A week immediately after cybersecurity scientists disclosed a flaw in the well known GO SMS Pro messaging application, it seems the builders of the application are silently having steps to take care of the issue from behind the scenes.
The security misstep built it possible for an attacker to occur up with a trivial script to access media data files transferred in between buyers, together with non-public voice messages, images, and movies, stored on an unauthenticated, publicly available server.
Although the conduct was observed on model 7.91 of GO SMS Pro for Android, the app makers have since launched 3 subsequent updates, two of which (v7.93 and v7.94) were pushed to the Google Enjoy Store immediately after community disclosure of the flaw and Google’s removing of the application from the marketplace.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Google reinstated the app back again to the Engage in Shop on November 23.
Now subsequent an assessment of the updated versions, Trustwave researchers claimed, “GOMO is trying to deal with the issue, but a complete take care of is even now not offered in the app.”
v7.93 of the application saw the builders entirely turning off the potential to deliver media data files, whilst the next update (v7.94) has introduced again the performance, albeit in a damaged form.
“In v7.94, they are not blocking the capacity to add media in the app, but the media does not surface to go anywhere,” the researchers reported. “The recipient does not receive any true textual content both with or without having attached media. So it seems they are in the method of seeking to correct the root dilemma.”
What’s a lot more, Trustwave confirmed that more mature media shared prior to the advisory are however available, which include a cache of delicate information and facts like driver’s licenses, wellbeing insurance account numbers, authorized files, and photographs of a a lot more “passionate” character.
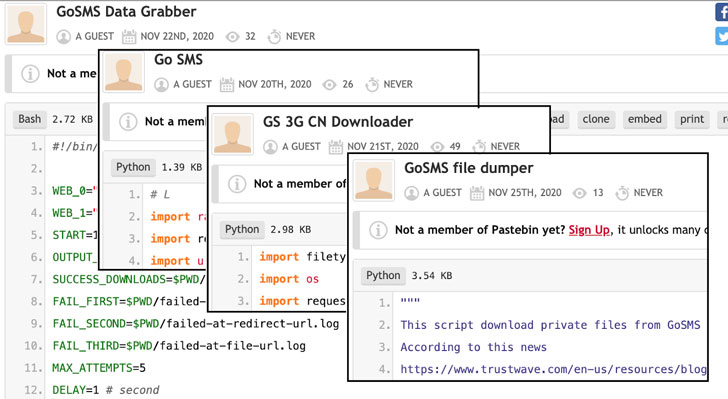
Troublingly, not only applications and exploits leveraging this vulnerability have been released on Pastebin and Github underground community forums look to be sharing illustrations or photos downloaded from GO SMS servers specifically.

Provided the lack of interaction from the application builders and the actuality that outdated facts is becoming actively leaked, it is proposed to refrain from making use of the application right up until the issues are completely patched.
“We also feel it would be a very good concept for Google to get this application again down,” the researchers reported.
Uncovered this post exciting? Follow THN on Facebook, Twitter and LinkedIn to examine additional special information we post.
Some pieces of this short article are sourced from:
thehackernews.com


 #thinkcybersec: Reconsider Hiring Strategies to Meet 2021’s Digital Challenges
#thinkcybersec: Reconsider Hiring Strategies to Meet 2021’s Digital Challenges