Israeli adware vendor Candiru, which was additional to an economic blocklist by the U.S. federal government this month, is stated to have reportedly waged “watering hole” attacks from substantial-profile entities in the U.K. and the Center East, new conclusions reveal.
“The victimized web sites belong to media retailers in the U.K., Yemen, and Saudi Arabia, as very well as to Hezbollah to govt institutions in Iran (Ministry of Foreign Affairs), Syria (like the Ministry of Electricity), and Yemen (including the Ministries of Interior and Finance) to internet support providers in Yemen and Syria and to aerospace/armed service technology corporations in Italy and South Africa,” ESET explained in a new report. “The attackers also created a web-site mimicking a health care trade reasonable in Germany.”
The strategic web compromises are thought to have transpired in two waves, the initially commencing as early as March 2020 in advance of ending in August 2020, and the second string of attacks starting in January 2021 and lasting right until early August 2021, when the targeted internet websites were stripped clean up off the destructive scripts.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Watering hole attacks are a kind of very specific intrusions in that they are inclined to infect a precise team of finish-consumers by backdooring web sites that customers of the group are identified to frequent with the aim of opening a gateway into their devices for comply with-on exploitation things to do.
“The compromised web sites are only made use of as a leaping-off issue to reach the ultimate targets,” the Slovak cybersecurity firm stated, linking the 2nd wave to a threat actor tracked by Kaspersky as Karkadann citing overlaps in the strategies, procedures, and methods (TTPs). The Russian business described the group as focusing on governing administration bodies and news shops in the Center East considering that at least Oct 2020.
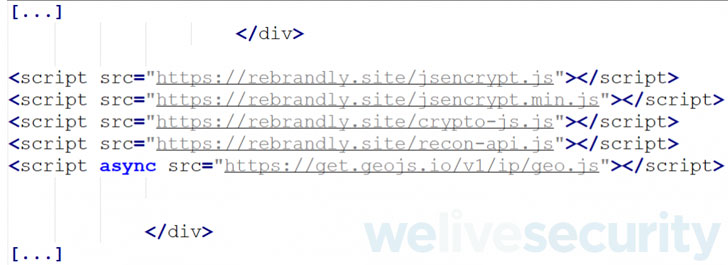
The authentic attack chains involved injecting JavaScript code into the sites from a remote attacker-managed domain that’s developed to accumulate and exfiltrated I.P. geolocation and procedure details about the sufferer device, opting to commence more only if the running technique in dilemma is possibly Windows or macOS, suggesting the campaign was orchestrated to goal computers and not mobile products. The last step led to a probable browser distant code execution exploit that enabled the attackers to hijack handle of the equipment.
The next wave observed in January 2021 was characterized by a lot more stealth, as the JavaScript modifications were being made to authentic WordPress scripts (“wp-embed.min.js”) utilised by the internet websites as a substitute of incorporating the destructive code straight to the principal HTML web page, using the process to load a script from a server less than the attacker’s regulate. What is actually additional, the fingerprinting script also went over and above harvesting method metadata to capture the default language, the listing of fonts supported by the browser, the time zone, and the listing of browser plugins.

The specific exploit and the ultimate payload delivered keep on being mysterious as but. “This demonstrates that the operators decide on to narrow the aim of their operations and that they you should not want to burn their zero-working day exploits,” ESET malware researcher Matthieu Faou mentioned.
The campaign’s one-way links to Candiru stems from the truth that some of the command-and-manage servers used by the attackers are similar to domains previously recognized as belonging to the Israeli business, not to point out feature browser-based distant code execution exploits in its arsenal, increasing the probability that “the operators of the watering holes are clients of Candiru.”
ESET famous that the attackers ceased functions at the conclusion of July 2021, coinciding with the community disclosures about Candiru relevant to the use of many zero-working day vulnerabilities in the Chrome browser to concentrate on victims found in Armenia. “It looks that the operators are using a pause, in all probability in purchase to retool and make their marketing campaign stealthier,” Faou stated. “We hope to see them again in the ensuing months.”
Found this article intriguing? Abide by THN on Facebook, Twitter and LinkedIn to read a lot more exceptional written content we write-up.
Some parts of this write-up are sourced from:
thehackernews.com


 Ghostwriter Disinformation Operation Linked to Belarus
Ghostwriter Disinformation Operation Linked to Belarus