As if the exponential increase in phishing cons and malware attacks in the last 5 several years wasn’t ample, the COVID-19 disaster has worsened it additional.
The current state of affairs has presented a viable chance to cybercriminals to find a way to goal men and women, modest and massive enterprises, governing administration companies.
According to Interpol’s COVID-19 Cybercrime Examination Report, dependent on the suggestions of 194 countries, phishing/scam/fraud, malware/ransomware, destructive domains, and fake information have emerged as the largest electronic threats throughout the globe in the wake of the pandemic.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
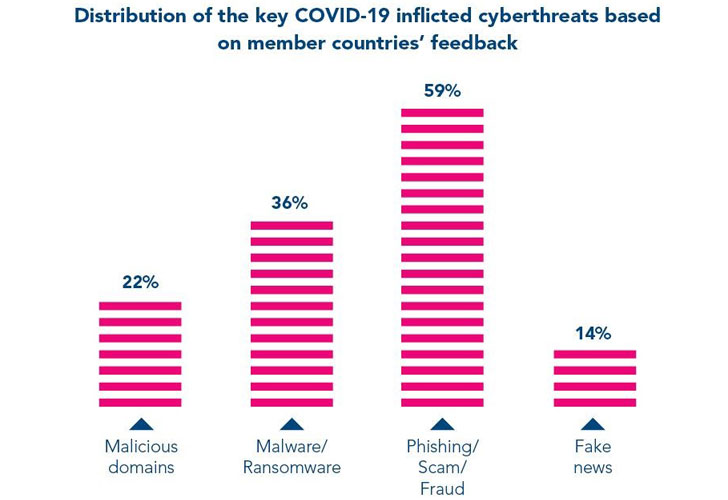 Image resource: interpol.int
Image resource: interpol.int
There are mainly two factors for rising cyber threats in 2020:
- Most of the populace is doing work, studying, buying, or running their enterprise from residence, in which they’re making use of private units from the home/community internet link, which are normally unsafe and consequently highly vulnerable to cybercrimes.
- The cybercriminals are using the COVID-19 topic to exploit men and women and enterprises as a result of malicious e-mails and domains. For instance, a lot of scammers have rolled out strategies supplying COVID-19 vaccines, absolutely free health-related exams and screening kits, tax rebates for donation to pandemic relief resources, facts on COVID-19 instances, and new job options due to the economic downturn. Some have even launched pretend e-commerce web sites advertising COVID-19 safety, health and fitness, and sanitization goods.
Let’s choose a appear at a few illustrations of cyber threats and security breaches that have taken place in 2020.
Cons
- In April 2020, swindlers impersonated the Globe Health and fitness Organization (WHO) to send e-mails to the community looking for donations to a fictitious COVID-19 fund.
- In March 2020, the Division of Justice in the United States submitted a lawful charm in the federal courtroom to shut down a web-site known as coronavirusmedicalkit[.]com, which claimed to promote free vaccine kits.
Phishing
- A phishingscam marketing campaign despatched out fake Zoom invitations to personnel from HR. The concept was to phish out their passwords.
- Quite a few UK citizens gained an e-mail from a faux governing administration ID telling them to claim a tax refund to defend versus the COVID-19 crisis.
Malware
- The Powershell malware attacks in 2020 have witnessed a sharp improve of 117% in North America.
- Ryuk has emerged as one particular of the greatest malware threats to US hospitals and health care suppliers in 2020.
Approaches to Safeguard In opposition to COVID-19 Electronic Threats
Cyber risk administration phone calls for both of those preventive and detective measures stated below:
1 — Teach Your Workers
Most phishing e-mails show up so authentic that your staff members are very likely to open the attachment or embedded hyperlink devoid of verifying the sender’s e-mail id or the information and facts in the message’s human body.
Develop cybersecurity consciousness among the your employees to enable them identify unauthenticated e-mails. Inform them to double-look at the sender’s e-mail address and seem for grammatical glitches or unusual requests. If they suspect nearly anything, they ought to straight away get in contact with the IT group instead of forwarding the e-mail to co-personnel.
2 — Encrypt and Backup Knowledge
You have to use whole-disk encryption program to encrypt all delicate knowledge of your enterprise, consumers, and workers.
It is also generally a very good concept to get a system backup of your databases, data files, and databases at regular intervals.
The normal rule of backup is 3-2-1: build at minimum 3 copies, two of which really should be on unique mediums (devices/cloud), and a single duplicate should really be off-web-site for catastrophe recovery.
3 — Fortify Cybersecurity Coverage for Remote Functioning
It is important to develop a rigid rulebook for your employees, laying down the protocol for utilizing home computing devices and internet link. They need to use a protected internet connection, stay away from the use of office environment devices for personal use, and keep formal data files/information only on business storage devices.
Also, make confident that your company implements robust firewall regulations and multi-layer authentication for VPN, critical business enterprise techniques, and any other distant network connections. Let your workers know the company-authorised apps and collaboration resources they have to use.
4 — Use Anti-Virus Methods
This may sound like primary security protocol, but it is very critical to install advanced and dependable anti-virus software package on your corporation servers and units.
5 — Protected Your Web and Cell Programs
With COVID-19 pushing the globe to embrace electronic on each individual entrance, your web and mobile applications are extra at risk from cyber threats and security violations. Therefore, you ought to proactively monitor software security hazards and acquire preventive actions to mitigate them.
You can do so by employing AppTrana, a risk-based mostly, completely managed software security solution offered by Indusface. AppTrana delivers true-time defense from OWASP exploits, DDOS attacks, Bot Mitigation, and Zero-Working day attacks.
You can also take into consideration Indusface WAS, which is a thorough web application vulnerability detection option. It presents Automated DAST Scanner merged with on-desire Guide Penetration Screening and wrong-positive elimination by way of handbook verification.
If you are wanting for cell security answers, then Indusface MAS runs in-depth Pen-testing with multiplatform coverage, which includes iOS, Android, and Windows, for vulnerability detection.
Summary
COVID-19 has set the pressing need to have on organizations to re-strategize their cybersecurity coverage to hold digital threats at bay.
It is also vital to realize that cyber threats are in this article to continue to be even just after the ongoing pandemic since world digital utilization is expected to improve repeatedly in the coming decades.
That’s why, it would assist if you get prepared on all fronts to overcome the cyber-attacks efficiently.
Observed this post interesting? Follow THN on Fb, Twitter and LinkedIn to browse much more exclusive content we write-up.
Some elements of this article are sourced from:
thehackernews.com

 Law Enforcement Seizes Joker’s Stash — Stolen Credit Card Marketplace
Law Enforcement Seizes Joker’s Stash — Stolen Credit Card Marketplace