A innovative social engineering attack undertaken by an Iranian-condition aligned actor qualified believe tanks, journalists, and professors with an intention to solicit delicate information and facts by masquerading as scholars with the College of London’s Faculty of Oriental and African Scientific tests (SOAS).
Organization security agency Proofpoint attributed the campaign — termed “Operation SpoofedScholars” — to the innovative persistent threat tracked as TA453, which is also identified by the aliases APT35 (FireEye), Charming Kitten (ClearSky), and Phosphorous (Microsoft). The govt cyber warfare team is suspected to be tied to the Islamic Groundbreaking Guard Corps (IRGC).


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“Recognized targets bundled authorities in Center Eastern affairs from think tanks, senior professors from effectively-regarded academic institutions, and journalists specializing in Center Jap protection,” the scientists claimed in a technical publish-up shared with The Hacker Information. “The marketing campaign demonstrates a new escalation and sophistication in TA453’s strategies.”
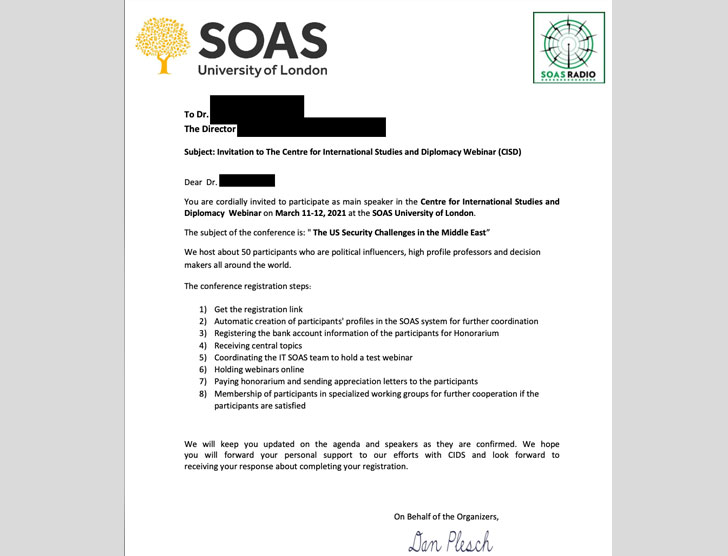
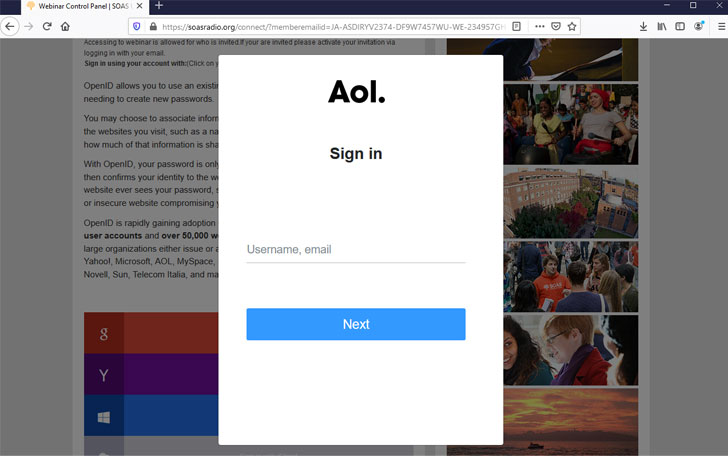
On a superior level, the attack chain associated the threat actor posing as British scholars to a team of hugely selective victims in an attempt to entice the concentrate on into clicking on a registration connection to an on-line meeting that’s engineered to seize a selection of qualifications from Google, Microsoft, Facebook, and Yahoo.
To lend it an air of legitimacy, the credential phishing infrastructure was hosted on a real but compromised website belonging to the University of London’s SOAS radio, making use of which personalised credential harvesting internet pages disguised as registration one-way links ended up then delivered to unsuspecting recipients.
At the very least in a single occasion, TA453 is said to have sent a credential harvesting email to a focus on to their personal email account. “TA453 strengthened the believability of the attempted credential harvest by employing personas masquerading as authentic affiliates of SOAS to supply the destructive backlinks,” the scientists claimed.
Some of the SOAS students who were being impersonated involved Dr. Hanns Bjoern Kendel, an affiliate professor of diplomatic scientific studies and intercontinental relations, and Dr. Tolga Sinmazdemir, a senior lecturer in political methodology.

Apparently, TA453 also insisted that the targets signal in to sign up for the webinar when the team was on line, elevating the chance that the attackers had been “scheduling on immediately validating the captured credentials manually.” The attacks are considered to have commenced at minimum given that January 2021, prior to subtly shifting their ways in subsequent phishing lures.
This is not the to start with time the threat actor has launched credential phishing attacks. Previously this March, Proofpoint in-depth a “BadBlood” campaign targeting senior medical gurus who specialized in genetic, neurology, and oncology study in Israel and the U.S.
“TA453 illegally obtained access to a web-site belonging to a earth class tutorial institution to leverage the compromised infrastructure to harvest the credentials of their meant targets,” the researchers explained. “The use of legit, but compromised, infrastructure signifies an enhance in TA453’s sophistication and will nearly absolutely be reflected in long term campaigns. TA453 proceeds to iterate, innovate, and collect in aid of IRGC assortment priorities.”
Uncovered this post interesting? Abide by THN on Facebook, Twitter and LinkedIn to read through a lot more unique articles we post.
Some parts of this posting are sourced from:
thehackernews.com


 Microsoft warns SolarWinds customers that Serv-U is under attack
Microsoft warns SolarWinds customers that Serv-U is under attack