A Mac malware campaign concentrating on Xcode builders has been retooled to incorporate aid for Apple’s new M1 chips and grow its characteristics to steal private information and facts from cryptocurrency applications.
XCSSET arrived into the highlight in August 2020 soon after it was observed to unfold by using modified Xcode IDE jobs, which, on the developing, were being configured to execute the payload. The malware repackages payload modules to imitate respectable Mac applications, which are in the end liable for infecting area Xcode jobs and injecting the major payload to execute when the compromised task builds.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
XCSSET modules arrive with the capabilities to steal credentials, capture screenshots, inject destructive JavaScript into internet sites, plunder person data from different applications, and even encrypt documents for a ransom.
Then in March 2021, Kaspersky researchers uncovered XCSSET samples compiled for the new Apple M1 chips, suggesting that the malware campaign was not only ongoing but also that adversaries are actively adapting their executables and porting them to run on new Apple Silicon Macs natively.
The most current investigation by Development Micro demonstrates that XCSSET carries on to abuse the growth model of the Safari browser to plant JavaScript backdoors onto internet websites through Common Cross-internet site Scripting (UXSS) attacks.
“It hosts Safari update deals in the [command-and-control] server, then downloads and installs packages for the user’s OS variation,” Craze Micro researchers explained in an examination revealed on Friday. “To adapt to the recently-launched Major Sur, new offers for ‘Safari 14’ had been extra.”
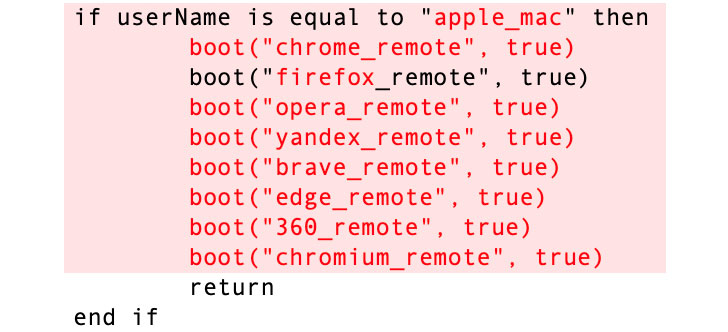
In addition to trojanizing Safari to exfiltrate info, the malware is also known for exploiting the distant debugging mode in other browsers these as Google Chrome, Brave, Microsoft Edge, Mozilla Firefox, Opera, Qihoo 360 Browser, and Yandex Browser to have out UXSS attacks.

What is extra, the malware now even attempts to steal account details from numerous internet websites, which include cryptocurrency trading platforms Huobi, Binance, NNCall.net, Envato, and 163.com, with talents to swap the deal with in a user’s cryptocurrency wallet with people less than the attacker’s control.
XCSSET’s method of distribution by way of doctored Xcode jobs poses a significant menace, as impacted developers who unwittingly share their perform on GitHub could pass on the malware to their customers in the sort of the compromised Xcode initiatives, leading to “a provide-chain-like attack for end users who rely on these repositories as dependencies in their own projects.”
Identified this article exciting? Adhere to THN on Facebook, Twitter and LinkedIn to go through far more exclusive written content we post.
Some areas of this write-up are sourced from:
thehackernews.com


 ICO Issued Over £42 Million in Fines Last Year
ICO Issued Over £42 Million in Fines Last Year