At any time question how hackers can hack your smartphone remotely?
In a report shared with The Hacker Information now, Check out Place scientists disclosed details about a critical vulnerability in Instagram’s Android app that could have permitted distant attackers to acquire control in excess of a qualified gadget just by sending victims a specially crafted image.
What is actually far more worrisome is that the flaw not only allows attackers execute steps on behalf of the user in just the Instagram app—including spying on victim’s non-public messages and even deleting or putting up pics from their accounts—but also execute arbitrary code on the system.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
According to an advisory published by Facebook, the heap overflow security issue (tracked as CVE-2020-1895, CVSS score: 7.8) impacts all variations of the Instagram application prior to 128…26.128, which was released on February 10 earlier this calendar year.

“This [flaw] turns the machine into a software for spying on focused end users with out their understanding, as effectively as enabling malicious manipulation of their Instagram profile,” Test Position Investigate reported in an analysis posted currently.
“In either case, the attack could direct to a large invasion of users’ privacy and could have an affect on reputations — or guide to security dangers that are even far more severe.”
After the conclusions were being described to Facebook, the social media corporation dealt with the issue with a patch update produced 6 months back. The community disclosure was delayed all this time to allow the majority of Instagram’s buyers to update the application, thereby mitigating the risk this vulnerability may well introduce.
Even though Fb confirmed there ended up no indications that this bug was exploited globally, the progress is one more reminder of why it truly is crucial to hold apps up to day and be conscious of the permissions granted to them.
A Heap Overflow Vulnerability
In accordance to Check Position, the memory corruption vulnerability will allow for distant code execution that, presented Instagram’s extensive permissions to obtain a user’s digital camera, contacts, GPS, picture library, and microphone, could be leveraged to conduct any destructive action on the contaminated device.
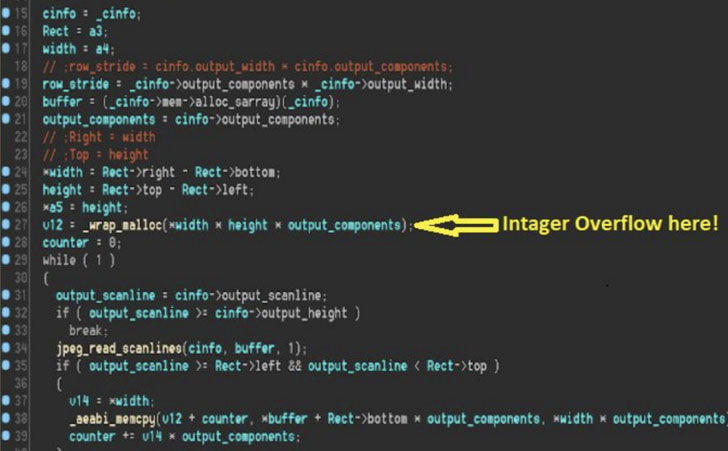
As for the flaw by itself, it stems from the way Instagram integrated MozJPEG — an open up-resource JPEG encoder library which aims to reduced bandwidth and give much better compression for photographs uploaded to the provider — ensuing in an integer overflow when the vulnerable perform in issue (“study_jpg_copy_loop”) tries to parse a destructive image with specially crafted proportions.
In undertaking so, an adversary could acquire handle above the measurement of the memory allocated to the graphic, the length of the info to be overwritten, and lastly, the contents of the overflowed memory area, in flip giving the attacker the skill to corrupt certain destinations in a heap and divert code execution.
The consequence of these types of a vulnerability is that all a negative actor needs to do is send out a corrupted JPEG impression to a target by using email or WhatsApp. At the time the recipient saves the image to the gadget and launches Instagram, the exploitation normally takes location automatically, granting the attacker total manage above the app.
Even even worse, the exploit can be employed to crash a user’s Instagram application and render it inaccessible except if it is really taken out and reinstalled all in excess of once more on the product.
If anything at all, the vulnerability is indicative of how incorporating 3rd-get together libraries into applications and companies can be a weak connection for security if the integration is not carried out ideal.
“Fuzzing the exposed code turned up some new vulnerabilities which have due to the fact been set,” Examine Point’s Gal Elbaz explained. “It is probable that, supplied more than enough effort, just one of these vulnerabilities can be exploited for RCE in a zero-click attack scenario.
“Unfortunately, it is also probable that other bugs stay or will be released in the future. As these kinds of, constant fuzz-screening of this and comparable media format parsing code, both of those in working technique libraries and 3rd-social gathering libraries, is completely important.”
Yaniv Balmas, the head of cyber analysis at Test Issue, delivered the next basic safety guidelines for smartphone buyers:
Uncovered this post exciting? Stick to THN on Facebook, Twitter and LinkedIn to study more unique content material we article.
Some parts of this article is sourced from:
thehackernews.com


 Gaming Industry Subjected to Surge in Attacks Over Last Two Years
Gaming Industry Subjected to Surge in Attacks Over Last Two Years