A danger actor connected with the LockBit 3. ransomware-as-a-support (RaaS) procedure has been observed abusing the Windows Defender command-line tool to decrypt and load Cobalt Strike payloads.
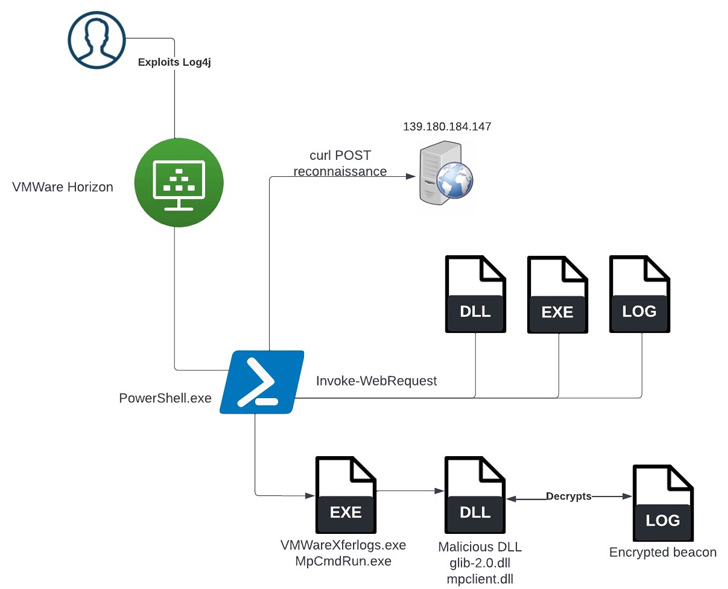
According to a report released by SentinelOne previous 7 days, the incident occurred right after obtaining first obtain by using the Log4Shell vulnerability in opposition to an unpatched VMware Horizon Server.
“The moment preliminary entry had been accomplished, the threat actors carried out a sequence of enumeration commands and attempted to operate numerous article-exploitation applications, such as Meterpreter, PowerShell Empire, and a new way to facet-load Cobalt Strike,” researchers Julio Dantas, James Haughom, and Julien Reisdorffer said.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

LockBit 3. (aka LockBit Black), which will come with the tagline “Make Ransomware Wonderful Yet again!,” is the future iteration of the prolific LockBit RaaS spouse and children that emerged in June 2022 to iron out critical weaknesses found out in its predecessor.
It’s notable for instituting what is actually the initial-at any time bug bounty for a RaaS application. Moreover showcasing a revamped leak website to title-and-shame non-compliant targets and publish extracted information, it also incorporates a new search resource to make it less complicated to obtain precise sufferer details.
The use of living-off-the-land (LotL) strategies by cyber intruders, wherein reputable program and features available in the technique are applied for write-up-exploitation, is not new and is commonly found as an try to evade detection by security computer software.
Before this April, a LockBit affiliate was located to have leveraged a VMware command-line utility referred to as VMwareXferlogs.exe to drop Cobalt Strike. What is actually different this time all over is the use of MpCmdRun.exe to attain the similar intention.
MpCmdRun.exe is a command-line tool for carrying out different capabilities in Microsoft Defender Antivirus, which include scanning for malicious computer software, gathering diagnostic information, and restoring the provider to a earlier version, among the other folks.

In the incident analyzed by SentinelOne, the preliminary accessibility was adopted by downloading a Cobalt Strike payload from a distant server, which was subsequently decrypted and loaded employing the Windows Defender utility.
“Instruments that should really get very careful scrutiny are any that both the firm or the organization’s security computer software have built exceptions for,” the researchers reported.
“Goods like VMware and Windows Defender have a substantial prevalence in the enterprise and a high utility to menace actors if they are authorized to run outside of the installed security controls.”
The conclusions come as preliminary entry brokers (IABs) are actively marketing accessibility to company networks, which includes managed provider companies (MSPs), to fellow danger actors for financial gain, in flip offering a way to compromise downstream buyers.
In May well 2022, cybersecurity authorities from Australia, Canada, New Zealand, the U.K., and the U.S. warned of attacks weaponizing susceptible managed service suppliers (MSPs) as an “first obtain vector to several victim networks, with globally cascading consequences.”
“MSPs continue to be an eye-catching offer chain target for attackers, specifically IABs,” Huntress researcher Harlan Carvey mentioned, urging corporations to safe their networks and put into action multi-factor authentication (MFA).
Found this report exciting? Abide by THN on Fb, Twitter and LinkedIn to browse a lot more unique material we submit.
Some components of this write-up are sourced from:
thehackernews.com


 Credential Stealer Malware Raccoon Updated to Obtain Passwords More Efficiently
Credential Stealer Malware Raccoon Updated to Obtain Passwords More Efficiently