Cybersecurity scientists are warning of ongoing attacks coordinated by a suspected Chinese-talking menace actor targeting the Afghanistan governing administration as component of an espionage campaign that may possibly have had its provenance as considerably back again as 2014.
Israeli cybersecurity agency Test Position Exploration attributed the intrusions to a hacking group tracked beneath the moniker “IndigoZebra,” with previous action aimed at other central-Asian international locations, which include Kyrgyzstan and Uzbekistan.
“The threat actors at the rear of the espionage leveraged Dropbox, the well-liked cloud-storage company, to infiltrate the Afghan Nationwide Security Council (NSC),” the researchers said in a technical write-up shared with The Hacker Information, including they “orchestrated a ministry-to-ministry fashion deception, wherever an email is despatched to a substantial-profile focus on from the mailboxes of another higher-profile target.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

IndigoZebra initially came to gentle in August 2017 when Kaspersky in depth a covert procedure that singled out former Soviet Republics with a broad swath of malware this sort of as Meterpreter, Poison Ivy RAT, xDown, and a earlier undocumented piece of malware identified as xCaon.
Check out Point’s investigation into the attacks commenced in April when NSC officers commenced obtaining entice email messages allegedly claiming to be from the Administrative Office of the President of Afghanistan.

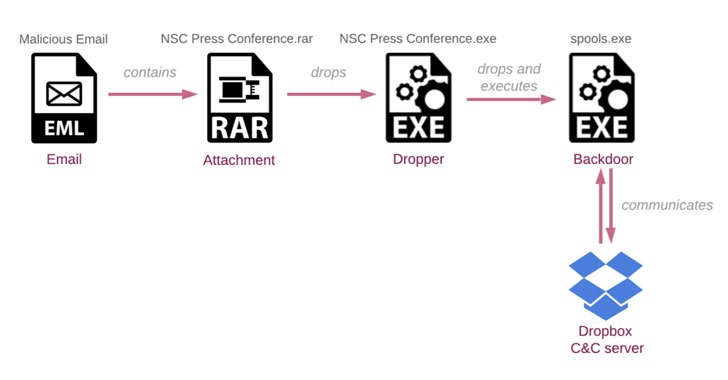
Even though the concept urged the recipients to review modifications in an attached document related to a pending NSC press convention, opening the decoy file — a password-protected RAR archive (“NSC Press convention.rar”) — was discovered to bring about an an infection chain that culminated in the installation of a backdoor (“spools.exe”) on the focused system.
On top of that, the attacks funneled malicious instructions into the target machine that have been camouflaged using the Dropbox API, with the implant building a exclusive folder for just about every compromised host in an attacker-controlled Dropbox account.
The backdoor, dubbed “BoxCaon,” is able of thieving private facts saved on the gadget, working arbitrary commands, and exfiltrating the effects back again to the Dropbox folder. The instructions (“c.txt”) them selves are put in a independent sub-folder named “d” in the victim’s Dropbox folder, which is retrieved by the malware prior to execution.

BoxCaon’s relationship to IndigoZebra stems from similarities shared by the malware with xCaon. Test Level mentioned it identified about 30 diverse samples of xCaon — the earliest courting again to 2014 — all of which rely on HTTP protocol for command-and-manage communications.
Telemetry data analyzed by the researchers also found that the HTTP variants mostly set their sights on political entities found in Kyrgyzstan and Uzbekistan, suggesting a shift in concentrating on in latest years together with a revamped toolset.
“What is amazing in this article is how the risk actors utilized the tactic of ministry-to-ministry deception,” claimed Lotem Finkelsteen, head of danger intelligence at Check Point.
“This tactic is vicious and successful in earning anybody do anything for you and in this case, the malicious action was found at the maximum ranges of sovereignty. Furthermore, it truly is noteworthy how the menace actors benefit from Dropbox to mask on their own from detection.”
Located this posting attention-grabbing? Adhere to THN on Facebook, Twitter and LinkedIn to read a lot more unique material we post.
Some parts of this article are sourced from:
thehackernews.com

 Rethinking Application Security in the API-First Era
Rethinking Application Security in the API-First Era