A beforehand undocumented, financially inspired risk team has been related to a string of details theft and extortion attacks on in excess of 40 entities amongst September and November 2021.
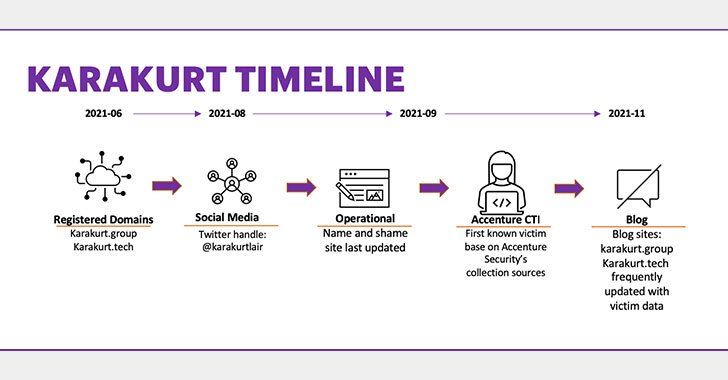
The hacker collective, which goes by the self-proclaimed name Karakurt and was to start with identified in June 2021, is able of modifying its methods and procedures to adapt to the targeted ecosystem, Accenture’s Cyber Investigations, Forensics and Response (CIFR) workforce claimed in a report posted on December 10.
“The danger group is financially inspired, opportunistic in character, and so considerably, seems to concentrate on lesser corporations or corporate subsidiaries vs . the substitute significant sport searching technique,” the CIFR crew mentioned. “Centered on intrusion evaluation to day, the menace group focuses entirely on knowledge exfiltration and subsequent extortion, fairly than the more damaging ransomware deployment.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

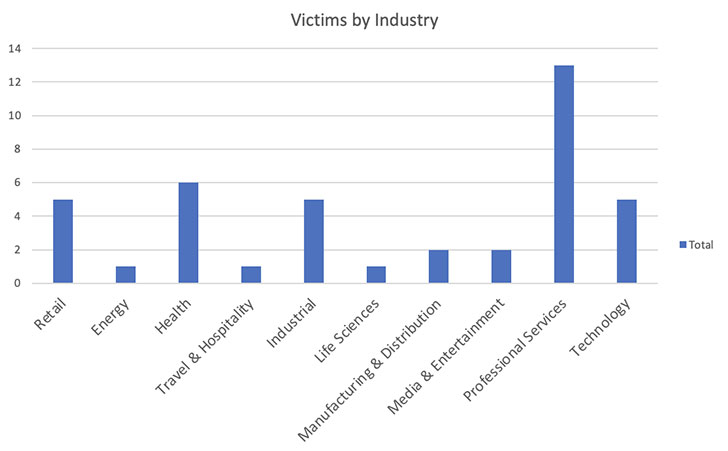
95% of the identified victims are centered in North The us, when the remaining 5% are in Europe. Qualified solutions, healthcare, industrial, retail, technology, and amusement verticals have been the most focused.
The target, the scientists pointed out, is to steer clear of drawing awareness to its destructive activities as substantially as probable by relying on residing off the land (LotL) strategies, wherein the attackers abuse respectable application and features accessible in a technique these as running system elements or set up program to shift laterally and exfiltrate data, as opposed to deploying write-up-exploitation instruments like Cobalt Strike.
With ransomware attacks getting all over the world attention in the wake of incidents aimed at Colonial Pipeline, JBS, and Kaseya as effectively as the subsequent regulation enforcement steps that have induced actors like DarkSide, BlackMatter, and REvil to shutter their operations, Karakurt seems to be attempting a distinct tack.

Fairly than deploy ransomware soon after getting first entry to victims’ internet-facing programs through respectable VPN qualifications, the actors focuses almost exclusively on info exfiltration and extortion, a move that’s much less probably to convey the targets’ company routines to a standstill and still allow Karakurt to demand a “ransom” in return for the stolen information and facts.
Other than encryption info at rest where ever relevant, businesses are suggested to turn on many-factor authentication (MFA) to authenticate accounts, disable RDP on exterior-struggling with devices, and update the infrastructure to the most up-to-date variations to avoid adversaries from exploiting unpatched techniques with publicly-acknowledged vulnerabilities.
Uncovered this report fascinating? Stick to THN on Facebook, Twitter and LinkedIn to examine additional exclusive articles we put up.
Some sections of this report are sourced from:
thehackernews.com

 Top 3 SaaS Security Threats for 2022
Top 3 SaaS Security Threats for 2022