Three dozen journalists doing work for Al Jazeera had their iPhones stealthily compromised by means of a zero-click exploit to install adware as component of a Center East cyberespionage campaign.
In a new report revealed yesterday by University of Toronto’s Citizen Lab, researchers said personalized telephones of 36 journalists, producers, anchors, and executives at Al Jazeera, and a journalist at London-based mostly Al Araby Tv set were being contaminated with Pegasus malware through a now-fixed flaw in Apple’s iMessage.
Pegasus is designed by Israeli personal intelligence organization NSO Team and will allow an attacker to entry sensitive information stored on a focus on product — all with no the victim’s information.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“The change toward zero-click on attacks by an marketplace and shoppers currently steeped in secrecy increases the probability of abuse going undetected,” the scientists claimed.
“It is additional tough […] to track these zero-click on attacks mainly because targets might not recognize just about anything suspicious on their phone. Even if they do observe a thing like ‘weird’ connect with behavior, the celebration may be transient and not go away any traces on the machine.”
The conclusions arrived to light-weight right after a single of the victims, Al Jazeera investigative journalist Tamer Almisshal, suspected his iPhone may well have been hacked and consented to have his network traffic monitored by Citizen Lab scientists applying a VPN application before this January.
The internet watchdog found that the attacks transpired between July and August of this year making use of an exploit chain it phone calls KISMET, a zero-day existing in iOS 13.5.1 that could be applied to crack Apple’s security protections.
Citizen Lab said the 36 telephones in query had been hacked by four distinct “clusters” or NSO operators with possible ties to the Saudi and the United Arab Emirates governments.
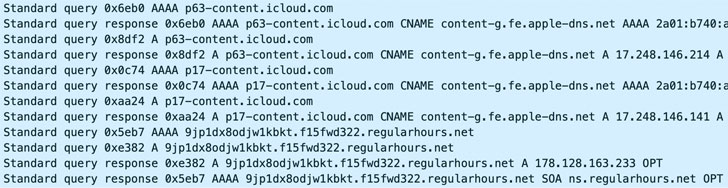
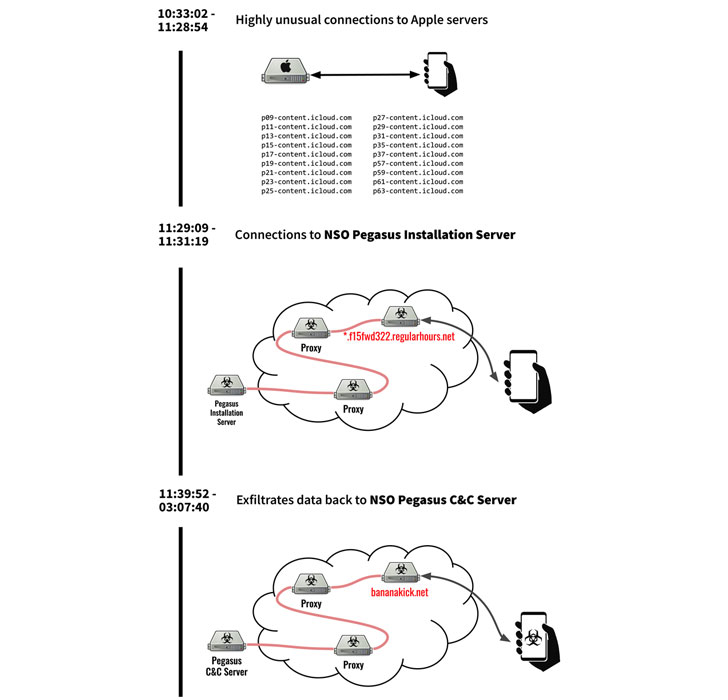
A assessment of Almisshal’s VPN logs uncovered a sudden uptick in anomalous connections to Apple iCloud servers, which the scientists surmise was the preliminary infection vector to transmit the destructive code, followed by connections to an set up server to fetch the Pegasus adware.
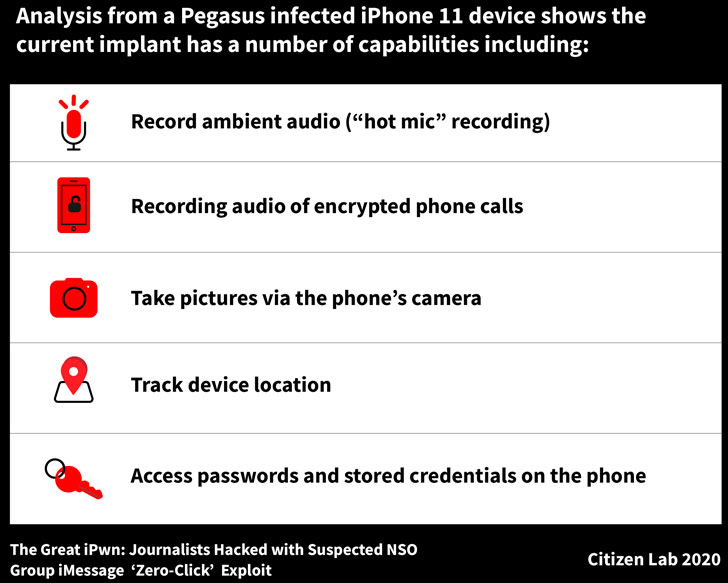
The implant arrives with the abilities to file audio from microphone and phone calls, take pictures employing the phone’s digital camera, obtain the victim’s passwords, and monitor the device’s spot.
Whilst NSO Group has regularly managed that its software program is only intended to be employed by regulation enforcement agencies to observe down terrorists and criminals, this is considerably from the 1st time the resource has been abused by various governments to spy on critics, dissidents, politicians, and other individuals of fascination.
A single of these instances concerned the shipping of the hacking resource via a formerly undisclosed vulnerability in WhatsApp, which is at the moment pursuing legal motion towards the company in a US courtroom.
“The current craze in direction of zero-click on infection vectors and more innovative anti-forensic capabilities is part of a broader market-vast shift in direction of additional complex, less detectable means of surveillance,” the scientists concluded.
“The elevated concentrating on of the media is specially about supplied the fragmented and usually ad-hoc security practices and cultures among the journalists and media outlets, and the hole involving the scale of threats and the security assets created obtainable to reporters and newsrooms.”
Located this short article exciting? Stick to THN on Fb, Twitter and LinkedIn to examine a lot more exceptional material we submit.
Some parts of this posting are sourced from:
thehackernews.com


 Does SolarWinds change the rules? The timing may matter
Does SolarWinds change the rules? The timing may matter