The Luna Moth campaign has extorted hundreds of hundreds of dollars from several victims in the legal and retail sectors.
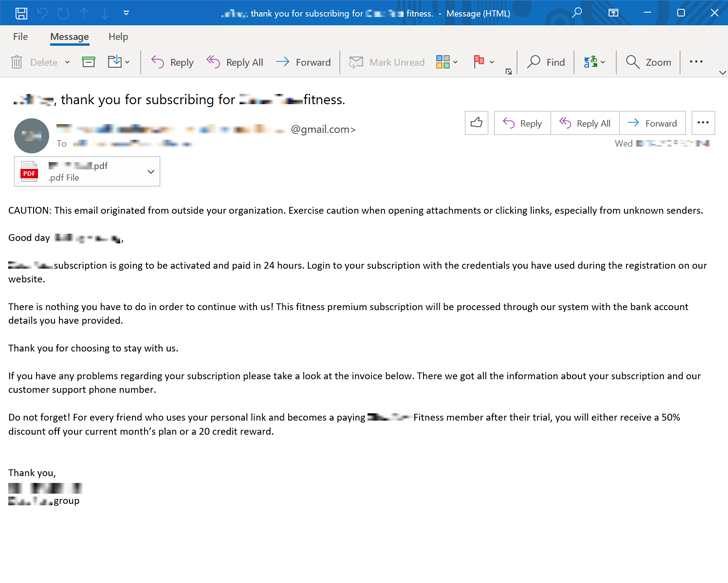
The attacks are noteworthy for using a system known as callback phishing or phone-oriented attack shipping (TOAD), wherein the victims are social engineered into building a phone simply call by means of phishing email messages made up of invoices and subscription-themed lures.
Palo Alto Networks Unit 42 claimed the attacks are the “product of a one really organized campaign,” including, “this threat actor has drastically invested in connect with centers and infrastructure that is unique to just about every target.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The cybersecurity firm described the activity as a “pervasive multi-thirty day period marketing campaign that is actively evolving.”
What is noteworthy about callback phishing is that the email messages are absolutely devoid of any malicious attachment or booby-trapped connection, making it possible for them to evade detection and slip past email defense options.
These messages ordinarily arrive with an bill that involves a phone variety that the people can connect with to terminate the intended subscription. In reality, nonetheless, the victims are routed to an actor-controlled simply call center and related to a live agent on the other end, who ends up installing a remote entry instrument for persistence.
“The attacker will then find to detect useful facts on the victim’s pc and connected file shares, and they will quietly exfiltrate it to a server they management utilizing a file transfer software,” Device 42 researcher Kristopher Russo said.
The marketing campaign may well be resource intensive, but is also technically a lot less subtle and probable to have a significantly higher success charge than other phishing attacks.
On major of that, it enables extortion without encryption, allowing malicious actors to plunder sensitive knowledge sans the need to deploy ransomware to lock the files after exfiltration.
The Luna Moth actor, also acknowledged as Silent Ransom, has grow to be an skilled of types when it will come to pulling off these kinds of techniques. According to AdvIntel, the cybercrime team is considered to be the mastermind driving the BazarCall attacks previous year.
To give these attacks a veneer of legitimacy, the adversaries, instead of dropping a malware like BazarLoader, acquire edge of reputable tools like Zoho Assist to remotely interact with a victim’s laptop, abusing the obtain to deploy other trusted program this sort of as Rclone or WinSCP for harvesting facts.
Extortion needs range from two to 78 Bitcoin based mostly on the firm specific, with the risk actor generating unique cryptocurrency wallets for just about every payment. The adversary is also claimed to give discount rates of approximately 25% for prompt payment, whilst there is no assurance that the data is deleted.
“The danger actors guiding this marketing campaign have taken great pains to prevent all non-critical tools and malware, to limit the possible for detection,” Russo stated. “Due to the fact there are incredibly several early indicators that a victim is less than attack, staff cybersecurity recognition coaching is the to start with line of defense.”
Discovered this article fascinating? Comply with THN on Fb, Twitter and LinkedIn to read through extra unique material we publish.
Some elements of this report are sourced from:
thehackernews.com


 Credential Stuffers Steal $300K from DraftKings Customers
Credential Stuffers Steal $300K from DraftKings Customers