A new ransomware spouse and children that emerged final thirty day period arrives with its possess bag of tips to bypass ransomware security by leveraging a novel strategy named “intermittent encryption.”
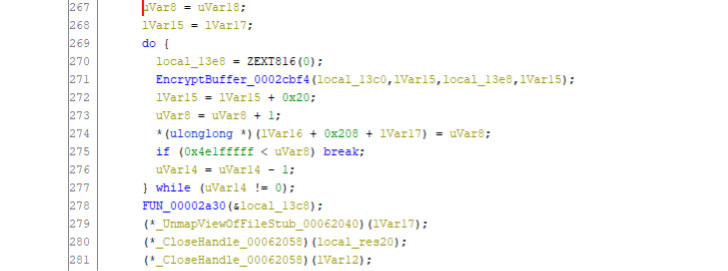
Referred to as LockFile, the operators of the ransomware has been uncovered exploiting recently disclosed flaws such as ProxyShell and PetitPotam to compromise Windows servers and deploy file-encrypting malware that scrambles only each alternate 16 bytes of a file, thereby offering it the skill to evade ransomware defences.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“Partial encryption is typically utilised by ransomware operators to pace up the encryption system and we have noticed it implemented by BlackMatter, DarkSide and LockBit 2. ransomware,” Mark Loman, Sophos director of engineering, claimed in a assertion. “What sets LockFile apart is that, unlike the other folks, it will not encrypt the initially couple blocks. In its place, LockFile encrypts each and every other 16 bytes of a doc.”
“This suggests that a file this sort of as a text doc continues to be partly readable and looks statistically like the first. This trick can be effective in opposition to ransomware security software program that relies on inspecting articles using statistical analysis to detect encryption,” Loman extra.
Sophos’ assessment of LockFile arrives from an artifact that was uploaded to VirusTotal on August 22, 2021.
At the time deposited, the malware also takes measures to terminate critical procedures linked with virtualization software and databases through the Windows Management Interface (WMI), in advance of continuing to encrypt critical data files and objects and display screen a ransomware note that bears stylistic similarities with that of LockBit 2..
The ransom note also urges the victim to get hold of a distinct email handle “[email protected],” which Sophos suspects could be a derogatory reference to a competing ransomware team known as Conti.

What is far more, the ransomware deletes alone from the process submit effective encryption of all the paperwork on the equipment, that means that “there is no ransomware binary for incident responders or antivirus computer software to come across or clear up.”
“The message below for defenders is that the cyberthreat landscape by no means stands even now, and adversaries will immediately seize each and every attainable possibility or device to start a profitable attack,” Loman reported.
The disclosure comes as the U.S. Federal Bureau of Investigation (FBI) produced a Flash report detailing the strategies of a new Ransomware-as-a-Service (RaaS) outfit recognized as Hive, consisting of a quantity of actors who are employing many mechanisms to compromise business enterprise networks, exfiltrate information and encrypt knowledge on the networks, and attempt to collect a ransom in trade for access to the decryption application.
Located this short article exciting? Comply with THN on Fb, Twitter and LinkedIn to read much more exclusive articles we put up.
Some components of this article are sourced from:
thehackernews.com


 Microsoft Warns of Widespread Phishing Attacks Using Open Redirects
Microsoft Warns of Widespread Phishing Attacks Using Open Redirects