned” Passwords?
When talking about breached passwords in your environment, are we declaring your organization has been actively breached? No, not necessarily. Having said that, figuring out consumer accounts in your environment using passwords that have been breached in other organizations is particularly critical for your environment’s over-all security.
Hackers can access significant databases of breached passwords from previous information leaks or substantial scale dumps of account info. Databases of breached passwords are conveniently observed on the dark web as cybercriminals submit treasure troves of account info for other individuals to use and exploit. They use these to conduct brute force or password spraying attacks from your organization’s person accounts and many others.
You might speculate how using breached passwords from a earlier details breach or hack can be productive towards your setting. It will come down to how people believe, no make a difference which group is their employer. Buyers are inclined to use the similar kinds of patterns that many others use when deciding on passwords. The reality of the make a difference is a breached person password in one particular natural environment may possibly exist for a diverse consumer in an additional group. Making use of breached password databases, attackers have uncomplicated entry to big numbers of passwords to use against any variety of accounts throughout different organizations.
It is vital to shield your organization from the use of formerly breached passwords.
If a password gets to be breached right after remaining chosen as a user password, it is critical to have visibility of this risk in the ecosystem and proactively remediate the threat.
How can your organization obtain visibility to and guard from breached person passwords?
Indigenous Applications Are Not Sufficient
Microsoft Energetic Directory supplies many instruments and administration utilities for interacting with conclude-consumer accounts and handling passwords. On the other hand, none of the built-in applications delivered by Microsoft Active Listing give visibility to breached passwords. IT admins can obtain totally free PowerShell tools to test passwords versus little lists of breached passwords. Nevertheless, these applications could not be actively updated with the most recent breach details and must be run in an ad-hoc fashion to look at the setting periodically.
Utilizing these totally free PowerShell equipment to scan your setting for possible breached passwords can help to give some visibility. Nevertheless, at best, these supply a reactive technique and only give visibility to breached passwords in the natural environment, but supply no energetic security. These styles of instruments do not reduce customers from using breached passwords when configuring a password.
Is there a way to keep away from breached password use entirely? What about proactively finding breached passwords and forcing users to improve passwords that have come to be compromised?
Specops Breached Password Security
Specops Password Policy offers the tools that enterprises will need to fulfill the obstacle of breached passwords head-on. A powerful component of Specops Password Coverage is the Breached Password Defense. By making use of Specops Password Coverage, firms can very easily increase existing Lively Directory password procedures to include things like proactive breached password safety.
Vital features of Specops Breached Password Defense:
- Offers a record of breached passwords – Incorporates a mixture of countless numbers of distinctive resources of leaked passwords from very well-identified resources this kind of as haveibeenpwned.com as very well as obscure breached lists,
- Has quite a few billion breached passwords that are checked in your natural environment,
- Right away stops buyers from working with passwords that are contained on the breached password list,
- With Specops Breached Password Safety Comprehensive, if a consumer modifications their password to one particular in the leaked listing of passwords, they are notified by email or SMS,
- Their account is also flagged, forcing the user to adjust the password the upcoming time they log in.
There are a few of methods that Specops can retrieve the newest password checklist. Employing Comprehensive API, the Specops Arbiters communicates with the Specops API in real-time to be certain buyers are not applying a password observed on the most up-to-date breached checklist curated by Specops.
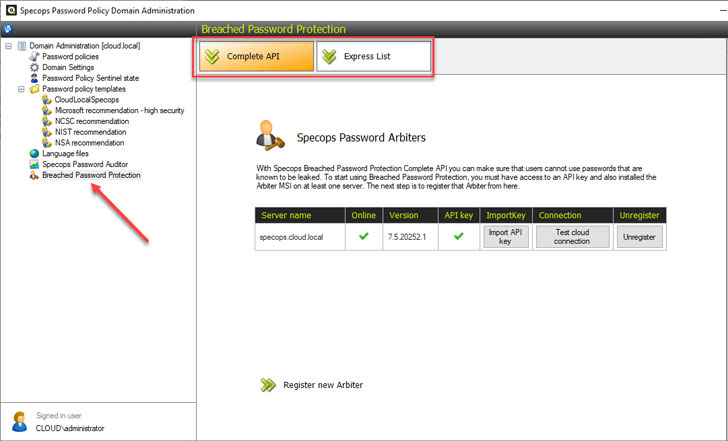 Specops Breached Password Protection with Entire API checks
Specops Breached Password Protection with Entire API checks
IT administrators can also download the most current breached password record utilizing the Convey List selection. Specops notes when new lists are obtainable. At the time the newest listing is downloaded, it is checked domestically for breached entries observed in Lively Directory.
