3 Nigerian citizens suspected of getting customers of an arranged cybercrime team behind distributing malware, carrying out phishing strategies, and comprehensive Business enterprise Email Compromise (BEC) cons have been arrested in the metropolis of Lagos, Interpol noted yesterday.
The investigation, dubbed “Procedure Falcon,” was jointly carried out by the intercontinental police organization along with Singapore-centered cybersecurity agency Team-IB and the Nigeria Law enforcement Pressure, the principal regulation enforcement company in the region.
About 50,000 focused victims of the criminal schemes have been recognized so considerably, as the probe proceeds to track down other suspected gang members and the monetization methods utilized by the team.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Team-IB’s participation in the calendar year-lengthy procedure came as portion of Interpol’s Job Gateway, which provides a framework for agreements with picked personal sector companions and gets risk intel straight.
“The suspects are alleged to have created phishing back links, domains, and mass mailing campaigns in which they impersonated reps of organizations,” Interpol claimed. “They then applied these strategies to disseminate 26 malware programmes, spyware and remote accessibility equipment, including AgentTesla, Loki, Azorult, Spartan and the nanocore and Remcos Distant Access Trojans.”
In addition to perpetrating BEC campaigns and sending out email messages containing malware-laced email attachments, the attacks have been applied to infiltrate and watch the techniques of sufferer organizations and individuals, foremost to the compromise of at minimum 500,000 authorities and private sector providers in more than 150 countries considering the fact that 2017.
According to Team-IB, the three folks — discovered only by their initials OC, IO, and OI — are considered to be users of a gang which it has been tracking beneath the moniker TMT, a prolific cybercrime crew that it says is divided into various lesser subgroups centered on an examination of the attackers’ infrastructure and techniques.
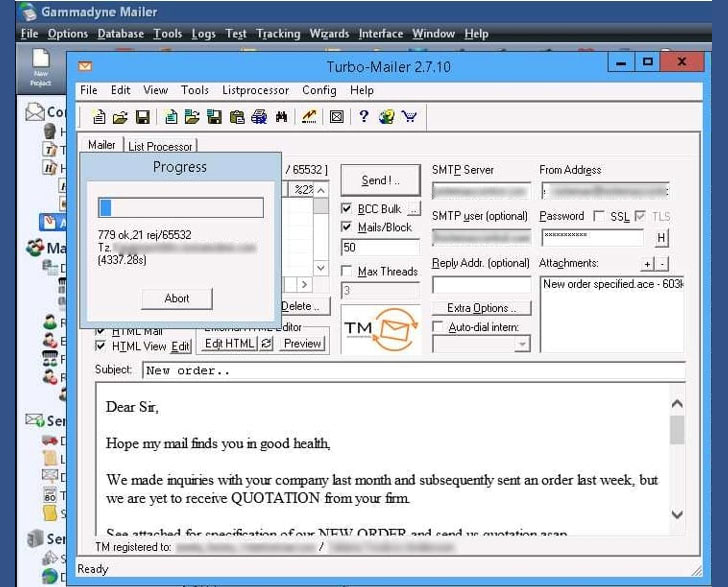
Some of their mass email phishing strategies took the kind of acquiring orders, product or service inquiries, and even COVID-19 assist impersonating legit companies, with the operators leveraging Gammadyne Mailer and Turbo-Mailer to deliver out phishing email messages. The team also relied on MailChimp to observe whether a receiver opened the concept.
The best aim of the attacks, Team-IB observed, was to steal authentication information from browsers, email, and FTP customers from corporations situated in the US, the UK, Singapore, Japan, Nigeria, among other folks.
“This team was working a well-founded felony company design,” Interpol’s Cybercrime Director Craig Jones noted. “From infiltration to cashing in, they utilised a multitude of resources and procedures to deliver utmost profits.”
Uncovered this article attention-grabbing? Adhere to THN on Fb, Twitter and LinkedIn to read through much more unique information we post.
Some pieces of this report are sourced from:
thehackernews.com


 Cloud security mapping startup Lightspeed comes out of stealth
Cloud security mapping startup Lightspeed comes out of stealth