A spear-phishing attack operated by a North Korean menace actor focusing on its southern counterpart has been found to conceal its destructive code within a bitmap (.BMP) graphic file to drop a remote obtain trojan (RAT) able of thieving sensitive facts.
Attributing the attack to the Lazarus Group based on similarities to prior ways adopted by the adversary, researchers from Malwarebytes claimed the phishing campaign commenced by distributing email messages laced with a malicious doc that it discovered on April 13.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“The actor has utilised a intelligent strategy to bypass security mechanisms in which it has embedded its malicious HTA file as a compressed zlib file in just a PNG file that then has been decompressed for the duration of operate time by changing itself to the BMP format,” Malwarebytes scientists reported.
“The dropped payload was a loader that decoded and decrypted the next stage payload into memory. The 2nd phase payload has the functionality to get and execute commands/shellcode as very well as execute exfiltration and communications to a command and command server.”
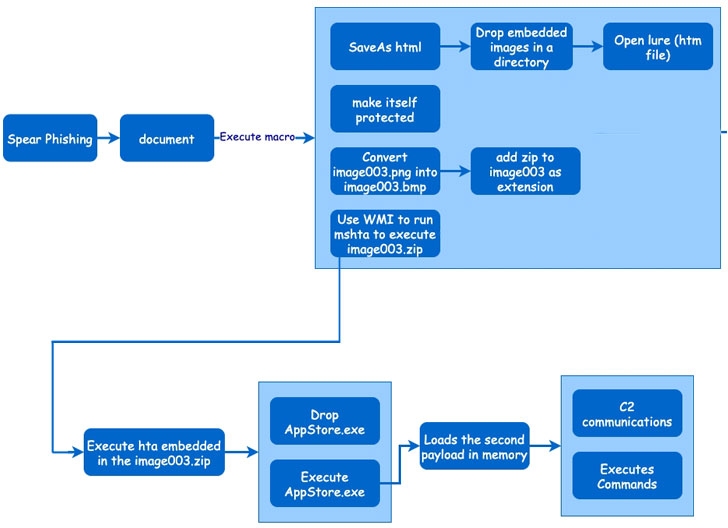
Created on March 31, 2021, the lure document (in Korean) purports to be a participation software kind for a reasonable in a person of the South Korean cities and prompts people to help macros upon opening it for the initially time, only to execute the attack code that triggers the an infection chain, ultimately dropping an executable referred to as “AppStore.exe.”

The payload then proceeds to extract an encrypted 2nd-phase payload appended to itself that is decoded and decrypted at run time, adopted by establishing communications with a remote server to receive added commands and transmit the results of all those instructions back again to the server.
“The Lazarus threat actor is one particular of the most lively and sophisticated North Korean menace actors that has targeted various nations around the world like South Korea, the U.S., and Japan in the past few of decades,” the scientists reported. “Lazarus is recognised to use new procedures and custom made toolsets in its functions to raise the success of its attacks.”
Identified this short article appealing? Stick to THN on Fb, Twitter and LinkedIn to go through far more unique articles we publish.
Some pieces of this article are sourced from:
thehackernews.com


 White House closes SolarWinds, Microsoft Exchange focus groups, signaling return to normalcy
White House closes SolarWinds, Microsoft Exchange focus groups, signaling return to normalcy