A focused phishing marketing campaign aimed at the aviation business for two decades may well be spearheaded by a danger actor working out of Nigeria, highlighting how attackers can carry out small-scale cyber offensives for extended periods of time though remaining less than the radar.
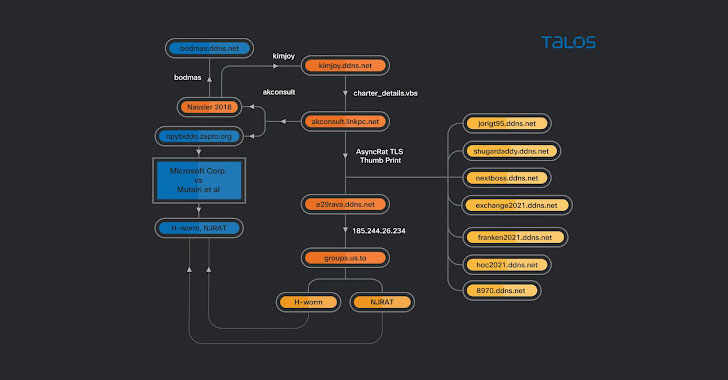
Cisco Talos dubbed the malware attacks “Procedure Layover,” setting up on preceding exploration from the Microsoft Security Intelligence team in May 2021 that delved into a “dynamic campaign concentrating on the aerospace and journey sectors with spear-phishing emails that distribute an actively designed loader, which then delivers RevengeRAT or AsyncRAT.”
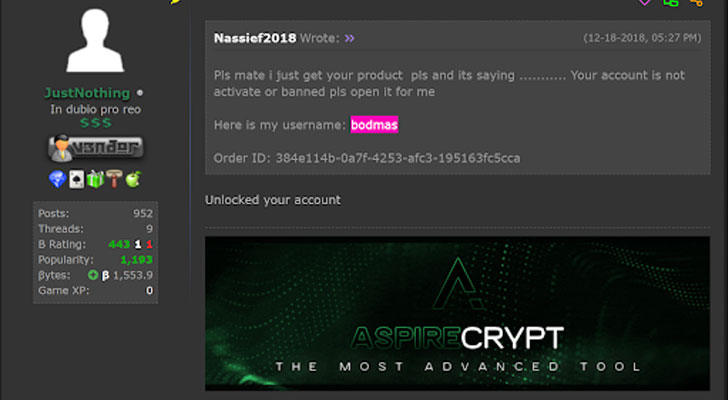
“The actor […] isn’t going to seem to be technically sophisticated, utilizing off-the-shelf malware since the starting of its activities without producing its personal malware,” scientists Tiago Pereira and Vitor Ventura reported. “The actor also buys the crypters that allow the use of these malware without the need of remaining detected, during the several years it has used various unique cryptors, generally acquired on on the internet community forums.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The risk actor is considered to have been energetic at minimum because 2013. The attacks include e-mails made up of certain entice files centered about the aviation or cargo marketplace that purport to be PDF data files but url to a VBScript file hosted on Google Push, which finally sales opportunities to the delivery of remote obtain trojans (RATs) like AsyncRAT and njRAT, leaving corporations susceptible to an array of security pitfalls. Cisco Talos reported it located 31 diverse aviation-themed lures dating all the way back to August 2018.
Further more assessment of the activity linked with various domains used in the attacks present that the actor weaved numerous RATs into their strategies, with the infrastructure made use of as command-and-control (C2) servers for Cybergate RAT, AsyncRAT, and a batch file which is applied as element of a malware chain to obtain and execute other malware.
“Many actors can have confined technical understanding but nevertheless be equipped to operate RATs or info-stealers, posing a substantial risk to significant firms given the appropriate circumstances,” the scientists said. “In this situation, […] what appeared like a basic marketing campaign is, in fact, a continual operation that has been lively for three several years, targeting an whole industry with off-the-shelf malware disguised with various crypters.”
Uncovered this report intriguing? Comply with THN on Fb, Twitter and LinkedIn to go through far more exceptional content we publish.
Some areas of this post are sourced from:
thehackernews.com

 Australia, UK, and US Announce Security Partnership
Australia, UK, and US Announce Security Partnership