Quite a few enterprises are presently on the lookout at how to bolster security throughout their group as the pandemic and distant function condition continues to progress in direction of the finish of the calendar year. As corporations go on to put into practice security steps to protect company-critical knowledge, there is an extremely significant area of security that often receives disregarded – passwords.
Weak passwords have lengthy been a security nightmare for your small business. This features reused and pwned passwords. What are these? What instruments are readily available to help safeguard against their use in your environment?
Various forms of hazardous passwords
There are a lot of unique styles of harmful passwords that can expose your corporation to huge risk. One way that cybercriminals compromise environments is by creating use of breached password info. This allows launching password spraying attacks on your setting.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Password spraying consists of making an attempt only a several passwords in opposition to a large variety of stop-users. In a password spraying attack, cybercriminals will normally use databases of breached passwords, a.k.a pwned passwords, to proficiently try out these passwords in opposition to person accounts in your surroundings.
The philosophy below is that across quite a few diverse businesses, customers tend to believe in quite identical techniques when it arrives to generating passwords they can remember. Normally passwords uncovered in other breaches will be passwords that other buyers are making use of in totally different environments. This, of system, improves risk given that any compromise of the password will expose not a single account but multiple accounts if utilised throughout distinct devices.
Pwned passwords are unsafe and can expose your firm to the dangers of compromise, ransomware, and info breach threats. What forms of applications are readily available to assistance find and mitigate these sorts of password challenges in your setting?
Applications Out there to enable with password security
There are a couple tools readily available that can assist with password security in your natural environment by way of API phone calls as well as utilizing cloud resources, both on-premises or in cloud environments. Let us glance at a few of these.
- “Have I Been Pwned” (HIBP) API
- Azure Advert Password Defense – can be utilised on-premises as well
“Have I Been Pwned” (HIBP) API
The Have I Been Pwned website, operated by security qualified Troy Hunt, is a precious source for the security community. Troy Hunt has delivered a range of resources on the web page that permit companies to make use of and obtain consciousness of several security threats that exist on the scene right now.
The HIBP web site was formulated in reaction to information breach occasions that frequently materialize when user qualifications are uncovered about and in excess of once more with the exact same passwords. Employing HIBP, businesses can discern if passwords in their natural environment have formerly been uncovered to knowledge breach functions.
Troy Hunt has provided an HIBP API that is freely accessible and makes it possible for earning authentic-time API calls from several software apps to the HIBP API to look at passwords used throughout numerous computer software sorts and lots of other reasons. Some of the API calls and details that can be returned include things like the following:
- Acquiring all breaches for an account
- Finding all breached web pages in the procedure
- Receiving a one breached website
- Receiving all information classes
Hats off to Troy for furnishing an superb source for the group that can be eaten and applied freely to assist bolster the security of passwords in their environments.
To properly consume the HIBP API, it does require that corporations have some progress skills in-house to make use of the useful resource. This might be a blocker for many corporations that would like to make use of the resource.
Azure Advertisement Password Security
Microsoft has presented a tool referred to as Azure Advertisement Password Security that detects and blocks acknowledged weak passwords and their variants. It can also block terms that are unique to your surroundings, this kind of as blocking passwords that may perhaps comprise the enterprise title as an instance.
The device can also be deployed on-premises as properly and makes use of the same lists of passwords, like world wide and tailor made banned passwords, that are configured in Azure to guard on-premises accounts. Using Azure Ad Password Defense employs a mechanism that checks passwords during the password alter party for a consumer to avert people from configuring weak or in any other case blocked passwords.
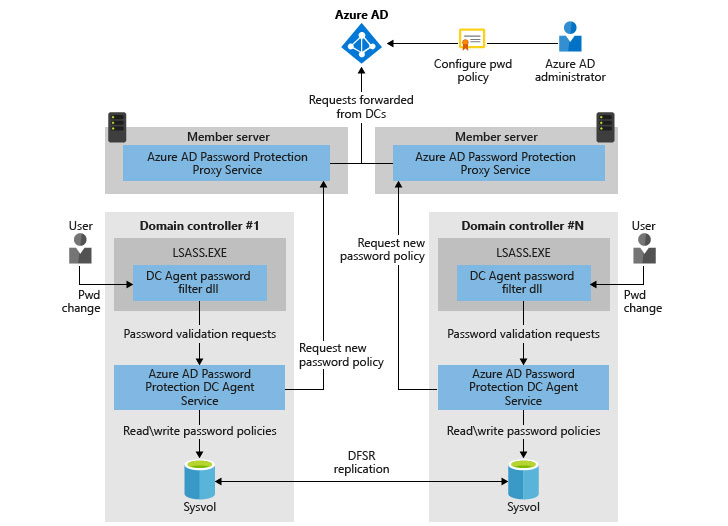 Architectural overview of Azure Advertisement Password Safety (image courtesy of Microsoft)
Architectural overview of Azure Advertisement Password Safety (image courtesy of Microsoft)
Making use of the Azure Ad Password Safety resource supplies respectable security, about and above the default security that you get by only applying Active Listing password insurance policies. Having said that, there are a variety of a lot less than desirable facets to Azure Advert Password Defense, which include the following:
- It does not consist of breached passwords – As reviewed, breached or pwned passwords are extremely risky. There is a possibility that some in your firm are applying passwords that have been uncovered in a previous breach. Azure Advert Password Protection has no look at for these.
