End users of Lenovo’s array of ThinkPad workstations have been warned to patch their units next the discovery of flaws that allows hackers to launch privilege escalation attacks.
It’s believed that two individual flaws can be chained alongside one another to concentrate on the ImControllerService component and change a user’s accessibility degree to a procedure, in accordance to security researchers at NCC Team.
The ImControllerService is a component present on Lenovo’s ThinkPad hardware range and controls jobs this sort of as procedure energy administration and application and driver updates.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The vulnerability can be triggered by exploiting two flaws, tracked as CVE-2021-3922 and CVE-2021-3969, impacting the way in which the ImControllerService handles the execution of highly privileged little one processes, NCC Group stated.
The ordinary running of a program will have the ImControllerService periodically start child procedures that open named pipe servers. These named pipe servers hook up to the mother or father approach in purchase to retrieve and execute the necessary XML serialised instructions.
1 of these commands is to load a plugin from an arbitrary locale on the program. The youngster process is essential to validate the digital signature of the plugin dynamic-url library (DLL) before loading and executing the file.
However, hackers are capable to hijack this method in buy to improve privileges and load any payload of their picking out on to the equipment.
The 1st vulnerability lies in the fact that the child procedure fails to check whether the source of the preliminary connection is legit. This creates a race condition that proficiently sees the hacker check out and make a relationship with the named pipe forward of the dad or mum procedure.
“An attacker utilizing high-functionality filesystem synchronisation routines can reliably acquire the race with the guardian procedure to hook up to the named pipe,” claimed NCC Team. During screening NCC Group’s evidence of strategy code by no means unsuccessful to connect to the named pipe before the father or mother company could do so.
“Due to the fact the boy or girl method does not validate the supply of the link it will begin accepting commands from the attacker right after the race situation has been exploited.”
A named pipe in a child method
NCC Group
The 2nd vulnerability is a time-of-verify to time-of-use flaw, which stems from how the kid system validates the plugin it truly is staying asked to load. When loading a DLL, the kid course of action validates its authenticity by examining if it’s signed by Lenovo.
However, attackers can use opportunistic locking (OpLocks) on a file to stall the validation system lengthy adequate for them to load their possess DLL. After the lock is unveiled, the machine will load the DLL of the attacker’s picking out which potential customers to privilege escalation.
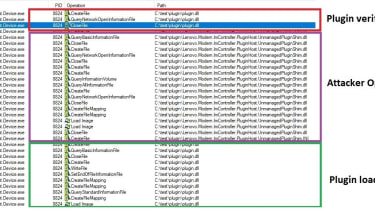
The Lenovo two-vulnerability exploit chain
NCC Group
Lenovo has produced an advisory in which it warns buyers to patch equipment to the newest IMController variation (edition 1.1.20.3). The ingredient is immediately up-to-date by the Lenovo System Interface Foundation Provider, which usually means the update can be brought on by rebooting the machine or manually restarting the ‘System Interface Foundation Service’ support, it stated.
It truly is now unclear how many Lenovo machines are thought to be afflicted globally IT Pro has contacted Lenovo for clarity.
Some sections of this short article are sourced from:
www.itpro.co.uk


 Meta: Surveillance-for-Hire Firms Hit 50,000 Victims
Meta: Surveillance-for-Hire Firms Hit 50,000 Victims