An ever-evolving and rampant form of cybercrime that targets e-mails as the opportunity medium to carry out fraud is regarded as Company Email Compromise.
Focusing on business, federal government as perfectly as non-income corporations, BEC can lead to big amounts of data loss, security breach, and compromised economic property.
It is a common misunderstanding that cybercriminals usually lay their target on MNCs and business-level organizations. SMEs these days are just as considerably a goal to email fraud as the bigger sector gamers.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
How Can BEC Impact Businesses?
Illustrations of BEC include things like subtle social engineering attacks like phishing, CEO fraud, faux invoices, and email spoofing, to identify a number of. It can also be termed an impersonation attack wherein an attacker aims to defraud a organization by posing people in authoritarian positions. Impersonating folks like the CFO or CEO, a business lover, or anybody you will blindly put your belief in is what drives these attacks’ good results.
February of 2021 captured the functions of the Russian cyber gang Cosmic Lynx as they took a innovative approach in the direction of BEC. The group had now been linked to conducting more than 200 BEC strategies considering that July 2019, concentrating on around 46 nations around the world around the world, focusing on giant MNCs that have a global presence. With exceptionally nicely-written phishing e-mail, they make it not possible for folks to differentiate in between actual and faux messages.
Distant-working has built video conferencing programs indispensable entities, post-pandemic. Cybercriminals are having gain of this circumstance by sending fraudulent e-mail that impersonate a notification from the video clip conferencing system, Zoom. This is aimed at thieving login qualifications to carry out massive business facts breaches.
It is crystal clear that the relevance of BEC is swiftly surfacing and expanding in recent occasions, with danger actors coming up with extra refined and ground breaking methods to get away with fraud. BEC has an effect on much more than 70% of companies worldwide and prospects to the decline of billions of pounds each individual year.
This is why marketplace authorities are coming up with email authentication protocols like DMARC to supply a large degree of safety towards impersonation.
What is Email Authentication?
Email authentication can be referred to as a bevy of approaches deployed to deliver verifiable information about the origin of email messages. This is finished by authenticating the area possession of the mail transfer agent(s) involved in the concept transfer.
Easy Mail Transfer Protocol (SMTP), which is the industry standard for email transfer, has no this kind of in-crafted feature for concept authentication. This is why exploiting the deficiency of security will become exceedingly quick for cybercriminals to launch email phishing and domain spoofing attacks.
This highlights the want for effective email authentication protocols like DMARC that actually provides its claims!
Actions to Prevent BEC with DMARC
Step 1: Implementation
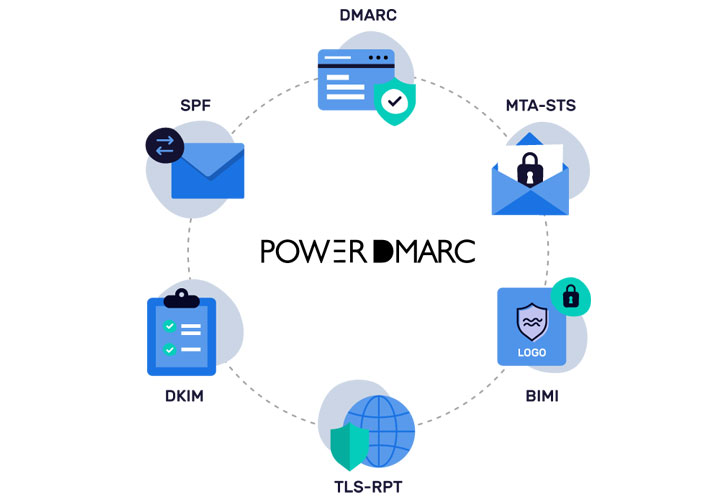
The first move to combating BEC is in fact configuring DMARC for your domain. Area-based Message Authentication, Reporting, and Conformance (DMARC) works by using SPF and DKIM authentication criteria to validate email messages sent from your area.
It specifies to acquiring servers how to reply to email messages that fall short possibly/the two of these authentication checks, supplying the domain operator manage in excess of the receiver’s response. For this reason for Applying DMARC, you would need to:
- Identify all valid email sources licensed for your domain
- Publish SPF file in your DNS to configure SPF for your domain
- Publish DKIM file in your DNS to configure DKIM for your domain
- Publish DMARC record in your DNS to configure DMARC for your area
To stay clear of complexities, you can use PowerDMARC’s cost-free instruments ( cost-free SPF report generator, absolutely free DKIM file generator, totally free DMARC file generator) to produce records with the appropriate syntax right away and publish in your domain’s DNS.