- Tailor made banned passwords have boundaries – The currently banned passwords can only have 1000 words or considerably less and need to be (4) figures or additional extended.
- No control over end-consumer working experience – There is no manage more than the concept that stop-customers acquire when a banned password is turned down with Azure Advert Password Defense. They only see the regular Windows mistake that the “password did not meet up with the demands” mistake.
Quickly safeguard versus pwned passwords
Any defense that can be presented in opposition to weak passwords and specified varieties of banned passwords is greater than the different of no security higher than default password insurance policies. Nonetheless, there is a device that can effortlessly shed light on equally password reuse and also pwned or breached passwords in your natural environment.
Specops Password Auditor is a totally free device at this time made available by Specopssoft that offers IT admins with the ability to scan their natural environment for many various kinds of password dangers. It will help to triumph over the problems of the aforementioned tools and other folks that are offered.
With Password Auditor, you can locate:
- Blank passwords
- Breached passwords
- Equivalent passwords
- Expiring passwords
- Expired Passwords
- Password procedures
- Admin accounts
- Password not needed
- Password under no circumstances expires
- Stale admin accounts
The good matter about the Specops Password Auditor device is that it constantly pulls the most current breached password lists from the Specops’ on the internet databases so that you are always examining your setting with the most recent security details accessible.
In addition, the tool is an uncomplicated Windows installation with no developer abilities needed to query APIs and supplies excellent visibility to the several various forms of password hazards in your natural environment. This lets mitigating these correctly.
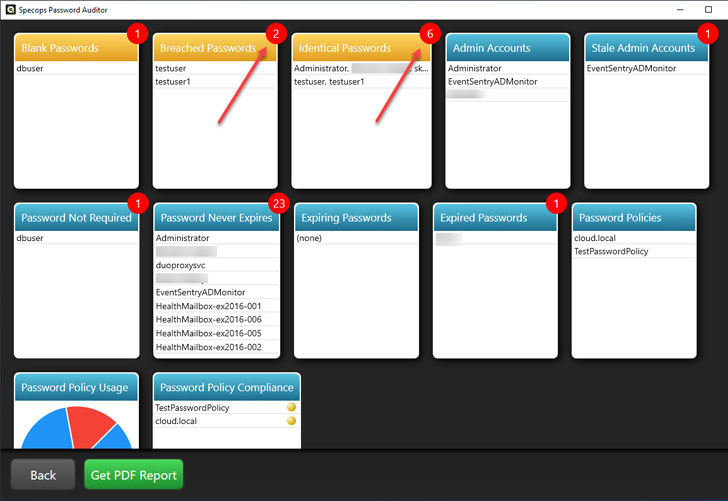 Specops Password Auditor supplies true-time scans of Lively Directory for reused and breached passwords
Specops Password Auditor supplies true-time scans of Lively Directory for reused and breached passwords
In addition, businesses can make use of Specops Password Coverage, which makes it possible for proactively mitigating password pitfalls in the environment. Using Specops Password Plan, you can produce custom and leaked password lists and password hash dictionaries centered on Specops much more than 2 billion leaked passwords. You can also efficiently block common character substitutions and keyboard styles.
Concluding Views
Obtaining breached passwords in your setting really should be a priority as part of your all round security plan to bolster finish-person security and shield business-critical data. Whilst there are instruments readily available from several sources to enable obtain and block weak passwords, there is typically a barrier of entry to applying many of people accessible for intake.
Specops provides a seriously great combination of instruments that makes it possible for proficiently finding breached passwords together with proactively blocking and enforcing password procedures that actively verify to see if current passwords are located on lists of passwords collected from earlier breaches.
By providing owing consideration to password security in your setting, you make the job of cybercriminals considerably far more difficult. They will not have an effortless way into your ecosystem by acquiring weak passwords.
Uncovered this report intriguing? Stick to THN on Facebook, Twitter and LinkedIn to read far more special content material we publish.
Some pieces of this posting are sourced from:
thehackernews.com

 CERT/CC Aims to Tackle FUD with New CVE-Naming Bot
CERT/CC Aims to Tackle FUD with New CVE-Naming Bot