Ransomware is not a new attack vector. In actuality, the initially malware of its kind appeared a lot more than 30 a long time back and was distributed by means of 5.25-inch floppy disks. To shell out the ransom, the victim experienced to mail revenue to a P.O. Box in Panama.
Fast ahead to right now, very affordable ransomware-as-a-company (RaaS) kits are available on the dark web for any person to obtain and deploy and attackers have an infinite amount of channels readily available to them to infiltrate businesses as a consequence of reliance on cloud and cellular technologies.
Initiating a ransomware attack is all about discretely gaining entry. And as staff members can now accessibility your facts from anyplace, you have shed visibility into how they do so. To safeguard towards these attacks, you’re not just looking for malware, you need steady insights into your end users, the endpoints they use and the applications and data they access.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Lookout, a leader in endpoint-to-cloud security, has published an interactive infographic to enable you visualize how a ransomware attack happens and understand how to guard your information. Lookout will use this blog to set up 1) the weather that resulted in $20-billion bucks in ransom payments in 2021, and 2) how you can guard your firm from these ongoing threats.
Work from everywhere improves both equally productiveness and attacker infiltration
While the actual malware utilised to keep your knowledge hostage is referred to as “ransomware,” that’s not what you need to aim on. Just before something is deployed, attackers have to have accessibility to your infrastructure.
Currently, end users are accessing knowledge applying networks you will not management and units you really don’t control, rendering whatsoever on-premises security actions you had obsolete.
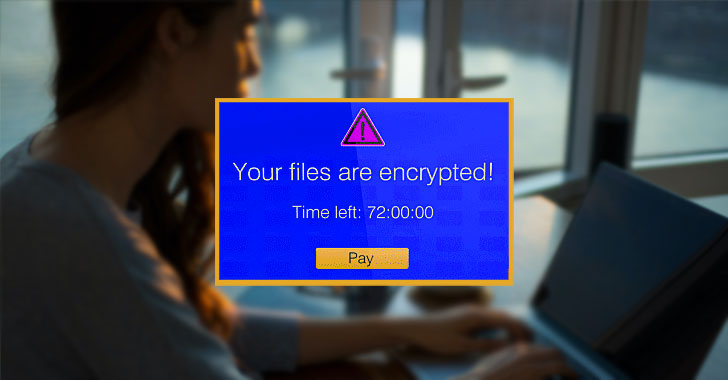
This suggests risk actors can start phishing attacks to compromise consumer credentials or exploit a vulnerable app with small consequence. And after they are within your infrastructure, they quickly deploy malware to create persistent backdoors that enable them to arrive and go as they make sure you. If they escalate privileges, it gets to be just about not possible to stop them from relocating all over laterally and holding your knowledge hostage.
Step-by-stage: how to secure versus ransomware
There are a number of measures that take place amongst an attacker accessing your infrastructure and inquiring for a ransom. These measures are outlined in the anatomy of a ransomware attack infographic and below is a high-amount rundown of what comes about and how you can guard your corporation.
1 — Block phishing attacks and cloak web-enabled apps
One particular of the easiest strategies attackers gain obtain is by getting above a person account by compromising qualifications with phishing attacks. It’s critical to be ready to inspect web traffic on any unit to block these attacks from influencing both Personal computer and cell customers. This will make certain that ransomware operators are not able to kick off their attacks by compromising accounts.
Threat actors will also crawl the web to obtain vulnerable or exposed internet-struggling with infrastructure to exploit. A lot of organizations have apps or servers uncovered to the web to allow distant entry, but this indicates attackers can come across them and search for vulnerabilities. Cloaking these applications from discovery is a crucial defense tactic. This will help you transfer absent from the unbridled accessibility presented by VPNs and make absolutely sure only licensed consumers accessibility the knowledge they require.
2 — Detect and reply to anomalous behaviors
If attackers handle to enter your infrastructure, they will start off shifting laterally to perform reconnaissance. This is to obtain extra vulnerabilities with the ultimate target of uncovering delicate facts. Some of the actions they could just take consist of shifting your options to lessen security permissions, exfiltrating facts and uploading malware.
Some of these ways may perhaps not be outright malicious behavior but can be deemed anomalous habits. This is wherever an knowledge of consumer and gadget habits and segmenting entry at the software amount will become critical. To end lateral motion, you need to have to be certain no consumers have free roam of your infrastructure and that they are not performing in a destructive manner. It is really also crucial to be equipped to detect too much or misconfigured privileges so that you can avoid variations to your app and cloud posture.
3 — Render facts useless for ransom with proactive encryption
The closing move of a ransomware attack is to maintain your knowledge hostage. In addition to encrypting the information and locking your admins out, the attacker could also exfiltrate some info to use as leverage, then delete or encrypt what’s left in your infrastructure.
Exfiltration and affect are commonly when the attacker finally reveals their presence. The modifications they make to data, no matter of if it truly is at relaxation or in motion, will set off alarm bells and they will demand payments. However, you can make all their initiatives for naught if that data is encrypted proactively by your security platform and renders it completely ineffective to the attacker. Encryption is a critical component of any information loss prevention (DLP) tactic, and triggering it off of contextual information safety guidelines can support you shield your most sensitive info from compromise.
Securing against ransomware: position goods versus a unified system
A ransomware attack is just not just a one function it truly is a persistent danger. To protected your business, you want a complete photograph of what is going on with your endpoints, consumers, applications and facts. This assures that you can block phishing attacks, cloak web applications, detect and react to lateral motion, and protect your facts even if it is exfiltrated and held for ransom.
Traditionally, companies have procured new instruments to mitigate new problems. But this style of strategy will not do the job with threats like ransomware. While you may possibly have some telemetry into your users’ accessibility activity, the well being of their corporate-owned device and how your info is managed, your security group will have to manage numerous consoles that really don’t perform with every single other.
Lookout realize the need for a system tactic and have created a Security Assistance Edge (SSE) platform that contains DLP, Person and Entity Behavior Analytics (UEBA) and Business Digital Rights Management (EDRM).
With a platform that delivers integrated insights into all the things that is occurring within your organization, we enable you to safe sensitive info without having hindering productivity. Lookout’s SSE platform was lately named a Visionary by the 2022 Gartner Magic Quadrant for SSE. Lookout also scored in the best 3 for all SSE use conditions in the 2022 Gartner Critical Capabilities for SSE.
To study a lot more about crucial lessons you can understand from huge ransomware attacks in 2021, and how to secure your sensitive knowledge, obtain Lookout’s most up-to-date guidebook on ransomware.
Uncovered this report interesting? Abide by THN on Fb, Twitter and LinkedIn to study far more special articles we write-up.
Some parts of this report are sourced from:
thehackernews.com

 Booz Allen Hamilton wins NASA’s $622m CyPrESS contract
Booz Allen Hamilton wins NASA’s $622m CyPrESS contract