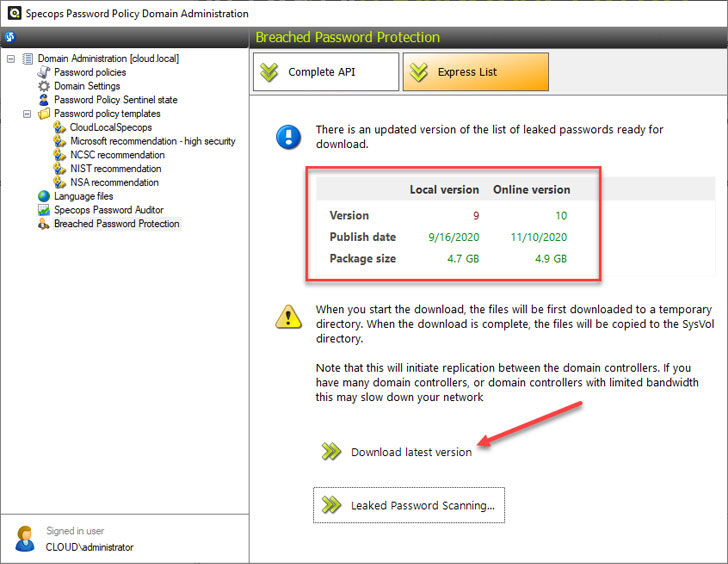 Working with the Specops Specific Listing to download the breached password list domestically
Working with the Specops Specific Listing to download the breached password list domestically
Blocking buyers from employing breached passwords
How do you make use of Specops Breached Password Defense to stop conclude-users from making use of these? Specops Password Coverage helps make this straightforward. In the Specops Password Plan options, you can configure the password policy to do the pursuing:
- Avert buyers from modifying to a leaked password
- Drive customers to improve leaked passwords when the Breached Password Security Categorical record is current
- Notify users when they are pressured to adjust password
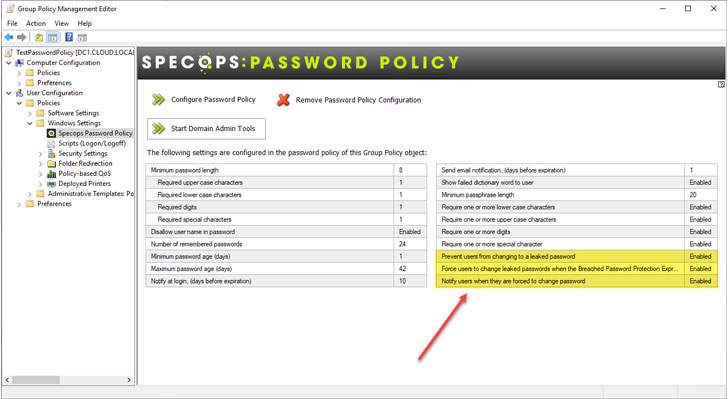 Specops Password Coverage with Breached Password Defense
Specops Password Coverage with Breached Password Defense
Specops Password Coverage assists transmit the password needs to stop-people in a a lot more intuitive way than the indigenous Windows password improve messages conclusion-consumers normally see.
Under is an case in point of the information received by a user when attempting to alter their password to a person on the breached password list.
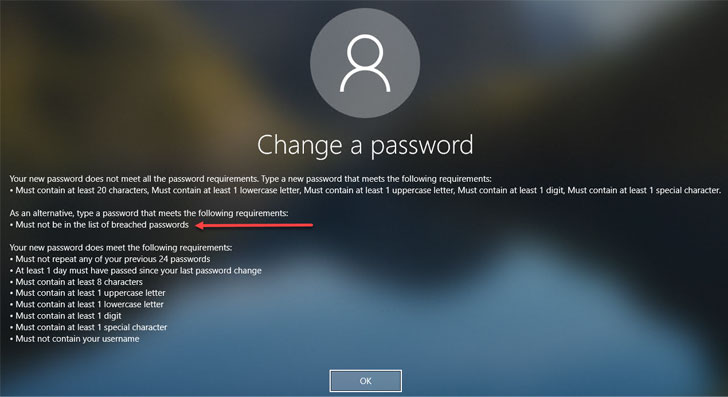 Password modify message for a failed password transform request owing to a breached password
Password modify message for a failed password transform request owing to a breached password
Conclusion
Guarding your surroundings from the use of breached passwords is critical to making certain person accounts are protected, and enterprise-critical data is safeguarded. There are no built-in indigenous Energetic Listing instruments that give visibility to these harmful user account passwords. Whilst you can obtain and use customized PowerShell scripts to scan your Active Listing environment, these demand handbook procedures, and the code or lists may possibly be outdated.
Specops Password Plan with Breached Password Security is a excellent remedy to proactively secure in opposition to the use of breached passwords in the environment. It seamlessly integrates with your current Energetic Listing password insurance policies configured by Team Plan Objects (GPOs) and presents authentic-time safety in opposition to breached passwords.
Study additional about Specops Password Plan right here.
Observed this short article attention-grabbing? Adhere to THN on Facebook, Twitter and LinkedIn to read extra special content material we post.
Some areas of this write-up are sourced from:
thehackernews.com

 Hackers-For-Hire Group Develops New ‘PowerPepper’ In-Memory Malware
Hackers-For-Hire Group Develops New ‘PowerPepper’ In-Memory Malware