Stage 2: Enforcement
Your DMARC plan can be set to:
- p=none (DMARC at checking only messages failing authentication would nonetheless be shipped)
- p=quarantine (DMARC at enforcement messages failing authentication would be quarantined)
- p=reject (DMARC at utmost enforcement messages failing authentication would not be shipped at all)
We would recommend you to start using DMARC with a plan enabling checking only so that you can preserve a tab on the email move and delivery issues. Even so, this sort of a policy would not supply any safety from BEC.
This is why you would finally want to change to DMARC enforcement. PowerDMARC will help you seamlessly change from checking to enforcement in no time with a coverage of p=reject, which will support specify to getting servers that an email despatched from a destructive supply making use of your domain would not be delivered to your recipient’s inbox at all.
Phase 3: Monitoring and Reporting
You have established your DMARC coverage at enforcement and have productively minimized BEC, but is that plenty of? The response is no. You however need to have an comprehensive and effective reporting mechanism to keep an eye on email stream and reply to any delivery issues. PowerDMARC’s multi-tenant SaaS platform assists you:
- remain in regulate of your domain
- visually keep an eye on authentication benefits for each individual email, person, and domain registered for you
- take down abusive IP addresses that check out impersonating your manufacturer
DMARC reviews are obtainable on the PowerDMARC dashboard in two major formats:
- DMARC mixture studies (offered in 7 diverse views)
- DMARC forensic stories (with encryption for enhanced privacy)
A fruits of DMARC implementation, enforcement, and reporting assistance you substantially lessen the chances of falling prey to BEC frauds and impersonation.
With Anti-Spam Filters, Do I Still Need DMARC?
Certainly! DMARC operates quite differently from your ordinary anti-spam filters and email security gateways. Even though these options typically arrive integrated with your cloud-primarily based email exchanger solutions, they can only offer protection against inbound phishing attempts.
Messages sent from your area nonetheless remain under the threat of impersonation. This is exactly where DMARC actions in.
Additional Recommendations for Improved Email Security
Generally remain beneath the 10 DNS Lookup Restrict.
Exceeding the SPF 10 lookup limit can completely invalidate your SPF report and cause even genuine e-mails to are unsuccessful authentication.
In these kinds of cases, if you have your DMARC set to reject, authentic emails will fail to get delivered. PowerSPF is your computerized and dynamic SPF history flattener that mitigates SPF permerror by serving to you keep under the SPF difficult limit.
It vehicle-updates netblocks and scans for variations manufactured by your email provider companies to their IP addresses continuously, devoid of any intervention from your aspect.
Be certain TLS Encryption of E-mails in Transit
Although DMARC can protect you from social engineering attacks and BEC, you nonetheless require to equipment up from pervasive checking attacks like Male-in-the-middle (MITM).
This can be carried out by guaranteeing that a link secured above TLS is negotiated among SMTP servers each time an email is despatched to your domain.
PowerDMARC’s hosted MTA-STS helps make TLS encryption necessary in SMTP and comes with a clear-cut implementation treatment.
Get Studies on Issues in Email Delivery
You can also help SMTP TLS reporting to get diagnostic studies on email supply issues after configuring MTA-STS for your domain. TLS-RPT assists you get visibility into your email ecosystem and better reply to issues in negotiating a secured connection primary to supply failures.
TLS stories are available in two views (aggregate stories per final result and per sending supply) on the PowerDMARC dashboard.
Amplify Your Brand name Remember with BIMI
With BIMI (Brand name Indicators for Concept Identification), you can consider your manufacturer remember to a whole new degree by supporting your recipients visually recognize you in their inboxes.
BIMI functions by attaching your exceptional brand name logo to every email you ship out from your domain. PowerDMARC can make BIMI implementation uncomplicated with just 3 easy methods on the user’s part.
PowerDMARC is your a person-stop place for an array of email authentication protocols, together with DMARC, SPF, DKIM, BIMI, MTA-STS, and TLS-RPT. Signal up nowadays to get your free of charge DMARC Analyzer demo!
Discovered this short article intriguing? Stick to THN on Facebook, Twitter and LinkedIn to go through a lot more distinctive material we article.
Some elements of this report are sourced from:
thehackernews.com


 Chinese Hackers Had Access to a U.S. Hacking Tool Years Before It Was Leaked Online
Chinese Hackers Had Access to a U.S. Hacking Tool Years Before It Was Leaked Online