IT and communication businesses in Israel ended up at the heart of a supply chain attack marketing campaign spearheaded by an Iranian risk actor that involved impersonating the firms and their HR staff to concentrate on victims with fake work features in an attempt to penetrate their computers and gain entry to the company’s purchasers.
The attacks, which happened in two waves in May possibly and July 2021, have been connected to a hacker group named Siamesekitten (aka Lyceum or Hexane) that has principally singled out oil, gasoline, and telecom companies in the Middle East and in Africa at the very least considering that 2018, researchers from ClearSky explained in a report revealed Tuesday.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
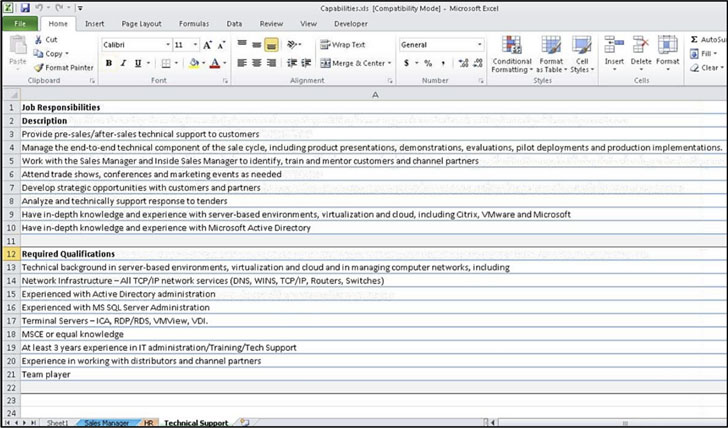
Bacterial infections carried out by the adversary commenced with determining opportunity victims, who have been then enticed with “alluring” task presents in perfectly-regarded providers like ChipPc and Application AG by posing as human methods division personnel from the impersonated companies, only to direct the victims to a phishing web-site made up of weaponized files that unload a backdoor recognised as Milan to set up connections with a distant server and down load a second-phase remote entry trojan named DanBot.
ClearSky theorized that the attacks’ target on IT and communication organizations counsel they are meant to aid provide chain attacks on their shoppers.

Besides employing lure paperwork as an first attack vector, the group’s infrastructure provided setting up fraudulent sites to mimic the corporation getting impersonated as effectively as building fake profiles on LinkedIn. The entice files, for their section, get the form of a macro-embedded Excel spreadsheet that particulars the meant job presents and a portable executable (PE) file that incorporates a ‘catalog’ of goods made use of by the impersonated firm.
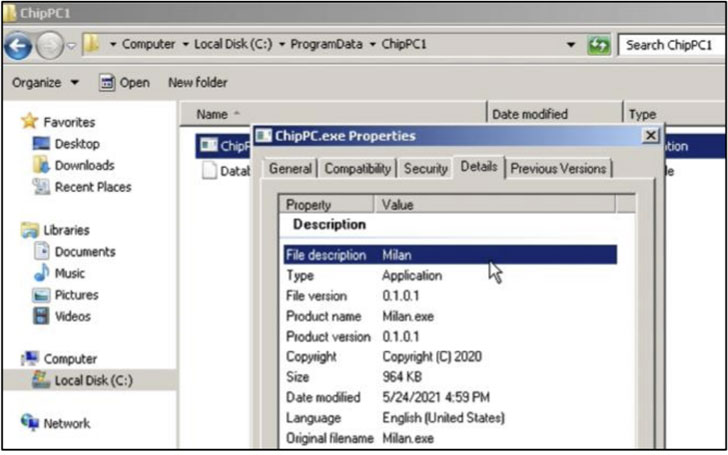
Regardless of the file downloaded by the victim, the attack chain culminates in the installation of the C++-dependent Milan backdoor. The July 2021 attacks from Israeli companies are also noteworthy for the point that the risk actor replaced Milan with a new implant referred to as Shark that’s created in .NET.
“This marketing campaign is related to the North Korean ‘job seekers’ marketing campaign, using what has become a broadly made use of attack vector in latest years – impersonation,” the Israeli cybersecurity company explained. “The group’s principal objective is to conduct espionage and make the most of the infected network to get obtain to their clients’ networks. As with other groups, it is doable that espionage and intelligence collecting are the initial methods toward executing impersonation attacks targeting ransomware or wiper malware.”
Observed this post fascinating? Observe THN on Fb, Twitter and LinkedIn to examine extra exclusive information we put up.
Some parts of this article are sourced from:
thehackernews.com

 Does a VPN Protect You from Hackers?
Does a VPN Protect You from Hackers?