A few JavaScript libraries uploaded to the formal NPM offer repository have been unmasked as crypto-mining malware, at the time once again demonstrating how open-source program package repositories are starting to be a valuable focus on for executing an array of attacks on Windows, macOS, and Linux methods.
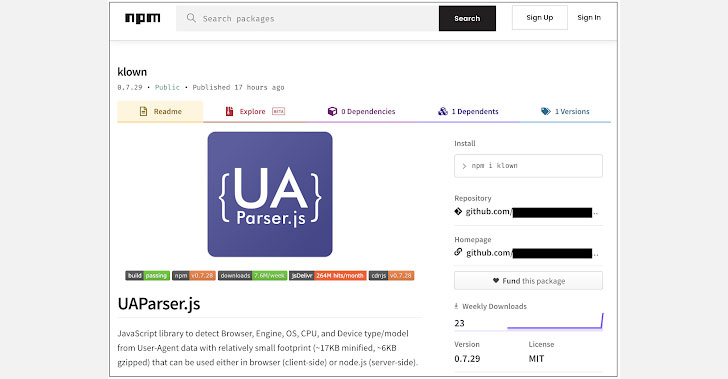
The destructive packages in dilemma — named okhsa, klow, and klown — ended up published by the identical developer and falsely claimed to be JavaScript-based mostly consumer-agent string parsers built to extract components details from the “User-Agent” HTTP header. But unbeknownst to the victims who imported them, the creator hid cryptocurrency mining malware inside of the libraries.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The negative actor’s NPM account has because been deactivated, and all the three libraries, every single of which have been downloaded 112, 4, and 65 instances respectively, have been eliminated from the repository as of October 15, 2021.
Attacks involving the three libraries worked by detecting the recent operating method, right before continuing to run a .bat (for Windows) or .sh (for Unix-based mostly OS) script. “These scripts then down load an externally-hosted EXE or a Linux ELF, and execute the binary with arguments specifying the mining pool to use, the wallet to mine cryptocurrency for, and the amount of CPU threads to make use of,” Sonatype security researcher Ali ElShakankiry mentioned.
This is considerably from the initially time brandjacking, typosquatting, and cryptomining malware have been uncovered lurking in computer software repositories.

Previously this June, Sonatype, and JFrog (formerly Vdoo) determined malicious deals infiltrating the PyPI repository that secretly deployed crypto-miners on the influenced machines. This is notwithstanding copycat packages named immediately after repositories or components utilized internally by significant-profile tech businesses in what is actually recognized as dependency confusion.
Discovered this report fascinating? Adhere to THN on Facebook, Twitter and LinkedIn to read more special information we publish.
Some elements of this report are sourced from:
thehackernews.com


 Threat Actors Abusing Discord to Spread Malware
Threat Actors Abusing Discord to Spread Malware