A condition-sponsored danger actor allegedly affiliated with Iran has been linked to a series of focused attacks aimed at internet provider vendors (ISPs) and telecommunication operators in Israel, Morocco, Tunisia, and Saudi Arabia, as effectively as a ministry of international affairs (MFA) in Africa, new findings reveal.
The intrusions, staged by a group tracked as Lyceum, are thought to have occurred involving July and Oct 2021, researchers from Accenture Cyber Menace Intelligence (ACTI) team and Prevailion’s Adversarial Counterintelligence Crew (PACT) reported in a specialized report. The names of the victims have been not disclosed.
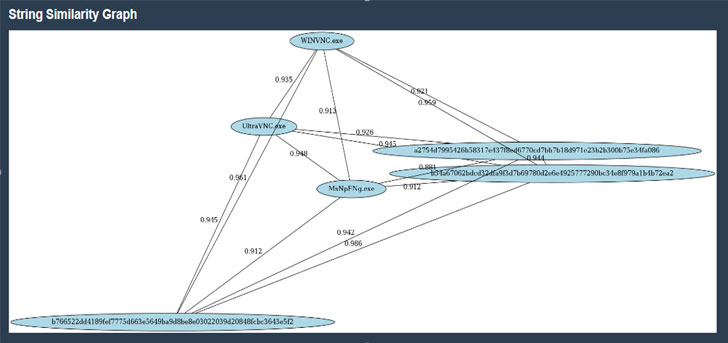
The most current revelations toss gentle on the web-based mostly infrastructure applied by Lyceum, about 20 of them, enabling the identification of “further victims and supply further visibility into Lyceum’s targeting methodology,” the scientists noted, incorporating “at least two of the discovered compromises are assessed to be ongoing regardless of prior general public disclosure of indicators of compromise.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Believed to be energetic due to the fact 2017, Lyceum (aka Hexane or Spirlin) is acknowledged to focus on sectors of strategic nationwide importance for uses of cyber espionage, although also retooling its arsenal with new implants, and growing its sights to involve ISPs and government organizations. The new and current malware and TTPs have enabled the hacking group to mount attacks versus two entities in Tunisia, Russian cybersecurity business Kaspersky disclosed final thirty day period.
The menace actor has been typically noticed applying credential stuffing and brute-drive attacks as preliminary attack vectors to receive account qualifications and achieve foothold into specific businesses, leveraging the accessibility as a springboard to fall and execute write-up-exploitation tools.
Two distinct malware families — named Shark and Milan (named “James” by Kaspersky) — are the principal implants deployed by the risk actor, every single permitting for the execution of arbitrary instructions and exfiltration of delicate data from the compromised methods to a distant attacker-controlled server.

ACTI and PACT also said it positioned beaconing from a reconfigured or most likely a new Lyceum backdoor in late Oct 2021 originating from a telecommunications business in Tunisia and an MFA in Africa, indicating that the operators are actively updating their backdoors in gentle of the latest public disclosures and making an attempt to bypass detection by security computer software.
“Lyceum will probable continue to use the Shark and Milan backdoors, albeit with some modifications, as the group has probably been ready to manage footholds in victims’ networks despite community disclosure of [indicators of compromise] affiliated with its functions,” the scientists mentioned.
Uncovered this report appealing? Observe THN on Facebook, Twitter and LinkedIn to examine extra distinctive information we publish.
Some components of this short article are sourced from:
thehackernews.com


 Palo Alto Warns of Zero-Day Bug in Firewalls Using GlobalProtect Portal VPN
Palo Alto Warns of Zero-Day Bug in Firewalls Using GlobalProtect Portal VPN