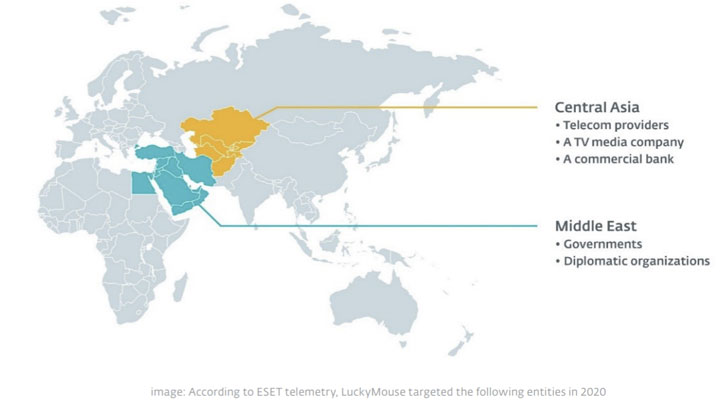
An adversary regarded for its watering gap attacks versus govt entities has been linked to a slew of recently detected intrusions targeting different companies in Central Asia and the Center East.
The malicious exercise, collectively named “EmissarySoldier,” has been attributed to a risk actor referred to as LuckyMouse, and is reported to have occurred in 2020 with the target of acquiring geopolitical insights in the location. The attacks included deploying a toolkit dubbed SysUpdate (aka Soldier) in a quantity of breached businesses, which includes authorities and diplomatic organizations, telecom companies, a Television set media enterprise, and a professional lender.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
LuckyMouse, also referred to as APT27 and Emissary Panda, is a advanced cyberespionage group that has a record of breaching various authorities networks in Central Asia and the Middle East. The actor has also been connected to cyberattacks aimed at transnational corporations these as the Worldwide Civil Aviation Firm (ICAO) in 2019 and lately attracted notice for exploiting ProxyLogon flaws to compromise the email server of a governmental entity in the Center East.
EmissarySoldier is only the newest in a sequence of surveillance endeavours aimed at the targets.
“In get to compromise victims, LuckyMouse usually utilizes watering holes, compromising websites likely to be frequented by its meant targets, ESET malware researcher Matthieu Faou explained in a report released nowadays. “LuckyMouse operators also perform network scans to come across vulnerable internet-experiencing servers run by their intended victims.”
What is actually far more, ESET also observed a several contaminated internet-struggling with devices functioning Microsoft SharePoint, which the scientists suspect happened by having edge of distant code execution vulnerabilities in the application.

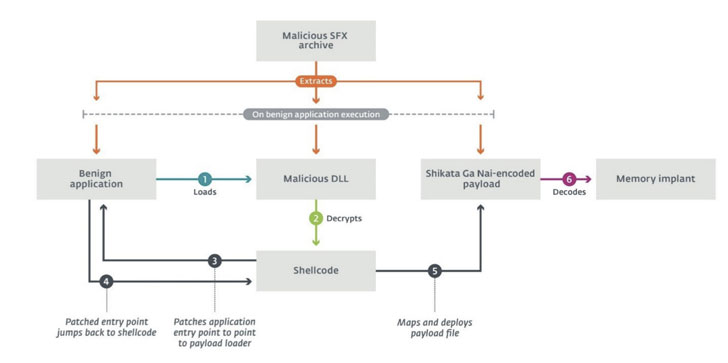
Regardless of the strategy utilized to gain an original foothold, the attack chain culminates in the deployment of tailor made submit-compromise implants, SysUpdate, or HyperBro, both of those of which leverage DLL lookup buy hijacking to load destructive payloads and thwart detection. “The trident product characteristics a legit application susceptible to DLL hijacking, a custom DLL that masses the payload, and a uncooked Shikata Ga Nai-encoded binary payload,” Faou mentioned.
For its portion, SysUpdate functions as a modular device, with just about every ingredient devoted to a specific operational goal. It will involve abusing a benign application as a loader for a malicious DLL, which in change masses the first-stage payload that eventually decodes and deploys the memory implant on the compromised procedure. Considering the fact that its discovery in 2018, the toolkit has undergone numerous revisions devoted to incorporating new functionalities, indicating that the operators are actively operating to revamp their malware arsenal.
“LuckyMouse was progressively active through 2020, seemingly going through a retooling method in which numerous characteristics ended up being incrementally built-in into the SysUpdate toolkit,” Faou claimed. “This may be an indicator that the menace actors guiding LuckyMouse are step by step shifting from applying HyperBro to SysUpdate.”
Uncovered this short article intriguing? Adhere to THN on Fb, Twitter and LinkedIn to go through a lot more exceptional content we submit.
Some areas of this post are sourced from:
thehackernews.com

 Anti-Vaxxer Hijacks QR Codes at COVID-19 Check-In Sites
Anti-Vaxxer Hijacks QR Codes at COVID-19 Check-In Sites