Facts have emerged about a new cyber espionage marketing campaign directed towards the aerospace and telecommunications industries, largely in the Middle East, with the goal of thieving sensitive details about critical assets, organizations’ infrastructure, and technology while remaining in the dark and correctly evading security alternatives.
Boston-based mostly cybersecurity firm Cybereason dubbed the attacks “Operation Ghostshell,” pointing out the use of a previously undocumented and stealthy remote access trojan (RAT) termed ShellClient that is deployed as the key spy instrument of alternative. The initial signal of the attacks was observed in July 2021 in opposition to a handpicked set of victims, indicating a really focused solution.
“The ShellClient RAT has been below ongoing improvement given that at least 2018, with numerous iterations that launched new functionalities, while it evaded antivirus resources and managed to keep on being undetected and publicly unidentified,” scientists Tom Fakterman, Daniel Frank, Chen Erlich, and Assaf Dahan said in a technical deep dive published nowadays.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

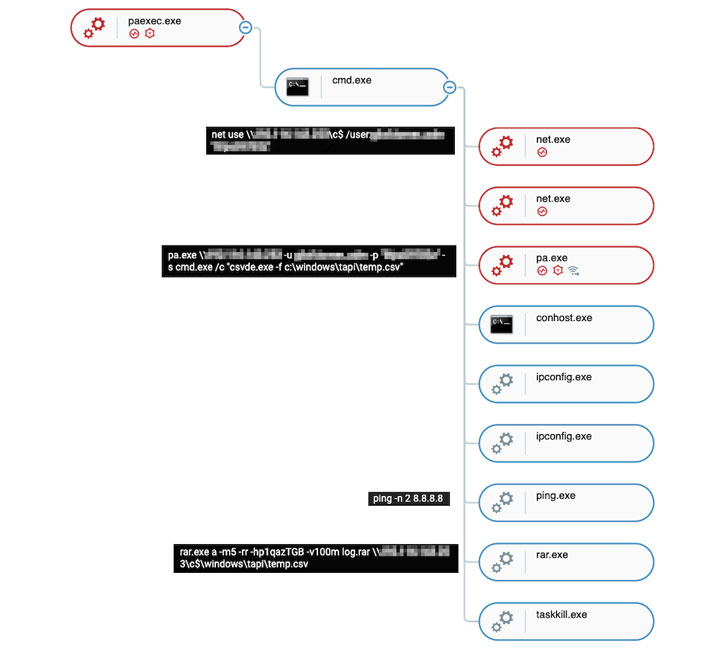
Cybereason traced the roots of this threat again to at the very least November 6, 2018, earlier working as a standalone reverse shell in advance of evolving to a sophisticated backdoor, highlighting that the malware has been beneath constant development with new options and capabilities additional by its authors. What is actually much more, the adversary at the rear of the attacks is also mentioned to have deployed an unknown executable named “lsa.exe” to complete credential dumping.
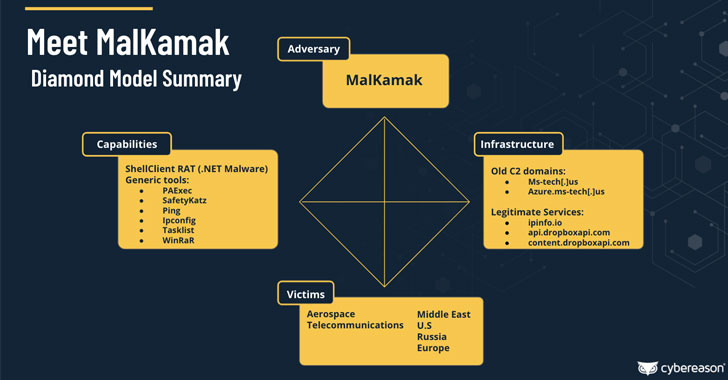
Investigation into the attribution of the cyber-attacks has also yielded an solely new Iranian danger actor named MalKamak that has been running since about the very same time period and has eluded discovery and investigation so considerably, with feasible connections to other Iranian point out-sponsored APT menace actors these kinds of as Chafer APT (aka APT39) and Agrius APT, the latter of which was identified posing as ransomware operators in an effort and hard work to conceal the origin of a sequence of details-wiping hacks in opposition to Israeli entities.
Apart from carrying out reconnaissance and the exfiltration of sensitive info, ShellClient is engineered as a modular portable executable that’s capable of carrying out fingerprinting and registry functions. Also of notice is the RAT’s abuse of cloud storage providers this kind of as Dropbox for command-and-command (C2) communications in an try to stay underneath the radar by blending in with legit network targeted visitors originating from the compromised methods.

The Dropbox storage is made up of a few folders, each and every storing facts about the infected equipment, the instructions to be executed by the ShellClient RAT, and the outcomes of individuals commands. “Every single two seconds, the sufferer equipment checks the commands folder, retrieves data files that depict instructions, parses their content, then deletes them from the remote folder and enables them for execution,” the researchers explained.
The aforementioned modus operandi mirrors a tactic adopted by one more risk actor called IndigoZebra, which was uncovered as relying on Dropbox API to shop instructions in a victim-certain sub-folder that is retrieved by the malware prior to execution.
The conclusions also get there days right after a new highly developed persistent risk dubbed “ChamelGang” was identified as driving a string of attacks concentrating on fuel, vitality, and aviation output industries in Russia, the U.S., India, Nepal, Taiwan, and Japan with the objective of stealing info from compromised networks.
Located this article appealing? Comply with THN on Fb, Twitter and LinkedIn to examine far more exceptional content we write-up.
Some elements of this article are sourced from:
thehackernews.com

 NCSC: Revoke Admin Access for BYOD Users Immediately
NCSC: Revoke Admin Access for BYOD Users Immediately